Russ White of ‘net work comments:
Throughout the last several months, I’ve been building a set of posts examining securing BGP as a sort of case study around protocol and/or system design. The point of this series of posts isn’t to find a way to secure BGP specifically, but rather to look at the kinds of problems we need to think about when building such a system. The interplay between technical and business requirements are wide and deep. In this post, I’m going to summarize the requirements drawn from the last seven posts in the series.
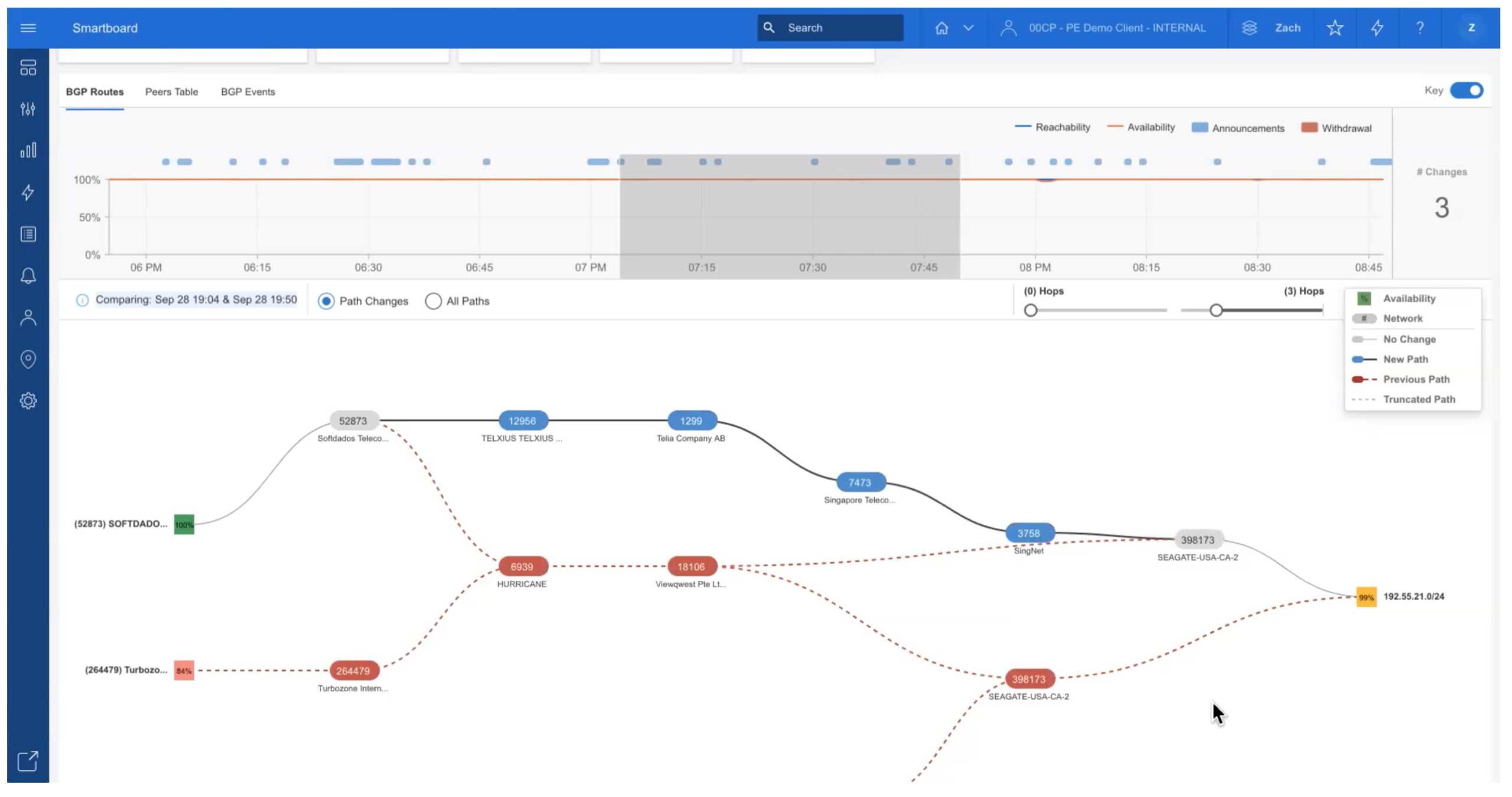
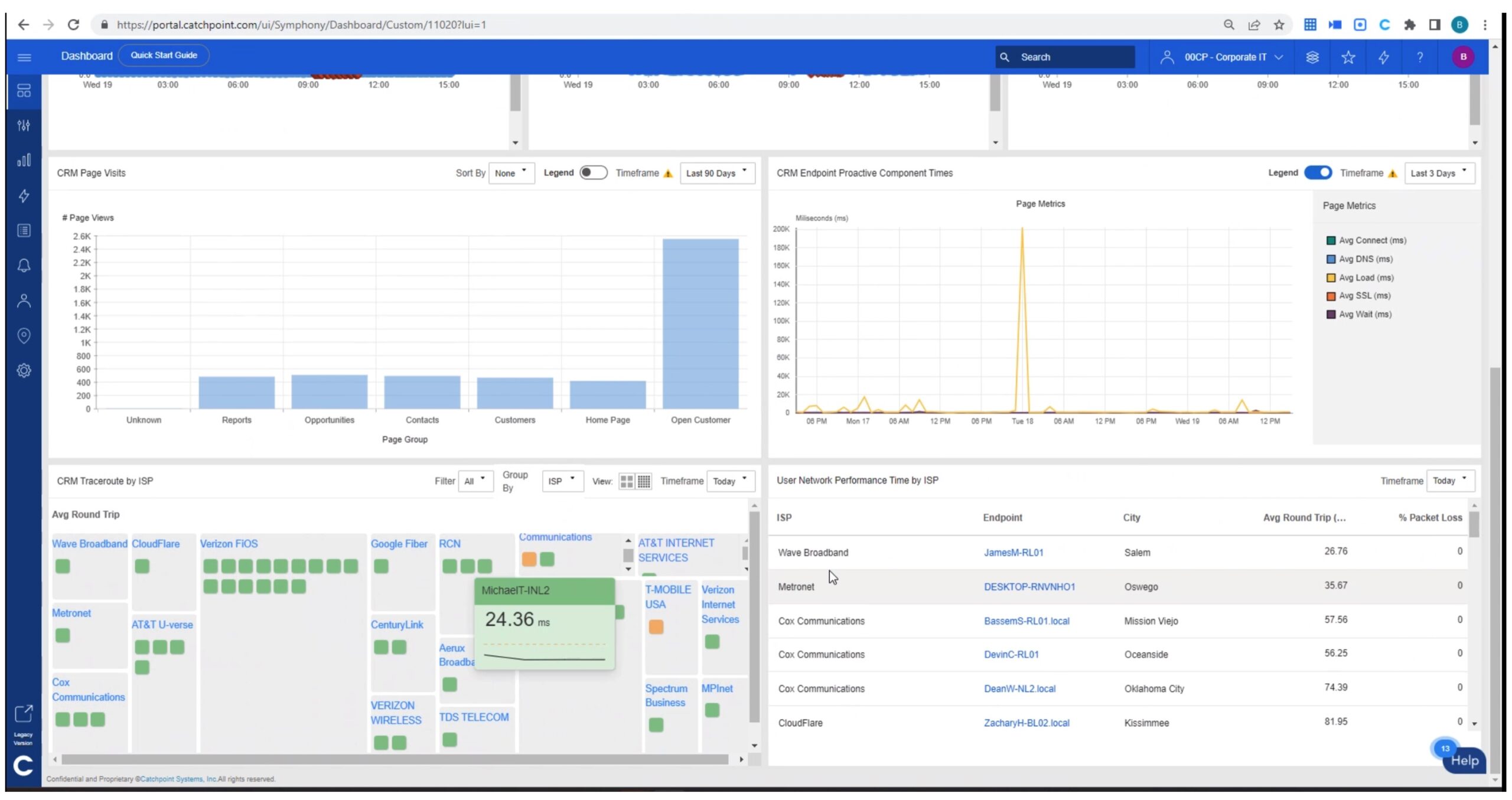
Some great thoughts on BGP from Russ. The need to secure BGP is huge given how much trouble it can cause when it’s hijacked or used for nefarious purposes.
Read more at: Securing BGP: A Case Study (8)