Anti-virus is still a huge part of and endpoint security plan. No matter how much we would like to believe that the old threats we used to face from copied floppy disks and worms is gone, reality is a bit different. We have to stay ever-vigilant for new threats as well as making sure we’re inoculated from the old issues that might crop up.
But the new frontier of malicious programs don’t come from the minds of people like Robert Morris or even enterprising hackers. Instead, malware is big business designed to evade detection rather than make a statement. People work hard to make sure their programs go undetected rather than having them blast out a message loud and clear for the whole Internet to see.
How are we supposed to detect these kinds of programs? How can we hope to find them when they want to stay undetected? And if they aren’t doing things particularly “virus-like” how are we supposed to rely on existing technologies to help us with the detection and removal of them?
Bad Behavior
For years, anti-virus programs have used virus “definitions” to identify and remove viruses quickly. This isn’t much different than the way your body reacts to an immunization for a particular disease. It identifies the specific patterns of a foreign entity and takes action against it. Definitions are still a huge part of virus removal for one simple reason: Speed. When you match a pattern for the Michaelango virus or for Klez you want that infection gone right away.
Most anti-virus and endpoint protection programs still use definitions to catch a wide majority of the infections they see. It reduces CPU cycles and only requires a database lookup to confirm. There are lots of programs out there that try to evade definitions, though. They use all kinds of crazy tricks, including things like polymorphism, to reconfigure themselves to evade detection. These problems are where the real innovation comes into play.
For the past couple of decades, anti-virus vendors have used heuristics detection engines to find viruses with evasion techniques or that have no definitions. The latter category could include programs that have just been released to take advantage of an brand new exploit, or a “zero day”. These piece of malware have no defining characteristics and so must be found based on how they behave.
Heuristics looks for programs that don’t have clear definitions but do things they probably shouldn’t be doing. This would include things like modifying the system registry in critical system areas or writing files to the operating system folders or even rewriting firewall or service rules to keep them able to persist and communicate with the outside world. Any one of these behaviors in a vacuum could be picked up by a heuristics engine and cause a file or process to be quarantined.
Now, the smart people in the room might have picked up on the fact that any or all of those behaviors could also be done by legitimate programs as well during installation or operation. And that is exactly the problem with heuristics. It’s a very broad category designed to look at virus-like behavior but not much deeper than that. It’s an exception-handling system for programs that aren’t defined as viruses in the engine. As such, it will never be the preferred method for virus detection by the endpoint engine.
Intelligence from Ziften
