The subscription model is one of the hottest trends around. What began with meal-kit businesses and fitness training centers has fast assumed the scale of an economy with its adoption by bigger industries. The newest party to join the as-a-service revolution are the big guns in automobile. With the intention to dynamize revenue, certain manufacturers are now offering in-cabin features as-a-service for the very first time.
In these times of connected products and services, ensuring trust along the path from a secure device to a deployed service takes more than just buying the best solutions or hiring the brightest minds. Cybersecurity in the era of connected IoT devices is more complex than that.
Micron took a shot at demystifying IoT security. At the recent Security Field Day event in California, Micron presented the Authenta Platform. Labeled the “Silicon-to-cloud trust platform”, Authenta delivers high levels of protection to IoT devices by securing the lowest layers of device software. Micron’s vision with it? Affordable and pervasive protection for all IoT solutions that uses silicon.
Securing IoT in the Subscription Era
As the subscription trend takes hold, a lot of businesses transition from straightforward manufacturers to subscription-based businesses. Over the past few years, a host of smart IoT solutions has emerged to bring to life this everything-as-a-service revolution.
But digital evolution is a double-edged sword. From one perspective it has made IoT solutions smarter, more powerful than was believed possible in such a short amount of time. But from another perspective, it has caused devices and services to deploy into new and unknown environments, posing high levels of security risks to the integrity of these solutions.
