VMware NSX is a powerful multifaceted solution with a lot of dimensions. So much so that it’s actually a little hard to get a single understanding of it. That’s not to say that it is a bloated or convoluted offering, merely ambitious in scope. If you’re going to make a platform for network virtualization and security, it’s kind of go big or go home.
But when talking about NSX, it’s easier to do it in pieces. Once you do, you realize that many of the aspects of the platform are based around some basic guiding principals. In this piece, I’m going to focus particularly on the security aspects. VMware designed NSX security around micro-segmentation. Aside from being a useful buzzword, it’s also a very smart way to keep your VMs and applications secure.
NSX: Beyond the Perimeter
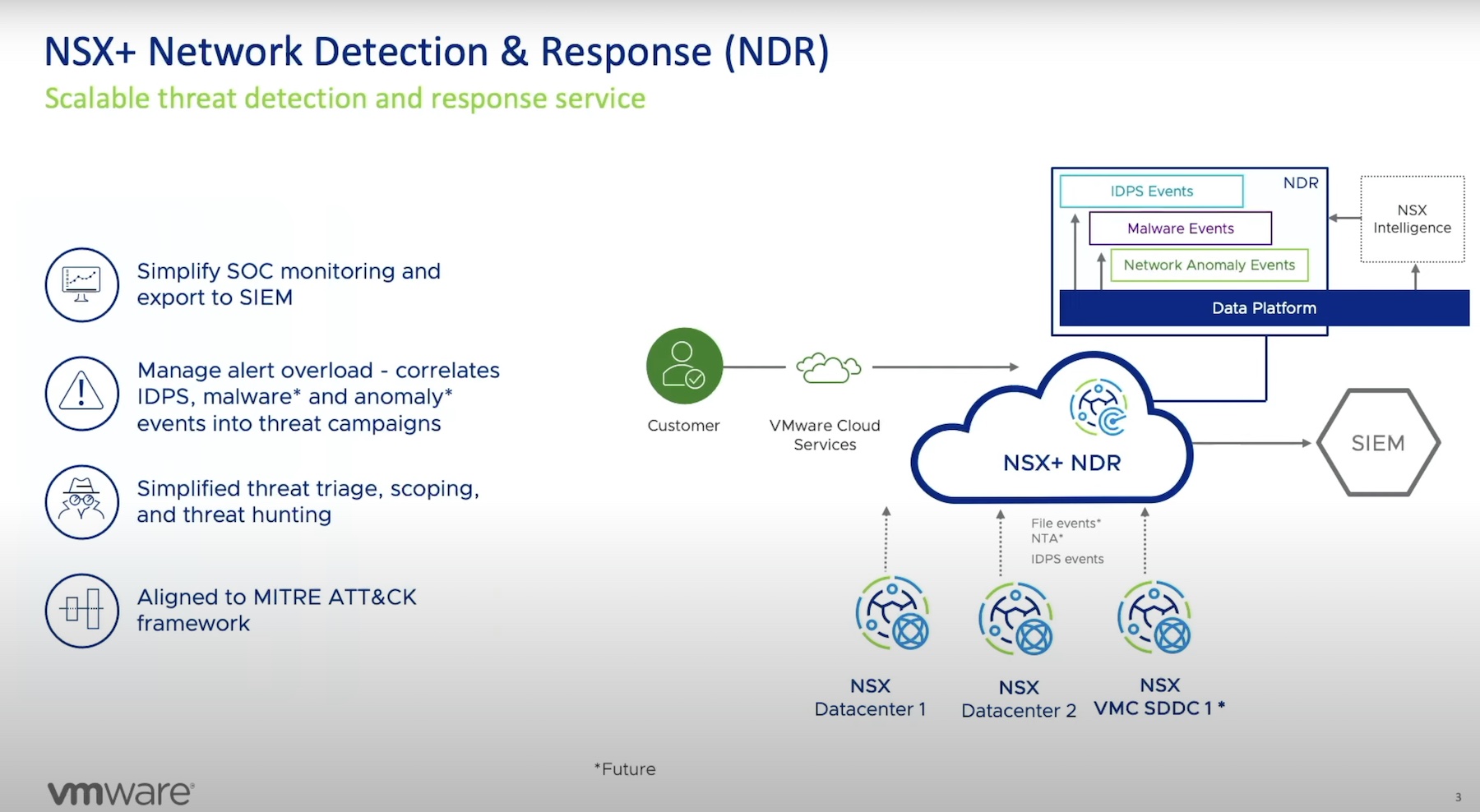
VMware thinks network security begins at the perimeter firewall, but that’s only the very cusp of the an overall solution. NSX is designed to provide the missing components, and get away from a model that has a single large fault domain. This is replaced by their zero-trust methodology. Within NSX, distributed firewalls can be applied down to the application at the vNIC level. With their advanced policy features, this can completely stop lateral threats that are able to get past the perimeter.
At it’s most basic, NSX operates by bringing visibility to your network. After an initial setup, the NSX Application Rule Manager can monitor your network to establish a baseline for communication between applications and the network. From there, it creates visualizations of these flows and automatically create rules based on the discovery. This automation might be the single most impressive part of their entire platform. It’s one thing to have the ability to segment traffic. It’s another thing to have traffic intelligently analyzed and automatically provisioned across your network. I’m sure most network engineers will want to tweak the recommendations, but giving you a solid foundation is fundamental to securing the network.
Policy Wonks
Stateful VM firewalls can also be deployed and modified via policy. VMware gives NSX a full suite of ingest points to govern this policy, making it a supremely customized tool. These can include network-based and vCenter-based objects, but can also be set by user identity. This looks at who is logged into a VM, and the enforce a distinct policy based on an individual. This can surely help cutdown on biggest problem with network security, the human factor. By being able to customize firewall settings down to a given logged in user, you can really focus your security efforts. Admittedly, in larger organizations, this probably isn’t feasible to do with every user, but every little bit helps.
End point monitoring is also supported, giving visibility from end-to-end, across the wire and into the VM. Right now this is strictly a visibility tool, although VMware is also working on a Guest Introspection Framework to accompany this, which would allow for actual application process isolation without the need to install a separate agent. As far as monitoring goes though, it feed back into the overall theme of visibility throughout the platform. To that effect, all the metadata is exportable, or can be published via a policy to a cloud management service.
One Piece of the Pie
NSX security is designed around the principals of isolation and segmentation. Instead of trying to constantly keep a handle directly on the network firehouse, VMware designed NSX to give you extremely granular control. The granularity comes in two fronts. Firewalls can be deployed down to the application level, which in turn support fine tuned policy control to modify those firewalls. It would be a lot to keep track, but the automation features with the Application Rule Manager eases a lot of the burden of initially setting it up, allowing network engineers to only worry about fine tuning and exceptional cases.
I’m still digging into all the possible use cases for NSX, including network automation, cloud deployments, and working across multiple sites. Make sure to check out their presentation from Networking Field Day to watch for yourself.



[…] Welsh has a post on why someone might use VMware NSX. Rich Stroffolino has a similar piece over at Gestalt IT, though Rich points out that this use case is only one aspect of how NSX might be used in an […]