An outstanding presentation not only relays the message in the intended way, it also stays with the...
Author - Sulagna Saha
Preventing Attack Escalation with Network Segmentation – A...
An integral component of the zero-trust architecture is microsegmentation. In this Gestalt IT Tech...
KubeCon 2023 with Michael Levan
KubeCon has steadily gained traction in the IT community over the years. In this Gestalt IT Tech...
Qlik Unveils a New Look while Making Strategic Adjustment to...
Qlik's rebranding is more than a new look, it's a statement. Data analytics has penetrated...
Kubernetes, Beyond the Hype with Jon Hildebrand
Kubernetes is said to be the go-to tool for all of IT. In this Gestalt IT Tech Talk, host Stephen...
Busting the Silo Mentality with DevOps with Matthew Allford
DevOps, if adopted right, can end years of productivity issues in IT. In this Gestalt IT Tech Talk...
Understanding Data Sovereignty with Nathan Bennett
Data sovereignty is one of the burning issues of our time. In this Gestalt IT Tech Talk recorded at...
Shifting Left to Cast a Wide Safety Net with Leon Adato
There is a growing consensus that security needs to shift left in the software development...
Improving the Accuracy of Domain-Specific Information of Large...
This article follows Ben Young’s journey of building a chatbot web interface for Veeam knowledge...
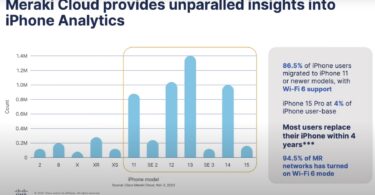
Next-Level Client Wi-Fi Visibility with Cisco’s Three-Way...
In this article, Sulagna Saha discusses data-driven enterprise Wi-Fi monitoring and optimization...