Connected devices and services are at a higher risk of compromise as they pass through a diverse supply chain before launching into an ecosystem that is open, fragmented and vulnerable. At any stage of this journey, a bad actor can implant a malware and compromise a device in a heartbeat. OEMs are constantly battling with these looming threats, all the while searching for ways to seal systems end to end from manufacturing through all of the product life.
A Logical Course of Action
Looking at the big picture of cybersecurity, Micron sees IoT security becoming more and more critical in the coming days. Already a leader in the flash memory space, Micron uses its cognizance with silicon to iron out the kinks in modern cybersecurity with a simplistic and logical approach – protection at the roots to the ends.
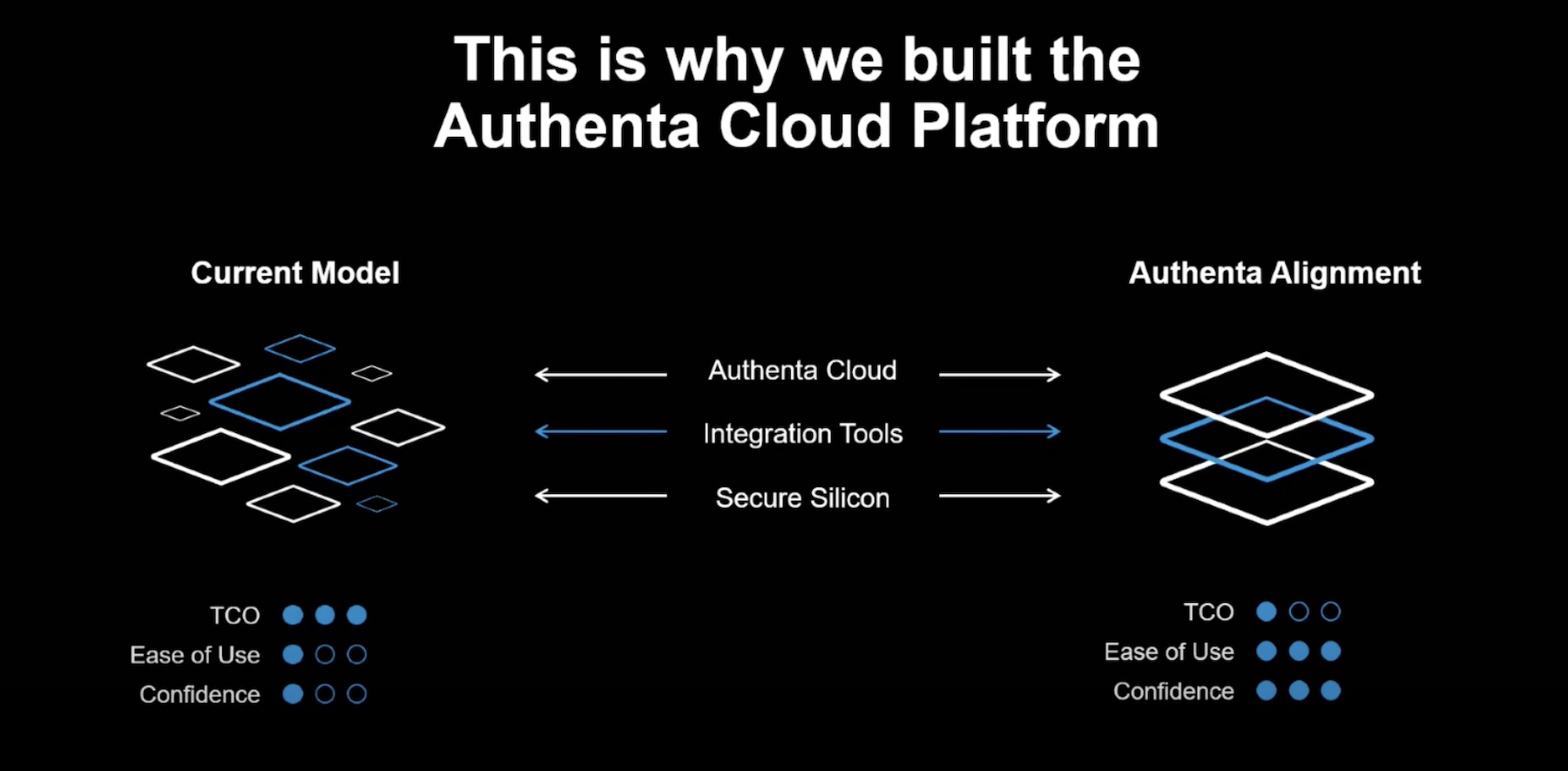
Led by the vision of a secure foundation for IoT, Micron built a silicon-based security-as-a-service solution – the Authenta platform. Authenta embeds security at three levels – hardware, integrations and delivery ensuring health and integrity of IoT systems from the factory through the to the end of the product life.
Authenta builds security from the ground up with the hardware root of trust that enables silicon-based security activation and control. Further up, it enables manufacturers to securely hand over the flash control to third parties. In the final steps, it provides secure, zero-touch onboarding to cloud. With the Authenta Key Management Service, users can manage and secure deployed services throughout their lifecycle. That’s all the bases covered.
A Closer Look at the Authenta Platform
Micron showcased the Authenta platform at the recent Security Field Day event. Luis Ancajas, Director of Authenta Product Line at Micron, outlined the drivers and gave an overview of the solution. In a later customer blueprint presentation, TrustiPhi explained Authenta’s capabilities and discussed its use cases.
