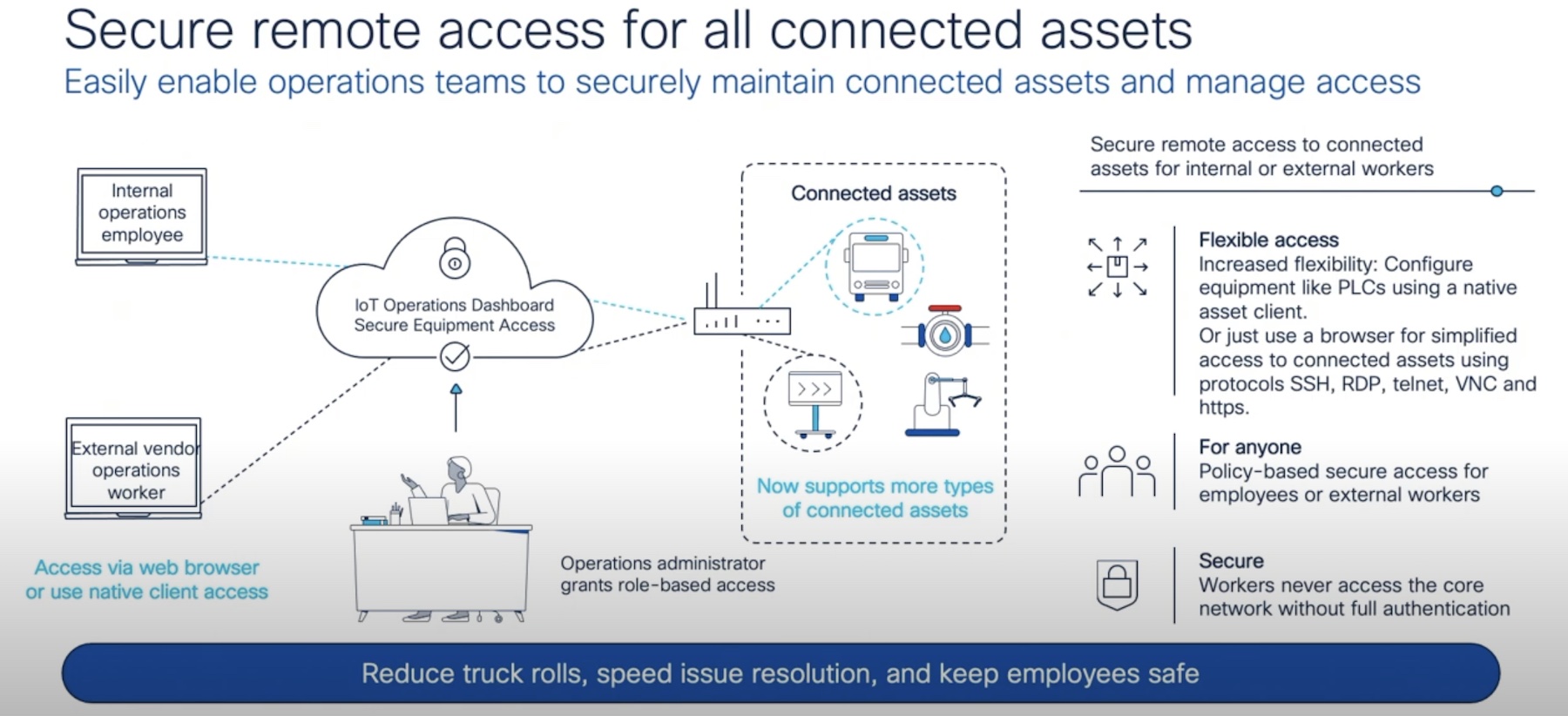
One of the hardest parts of building any security infrastructure is dealing with exceptions. For every device that can run security agents and be monitored via API, you’re also going to have devices that are unmanaged and all but invisible to most security platforms. As the number of Internet of Things (IoT) devices increases in enterprises that lack of visibility is going to be even harder to manage. How can you secure something you have no access to?

With IoT, the question is even harder. That’s because these unmanaged devices are also very difficult to secure under the best of circumstances. Expensive IoT commercial devices do have bigger processors and more memory than thermostats and other inconspicuous emplacement devices. But even the CPU and RAM in an insulin pump or industrial hygrometer are supposed to be dedicated to the purpose of the device. Getting an agent to run in the free space on one of these devices could impair their operation. And in mission-critical IoT places, that could literally mean the difference between life and death.
We have to start thinking about how we secure these devices from a different perspective. I liken it to some of the puzzles that make people think outside the box by giving them constraints they can’t modify. Relatively simple problems quickly become complex once you introduce some complicated existing conditions. Instead of assuming that you have full control of the network you have to work around things you can’t see or touch.
The Invisible Hand
During RSA 2020, I had a great opportunity to sit down for a few minutes with Mike Nelson, VP of IoT Security for DigiCert. He’s one of the people at the forefront of trying to solve these issues with IoT devices. With the rise of more complicated hacking techniques and the ability to insert clever little hacks into device firmware, how can you be sure that you’re not dealing with someone that has the financial backing and desire to cause massive damage to your IoT devices?
Attacks like Stuxnet were just the vanguard of the kinds of hacking that we’re talking about. Imagine being able to invade a repository for firmware images for medical equipment, for example. Perhaps you destroy them like a traditional hacker might. Or, maybe you introduce the kinds of systemic issues that cause intermittent failure. Maybe you’re an agent of a foreign government intent on creating a little havoc in the healthcare system. You could even be a rival company looking to get your hands dirty and profit off the inevitable reputation damage that comes from failing devices. No matter what your angle, being able to attack the firmware of IoT devices is a great way to create some hard-to-trace issues.
Mike and I talked about the things that DigiCert is helping to do to ensure that IoT devices have more security without trying to make them run agents or additional software. Since DigiCert is a digital certificate company, you can guess they are leading the way in providing things like code signing certificates for critical IoT devices to ensure that firmware that is loaded on the device is verified and trusted. That’s incredibly important as the number of devices is set to explode in the next 3-5 years. If you think you’re swimming in IoT now, just wait until it gets faster, cheaper, and more functional.
DigiCert ONE is the platform that can be used to control PKI for a variety of devices, including IoT. Imagine the nightmare scenario of being told that a shipment of new insulin pumps showed up from the manufacturer that IT had pressed them into service without your approval. Where did they come from? Can you trust them? With DigiCert ONE you can load identity information for each device and ensure that it matches the expectation of what it should look like. Did the identity cert come from the company? If so, allow it on the network. If not, lock it down until an investigation can be done. This kind of transparency can help you save lives and save your organization from costly lawsuits in the future.
Bringing It All Together
The future of IoT is more than just microsegmented networks and isolated control systems. We have to build integrated solutions that help us see everything in the network, even the invisible stuff we’ve never worried about before. As things get smarter and more likely to be vectors for attack or infection, we need to make sure we can audit and verify those devices before they have the opportunity to become something unintended. Primary security isn’t enough. We have to look at secondary options to ensure our invisible devices are safe and sound.