As companies accelerate efforts to transition to cloud, one topic has surfaced as a number one priority – data sovereignty. In the digital age, where every click and every swipe produce a byte of data somewhere, there’s growing pressure to keep data under sovereign control.
In one of the Tech Talks recorded at the recent Cloud Field Day event in Silicon Valley, this became the topic of discussion. Nathan Bennett, a veteran from the cloud world, tapped into the conversation of data sovereignty and explained what it means for the average private sector companies.
For most people, data sovereignty brings to mind the idea of cordoning off digital data within a country’s geographic perimeter. Is that the entirety of it? We asked Bennett.
“Geo proximity is definitely the first step if you are an entity within the US government or the EU who wants to make sure that the data is stationed within those sovereignties,” said Bennett.
Gone are the days when data could live borderlessly. Under new regulations, users residing outside the country lose access to certain app features depending on the law of the land.
But data sovereignty in the cloud era far exceeds just the concept of locality. “The idea of sovereignty within the clouds is a pretty big topic, especially within the public sector and other areas for compliances and security reasons. Within the sovereign cloud, it’s about where is the data. But most importantly, who has possible access or access adjacent to that data?” Bennett stated.
The Debate over Access and Control
Multi-tenancy that is the cornerstone of the cloud business model – the idea that tenants can share the same hardware stack, services and even databases for their applications for reduced cost – is in contradiction with the first requirement of data sovereignty – fine-grained control and access.
A key concern among enterprises is who’s has access to their data, and with the scale of today’s network, it could be anybody. “It’s rock skipping on the top of the lake, where it’s not necessarily about the lake, but the rocks skipping. Verifying all of the different security aspects of that rock, where it’s skipping and then securing those skips,” explained Bennett.
Although the conversation around data sovereignty is getting real, and there are obvious security risks and control limitations in multi-tenant environments, it is not the kind of thing that small and mid-size companies should lose their sleep over yet, said Bennett.
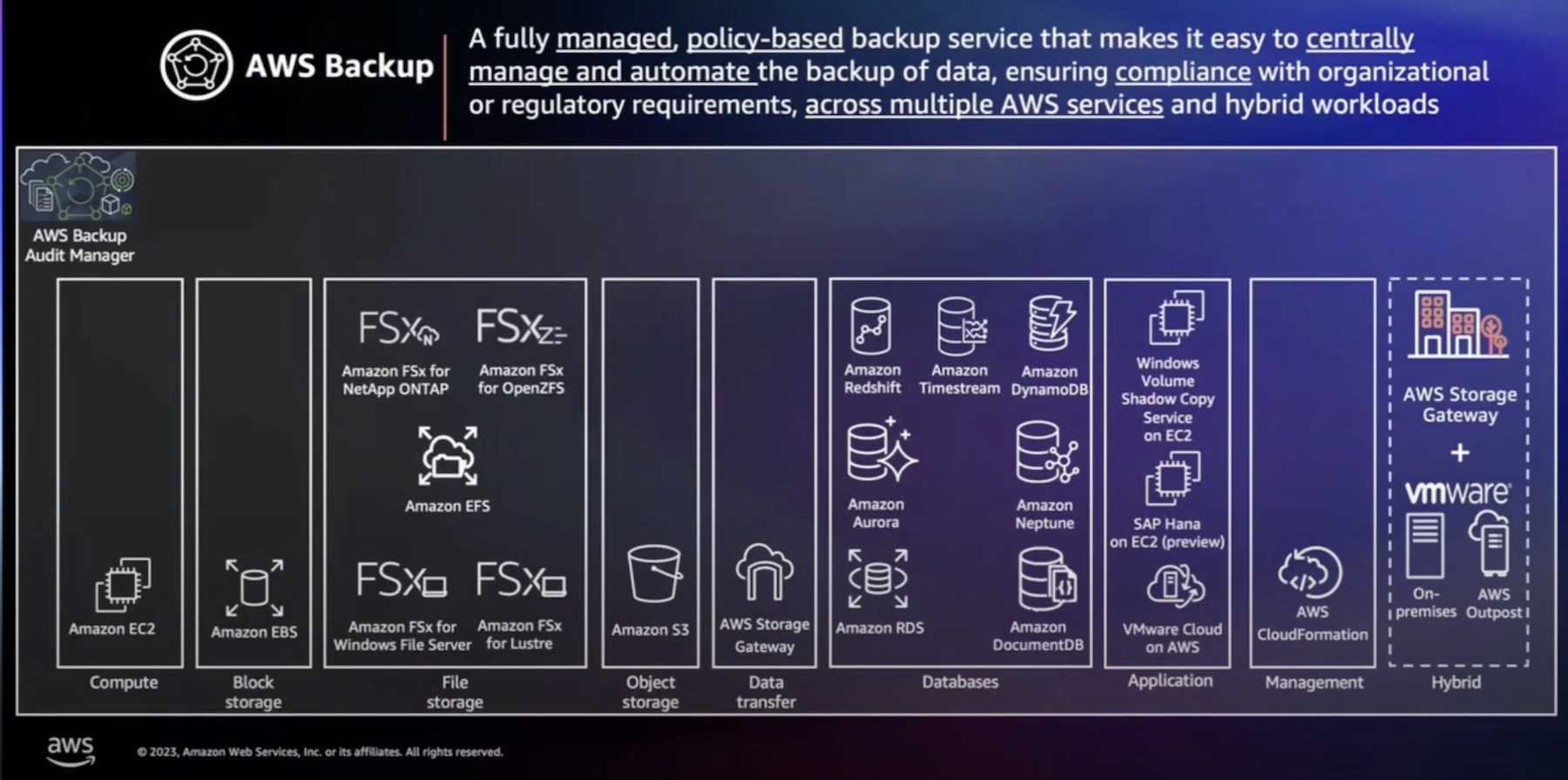
“If you are concerned, there are multiple different services that are already prevalent within the clouds to afford you resiliency and durability of your data to maintain that security.”
At the other end of the spectrum are the public sector companies that need to maintain high levels of compliance like FedRAMP, and Impact Level, commonly refer to as IL4, IL5, IL6. These enterprises come under intense regulatory scrutiny, and as a result demand the highest levels of ownership.
The Rise of Sovereign Cloud Regions
Hyperscalers like AWS, GCP and Azure already have sovereign cloud regions separate from the commercial cloud. The market is exponentially expanding. “We are seeing additional players in the game that are popping up and utilizing colocations to create sovereign clouds specifically for customers. We are also seeing individual agencies building sovereign clouds that they can themselves use specific to their use cases.”
For all intents and purposes, these sovereign clouds are like private datacenters, but with the full set of public cloud features. Built for the regulated industries that have to meet the highest level of compliance and security, these clouds are sacrosanct, and cannot be accessed by small or mid-size companies.

But at the base level, both commercial and sovereign clouds provide software-defined compute, network and storage. “If you hit an API and it goes to no man’s land where it has to then create a ticket for some guy to go and build something, that’s not a cloud that anybody would want to use. You need specific automation behind it and orchestration in order to get an instance within a set amount of time based off of SLAs,” Bennett said.
As awareness around data sovereignty mounts, ownership and control will become more central to commercial cloud services. “There are specific hardware capabilities coming down the pipe that might actually change the way that we view the tenancy issue,” said Bennett.
And to quote Bennett, “The cloud operating model is rapidly transforming, and that operating model can work for an SMB, as well as the DoD that has to maintain the highest level of compliance”.
For more, be sure to watch the full interview, and other Tech Talks from the recent Cloud Field Day event.