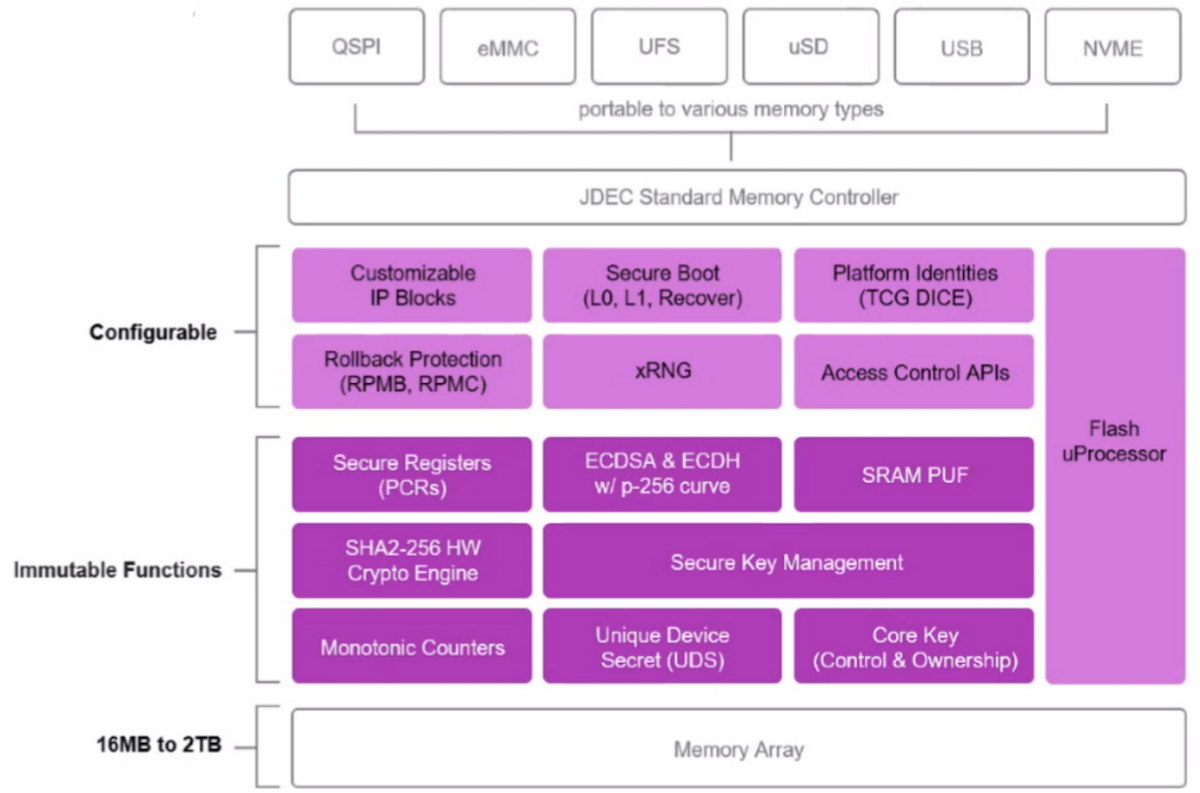
Micron Authenta is a triple-tiered platform that has security woven into its fabric. At the base, Authenta enables always-on security directly in the silicon thus establishing trust in provenance and preventing attempts of tamper at the silicon level. With a combination of device-specific identity and in-memory secure boot, it ensures that devices are authenticated with the host irrespective of the run-time environment.
Authenta is a zero-component solution that requires no additional hardware component. Its security features are built natively into the flash memory. The Authenta-activated memory deploys in the standard sockets and is compatible with a variety of endpoints. Hardware root of trust provides enhance system-level protection while bringing down the cost of engineering.
But where standard hardware security systems save keys and credentials in the hardware itself, Authenta saves them in the cloud. Through a cloud-based Key Management Service (KMS), Authenta saves all secrets securely in cloud keeping them accessible for management throughout the product lifecycle. A trusted partner can avail this feature to validate that they’ve received the product in its mint state.
Above the Authenta root of trust is a suite of integration tools “that can be used to bridge the gap between early manufacturing and deployment, and through the life cycle of the platform,” explained Ari Singer, CTO of TrustiPhi in his presentation. The integration suite allows users to activate security, control endpoints, and configure and personalize. But most importantly, it enables OEMs to transfer keys and certificates via a separate chain which makes a quiet supply chain attack a lot less likely.
