When you think of IoT, what do you think of? Odds are good it’s probably some kind of consumer gadget, like a thermostat or a lightbulb. Perhaps it’s even some kind of doorbell or security camera or another piece of invisible infrastructure. But I’d be willing to be whatever you thought of was small and fixed in place.
The reality of IoT, especially outside the home, is much more varied. We’re starting to see IoT enabling large manufacturing machines on production floors. We’ve also seen an explosion of IoT-enabled services for delivery vans and law enforcement vehicles. These kinds of IoT applications certainly aren’t as exciting as a smart thermostat, but they accomplish the same goals. It’s all about bringing intelligence to a device that formerly didn’t have it.
But how do you retrofit IoT intelligence into a press machine the size of a garage? Or find a way to incorporate a mobile router into a police care filled to the brim with devices already? You need to find a way to add something to make the whole thing work properly. And keep everything secure at the same time. Because adding a device to the network opens the attack surface to all kinds of heretofore unknown vectors for problems.
Rock the Cradle
While I was at RSA I had the opportunity to sit down with Todd Kelly, the Chief Security Officer at Cradlepoint. He told me all about the IoT platforms that Cradlepoint has been building for what they term “high value” IoT devices. This includes things like manufacturing machines and law enforcement vehicles. Cradlepoint wants to ensure that these critical assets are not only able to take advantage of the benefits of IoT but stay secure in the process.
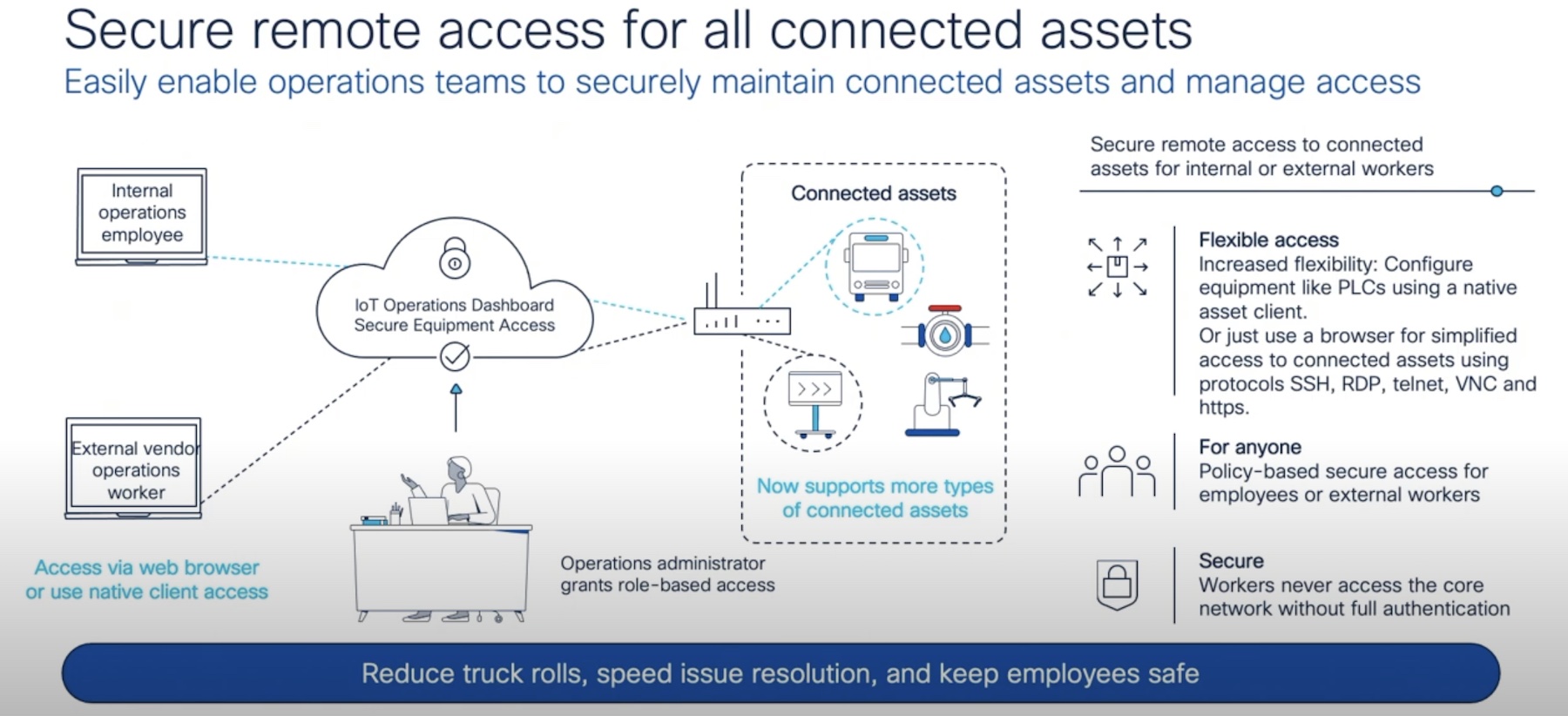
One way they’re able to do that is by having a single platform for management and security of those assets. The same dashboard that enables you to install and configure a mobile router in a SWAT van, for example, also allows you to see the status of that device and what the traffic profile looks like from a vulnerability perspective. You can detect things that might be trying to attack your endpoint and prevent malware on the inside from getting out.
You may not think that’s a big deal until you realize that gaining access to these devices when they’re brought online is a huge win for malicious hackers and criminals. Could you imagine gaining access to a secure law enforcement officer (LEO) database? Being able to pull up criminal records and other identifying information? Or, in the case of factory equipment being able to lock the machines down and hold them for ransom? We’ve already seen this kind of thing happening with NotPetya and Maersk last year. Could you imagine how damaging it could be for a manufacturer if they lost control of their equipment and couldn’t produce product?
The secondary aspect of Cradlepoint’s delivery of enhanced IoT edge security is how it can also secure smart devices already in place. Think about kiosk machines like RedBox for example. These devices are already able to call home to validate credit card data and customer information. But they could also be hacked and dispense product inappropriately if someone were enterprising enough. But installing Cradlepoint edge routers in front of those devices you can instantly increase the security posture of the device without the need to overhaul the operation of the kiosk. The connections become secure without the need to modify anything beyond plugging in a couple of extra wires. And the manageability you gain from the unified dashboard means you can instantly see when something is amiss and correct it without having to dispatch a tech.
Bringing It All Together
IoT isn’t always about beautiful consumer-based designs. It’s not about handy gadgets that make people’s lives easier. For the enterprise, IoT is about easing management of devices and making things work better and faster for a skilled workforce. It’s also about doing this in a way that keeps those devices from being compromised when they’re attached to any network. That means you need a solution that will prevent your enterprise IoT devices from getting hacked while still allowing them to work as they should. Cradlepoint has a great line of solutions that can help you out with this very conundrum and do it in a way that keeps both your operations and security teams happy.
If you’d like to learn more about Cradlepoint and their line of security and IoT-related devices, make sure to check out http://Cradlepoint.com/