Tech companies are one-upping each other in the custom silicon game. In this Gestalt IT Tech Talk...
Exclusives
Gestalt IT Exclusives are original long-form posts written by the Gestalt IT team and published here first. Exclusives are highlighted in our weekly Gestalt News email. Sign up today, or follow us on Twitter!
Aligning IT and Security to Drive Long-Term Organizational...
In this Ignite Talk from Edge Field Day, Sulagna Saha discusses Brian Knudtson's presentation on...
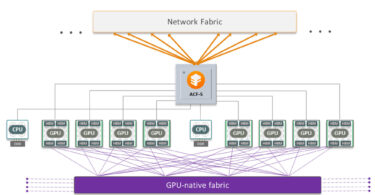
A Different AI Networking Focus with Enfabrica
Building networks for AI is expensive. What you need is a way to better utilize your GPU resources...
Overcoming Cognitive Biases Standing in the Way of Professional...
In this Ignite Talk article from the Edge Field Day event, Sulagna Saha reviews Jim Czuprynski’s...
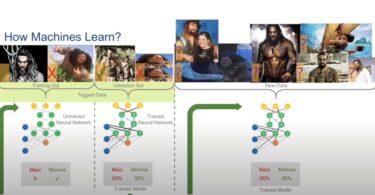
Generative AI – Risks and Rewards with Gina Rosenthal
In this Ignite Talk article from Edge Field Day, Sulagna Saha discusses Gina Rosenthal's...
The Truth behind SaaS Data Recovery with W Curtis Preston
With most SaaS services used in businesses, backup and recovery is a rare addition. In this Gestalt...
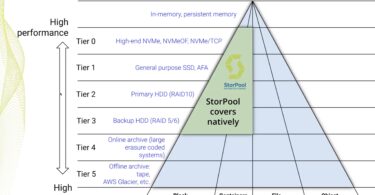
StorPool Tightens Data Protection in StorPool v21
In this exclusive article, Sulagna Saha discusses StorPool's plan to tighten data protection with...
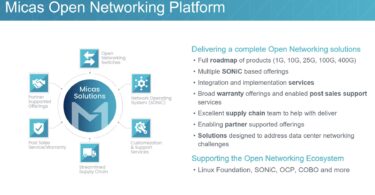
Transitioning to Open Networking, One Step at a Time, with Micas...
In this exclusive article, Sulagna Saha discusses how Micas Networks is helping businesses...
Inside the Exciting World of 3D Printing, with Erik Ableson
3D printing, in the recent years, has played a major role in meeting demands for individualized...
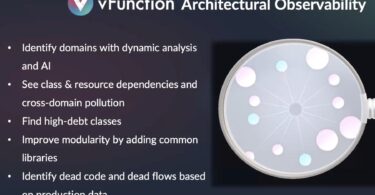
Finding and Fixing Architectural Tech Debt in Applications with...
In this exclusive article, Sulagna Saha discusses vFunction's Observability Platform and how it...
Meet W. Curtis Preston, aka Mr. Backup
Presenting W. Curtis Preston, known to many as Mr. Backup. Preston is the host and creator of The...
Meet Mikael Korsgaard Jensen, Technology Specialists Team Lead...
In this Meet the Delegate interview, Stephen Foskett sits down with Mikael Jensen, the Technology...
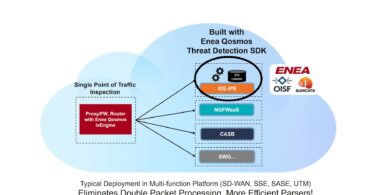
Preventing Spoofing and Other Cloaked Attacks with Enea Qosmos...
In this exclusive article, Sulagna Saha disusses how Enea's Qosmos Threat Detection SDK prevent...
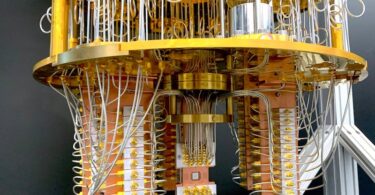
Post-Quantum Migration with DigiCert
Post-quantum cryptography is closer than you think. With the public release of the NIST finalists...
Meet Matt Tyrer, Founder and Chief Analyst at the Competitive...
Meet Matt Tyrer, the Founder and Chief Analyst at the Competitive Corner. Born and raised in Iowa...