I had a chance to sit down and talk with Roark Pollack of Ziften during the RSA conference in March. They’ve been around doing endpoint protection since 2010, but the roots of their founders go all the way back to Symantec before that. They’ve seen a lot of time in the game trying to protect computers from viruses and such. That means they also know how to build a system that will protect endpoints from current and new threats as well.
The Ziften integration with Microsoft consoles is impressive. Their ability to protect Mac and Linux endpoints is also critical, as these systems are often overlooked in a protection scheme and often very likely not enforced unless something causes a massive outbreak. However, these kinds of integrations aren’t the most impressive part of what I learned about from Ziften.
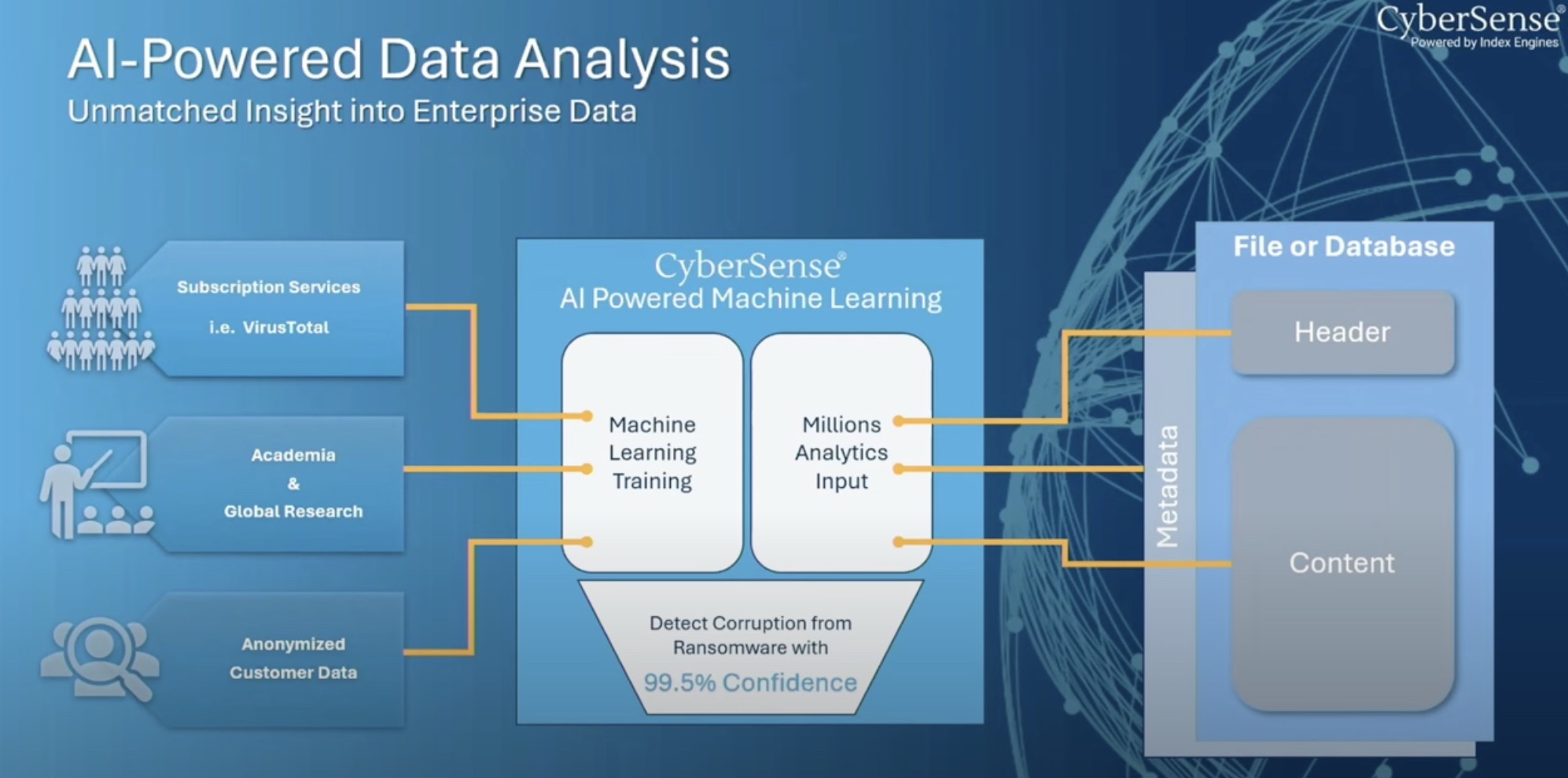
Ziften has incorporated machine learning (ML) and artificial intelligence (AI) into their endpoint protection engine as part of the detection and removal process. Now, dear audience, before you start railing against AI in a security product, I made sure to ask Roark about their implementation. He told me that they are using AI to detect behaviors of unknown programs to figure out how likely they are to be virus or malware-like.
The difference between heuristics and AI in this case is the learning aspect. Heuristics are never smart enough to learn from their mistakes. The heuristics engines never figure out that installation programs for certified applications are valid and should not be flagged. Heuristics engines are also blind to new exploits that find ways around existing detection methods. Because the AI component of Ziften is always looking at the results of the behavior there can be a profile built of known-good applications. There can also be a quick response to currently-unknown infection vectors. Because instead of looking at just the behaviors of the program, Ziften is looking at everything to find out if it walks like a duck and swims like a duck to determine the likelihood that it is indeed a duck.
This is a huge leap forward for endpoint protection programs. I’ve worked with behavior scanners in the past and they almost always either flag everything and create false positives or ignore almost everything to avoid “bothering” the user. And the result is the same: No one trusts an endpoint protection program. It protects from viruses and the most common malware but you’re still at risk to the clever new things that are designed to burrow deep and evade detection. Ziften is hoping to change all that with their impressive AI solution.
Bringing It All Together
When it comes to AI, I’m as skeptical as anyone else. I think there’s a lot of flash and not as much substance as we would like. However, thanks to Ziften, I’m starting to see how the practical applications of AI are really shining is very specific areas. Roark shared a quote with me that resonated when it comes to the difference between what we’ve done before and what we’re trying to do now. He said, “Heuristic detection was a big hammer. AI is more like a scalpel.” Rather than just flagging it all and sorting it out when there’s a definition created Ziften is taking the right approach with their AI solution to figure out how to find the bad programs before they become big problems.
For more information about the Ziften endpoint protection solution, make sure to check out http://Ziften.com.