Cryptography is the secret sauce that keeps our lives livable in today’s world. Think about all the secure websites and applications that you use to do business or share information. All of those secure transactions work on the principle of encrypted data. We’ve seen massive campaigns to crack encryption keys or steal seed values for tokens. It’s a cat-and-mouse game to keep our security one step ahead of increasing computing power. But what if the race is already lost?
Quantum Leap
 I had the chance to sit down with Avesta Hojjati, the head of R&D for DigiCert during the RSA Conference. I asked him about some of the problems that he was looking at in security right now. I fully expected the answer to be around certificate management or complexity issues. I was blown away when he started telling me about post-quantum cryptography and what it really means for the future of encryption protocols.
I had the chance to sit down with Avesta Hojjati, the head of R&D for DigiCert during the RSA Conference. I asked him about some of the problems that he was looking at in security right now. I fully expected the answer to be around certificate management or complexity issues. I was blown away when he started telling me about post-quantum cryptography and what it really means for the future of encryption protocols.
Modern encryption and hashing protocols are built on algorithms like the RSA cryptographic algorithm. Without getting super technical about the method used to create a specific key, it all comes down to multiplication. Take two large, random prime numbers and multiply them together. Take that result and use it as the basis for creating the key. For key sizes bigger than 1024 bits, reverse engineering the key out of that resulting product is next to impossible. This is the basis of all cryptography today. It works because computers are really good at multiplication and really bad at factoring. Even being given the product you can’t find out how you arrived there without the factors.
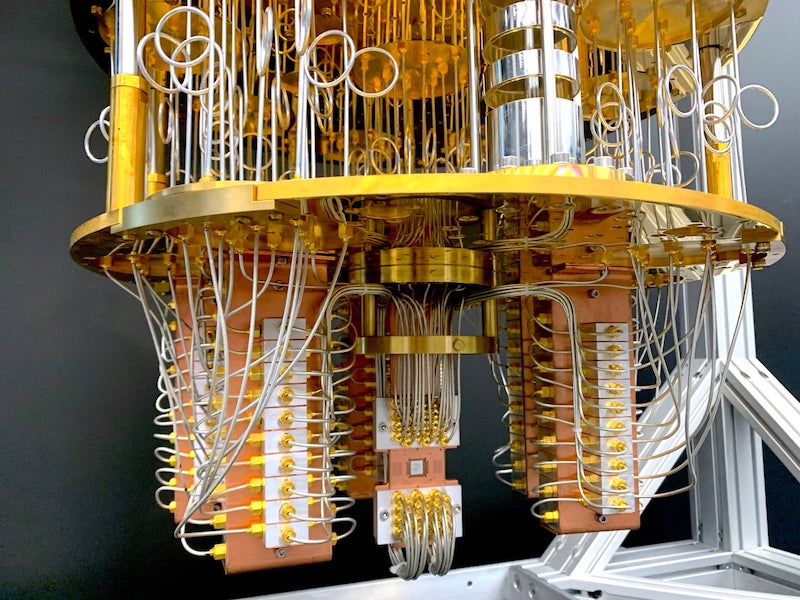
This is where a quantum computer comes into play. Where modern CPUs are efficient at multiplication, quantum computers excel at factoring. By their very nature, they can understand the states of the data they are fed. Thanks to an algorithm developed by Peter Shor, quantum computers with sufficient processing power, referred to as qubits, would be able to factor the RSA algorithm immediately. This means they could slice through the complicated mathematics that pre-quantum cryptography relies on and leave almost every modern cryptographic algorithm completely vulnerable.
So, why haven’t we heard about this yet? The good news is that a sufficiently powerful quantum computer hasn’t been built yet. Once it does get built, the underpinnings of SSL/TLS and other security mechanisms are in doubt. And, just like British Intelligence was motivated to break the Enigma machine in WWII, so too are modern scientists determined to break RSA. That’s where the research that Avesta and his team are doing comes into play.
Building A Better Mousetrap
This is an issue that has been high on the radar of the US government since 2016. That’s when NIST put out the call for a post-quantum crypto algorithm to defeat the eventual rise of a quantum computer. DigiCert first started working on this solution in 2017. They’ve partnered with several companies, including Microsoft Research, Gemalto, and ISARA to start working on algorithms that will satisfy the NIST requirements.
According to Avesta, the race is on. The deadline is the first powerful quantum computer that can cut through the noise and decrypt data. Given the number of low power IoT devices that are now being used as sensors, for example, could you imagine what would happen if someone were able to figure out how to crack RSA public key encryption and start modifying data? Because you could eliminate the encryption complexity on the fly, you could easily insert invalid data without anyone being the wiser. Think about the value you could destroy or corrupt with the ability to invisibly modify data and keep the cryptographic signature the same!
The DigiCert team has been putting a lot of work in on the problem and they’ve made it past the first round of NIST selection and onto the second which was announced earlier this year. They’re also trying to make sure they have solutions for pre and post quantum crypto as well, with the end goal being a combined certificate that can satisfy both needs and provide for a smooth transition mechanism between the two algorithms. Since all transitions take time, the need for lead time before the assembly of the hypothetical quantum supercomputer is critical.
Bringing It All Together
I loved learning more about what DigiCert Labs is working on with regard to the post-quantum crypto future. It’s critical that we understand the problem and how to transition away from flawed algorithms as soon as we can. Given the number of people that still rely on MD5 hashes and DES encryption, you can see how challenging this can be. Avesta and his team are doing a great job of preparing us for the eventual end of the RSA algorithm.
If you’d like to learn more about the initiatives that DigiCert is working on, make sure to visit http://DigiCert.com. You can also email [email protected] to find out more and perhaps even find out how you can contribute!