The word is spreading on the Internet that respected secure email provider ProtonMail has been hacked by an anonymous group. A pastebin post by “AmFearLiathMor” titled “Protonmail Hacked” makes the claim that the company intentionally undermined its own security features, allowing the hacker group to infiltrate the front-end code and steal the passwords and data, also installing a backdoor on the company’s servers for a time. They also make some wild claims about ProtonMail’s own activities and those of their users.
But the would-be hacker provides no proof that this hack is real, and ProtonMail is vigorously denying that it happened. Other investigators are skeptical of the claims as well. The over-the-top claims and blatant attempt at extortion certainly undermines the credibility of the paste in our eyes. Although it is possible that ProtonMail was hacked as claimed, we believe that this is probably not the case.
Why Do We Care About ProtonMail?
Why would it matter if ProtonMail was indeed hacked? The service has emerged as a trusted provider of secure email and VPN services for many of the most respected names on the Internet. ProtonMail has even surfaced in the media, claimed to be the communication service of choice for players being investigated by Robert Mueller and many other news stories. Heck, Mr. Robot even uses ProtonMail!
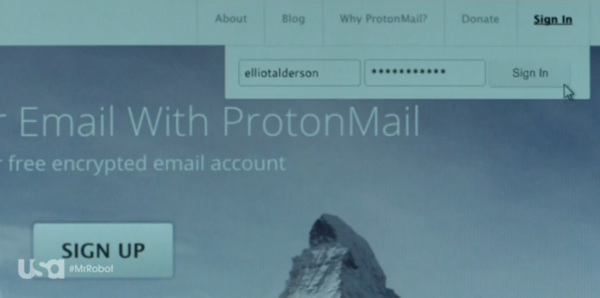
Maybe fsociety is behind the alleged ProtonMail hack
I personally use ProtonMail as my “backstop” email account, verifying other services to it, and I advocate using ProtonMail on my blog. Many of my friends also use it, with some switching entirely to the service to protect their online lives from Google’s intrusive “personalization” features. I’m also a ProtonVPN user and was thrilled to see that the ProtonVPN app went live for iOS this week.
So the stakes are serious if ProtonMail was indeed hacked. It would expose the private email of millions of people, many of whom are extremely sensitive about their privacy. And like any email service it would allow the accounts of many others to be exploited.
Then there are the claims made about ProtonMail in this paste: That the company is secretly cracking users’ emails and passwords, transmitting data to unnamed entities in the United States, and that ProtonMail is secretly owned by an American corporation. All of these would undermine the faith placed in the service as a provider outside the reach of American authorities.
Do the Hacking Claims Hold Up?
The paste claims that ProtonMail intentionally compromised their own email service and left it exposed by not using Subresource Integrity (SRI) checking. This would function somewhat like a cross-site scripting attack, substituting a malicious front-end component to collect passwords and (presumably) second-factor codes. This is all moderately plausible, though it could also be entirely made up.
The paste then drops buzzwords like a TV show: “We began with months of dedicated penetration testing, we asked assistance from other organizations and deployed unreleased 0-days” could be a line from the fourth season of Mr. Robot! But again, it is plausible that a front-end hack could expose user passwords, including those of ProtonMail employees, and enable the company’s servers to be compromised. From there, a wholesale substitution of authentication code could perhaps compromise the passwords of a large number of users.
Although the compromise is plausible, some of the claims about the company are not. If ProtonMail truly sent “decrypted user data to American servers” this would stand in opposition to everything the company stands for. Although Switzerland does have a Mutual Legal Assistance Treaty (MLAT) with the United States, it definitely does not require ProtonMail to “reveal all their data to the Americans” as claimed by the paste.