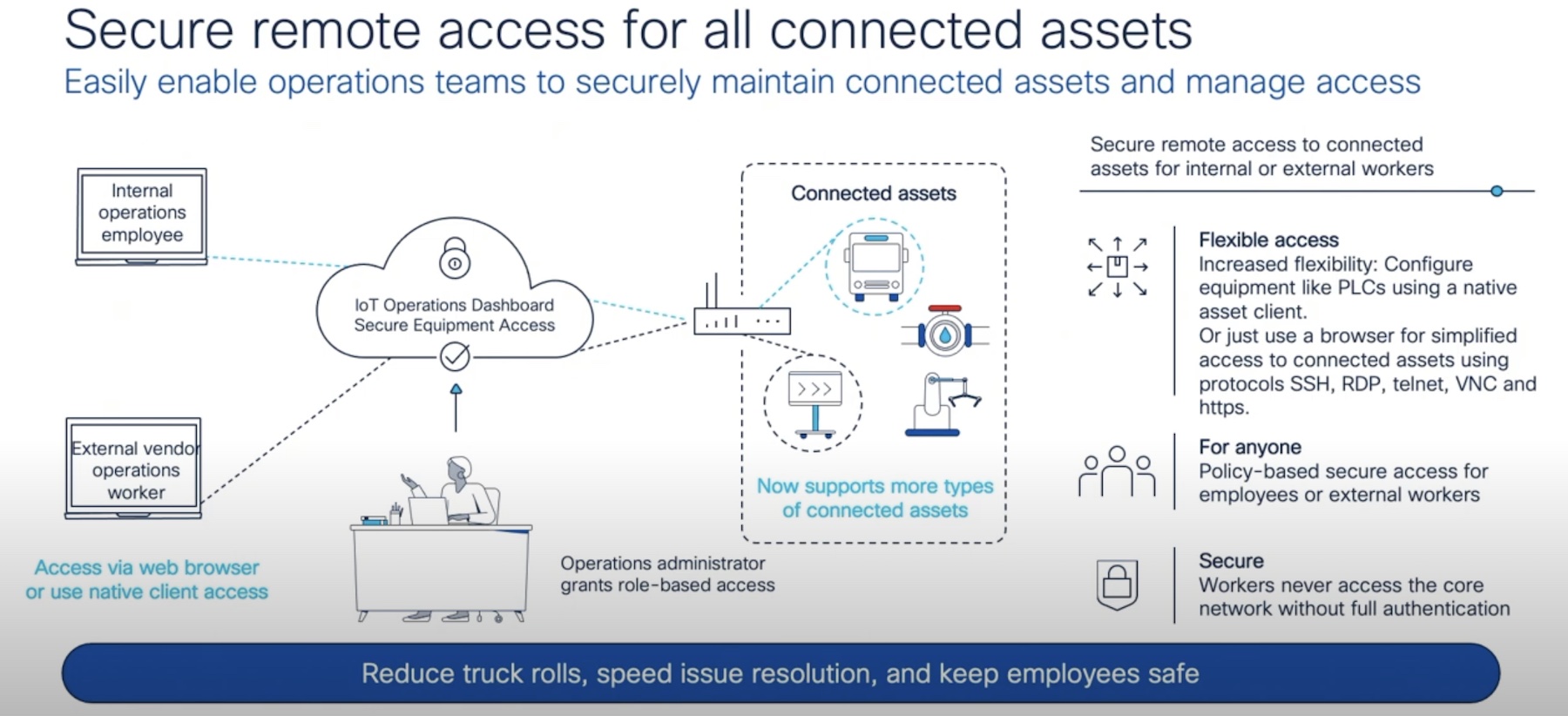
The third piece of it, Authenta Cloud, is the delivery of the product or service in a secure cloud ecosystem. “ Our cloud has the ability to send keys and credentials, platform identities, services so that it helps in the facilitation of all of the systems going out into the field,” explained Ancajas.
Wrapping Up
Micron’s Authenta makes a compelling Zero Trust IoT security platform. With intelligent implementation of security technologies, it provides protection at silicon level, and through the supply chain from manufacturing to ownership transfers to deployment. Micron’s vision with it was to build a solution that preserves and proves the integrity of the IoT systems at delivery and Authenta does more than that. It gives users the peace of mind that the items they are deploying in their environments are not corrupt or compromised on the way to them, but also gives OEMs the ability to protect their products from malicious supply chain attacks, thus ultimately empowering the subscription business.
For more information on the Authenta platform, be sure to check out Micron’s other presentations on it from the recent Security Field Day event.