Then there’s the extortion attempt. The paste gives ProtonMail a week to pay “a small fee” or they threaten to release data uncovered during their alleged hack. This is reminiscent of the sextortion and password email scams going around right now but on a much grander scale. Just like those scams, the data claimed to be exposed quickly ranges from “decrypted emails” to “circumventing the Geneva convention, underwater drone activities in the Pacific Ocean, and possible international treaty violations in Antarctica!” It also claims “rampant pedophilia among executives and the affluent”, a frequent boogeyman of fringe types and Internet trolls. Then they claim that the bulk of the data will be “sold in bulk to the highest bidder on the darknet,” another Hollywood-worthy claim.
The ProtonMail Hack is Likely a Hoax
None of this rings true. Although the attack vector is moderately plausible, the rest of the paste’s claims veer off the rails. There’s too much “Hollywood” and not enough reality to their choice of words, and the alleged hacked content isn’t credible. The fact that there is no sample data revealed suggests that this is all a hoax or a weird trolling attempt.
I’m still using ProtonMail. But I did change my password, just in case!
Update, November 19
A second paste has appeared as a response to skepticism of this hack claim. The purported hackers again claim that the exploit is real and that they have communicated secret information to ProtonMail so they can verify the hack. But they offer no more details to people like us who are observing all this from the outside!
Again, this paste make specific claims about pedophilia, drones, and underwater secrets supposedly contained in ProtonMail user mailboxes. And again, these all seem salacious but not necessarily convincing. They also claim again that ProtonMail is owned by an American company and suggest that it is a CIA front, which would be concerning if there was any proof of these links.
Finally, this new paste says the hackers left “clues” in support tickets that would allow their identities to be uncovered. This is simply astounding, and undermines the whole claim of legitimacy. There is no way a group of hackers focused on extortion would leave clues of their “real last names” as some sort of game for the victim!




i have been keeping up on this and this is there reply i found by scraping pastebin
https://pastebin.com/QQLzU9yy
Thank you for this! We have updated our article.
A former neighbor of mine was obsessed w/me and hacked my home wifi network, my phone, my computer (he was watching me naked on my devices before I knew that that was even possible, breaking into my home, following me on my own google maps etc)…I eventually went to protonmail for everything, including VPN.
This same stalker/hacker managed to change like a dozen protonmail accounts. I don’t know if he HACKED the accounts or simply found a way to CHANGE all my passwords so I wouldn’t be able to access the actual account. I don’t know if he ever went inside my accounts, BUT I did notice that the emails I used as secondary emails to open a protonmail account were ALSO suddenly not opena-able (passwords were changed on me). So, is it possible? This happened a dozen or more times, so many times I stopped counting.
But ALL THE EMAIL ACCOUNTS (also protonmail) I used to OPEN my protonmail accounts, listed INSIDE my account info, were compromised – as far as passwords were changed on them, as well.
BTW – requiring another email to open an email account is NOT the most secure way to open an email account. I tried to let protonmail know about this and they said that what I was claiming, isn’t possible.
Isn’t possible, or they just don’t know it’s possible?
Some loser underground black hat hacker kid who’s far surpassed the 10,000 hours of creating an expert b/c hacking is ALL THEY DO, like the “sexual cyberterrorists” that are gaining speed these days, CAN figure out a way to do this. Avg IT peeps just don’t know about it – not knowing is not the same as IMPOSSIBLE. We need some really good white hat hackers to investigate this stuff, bc if this is possible, then it wil become more and more common….
My stalker also managed to figure out a way to CHANGE my protonVPN settings so that my location was NOT changed even though I would put it on different countries, etc; eventually, it just stopped working. Granted, he was in my computer already and knew which emails I was using, but this happened even when I used OTHER (not my) computers. Perhaps some kind of notification system he set up that pops up when I used certain emails and he can attack/disable what I’m doing.
He’s still stalking me so I’m trying to be anonymous but its a security issue that protonmail should look into. Anyone want to take a guess at this kind of black hat hacker stuff I’m talking about? This is above the paygrade of the avg IT person or computer repair person who says things like “macs don’t get hacked” or even worse, Apple IT “genius” peeps who ask me, “what’s Tor?” when I tell them the same thing happened to my TOR! We need better security!