FireEye recently published a report about the rise of “human-operated ransomware attacks.” According to their study, these types of attacks, which wait for human direction before encrypting data rather than beginning encryption as soon as a network is breached, are up 860% since 2017. It’s part of a larger trend of increasingly sophisticated ransomware, which we’ve also seen start to blackmail organizations in addition to locking them out.
But one chart stood out to me from this report:
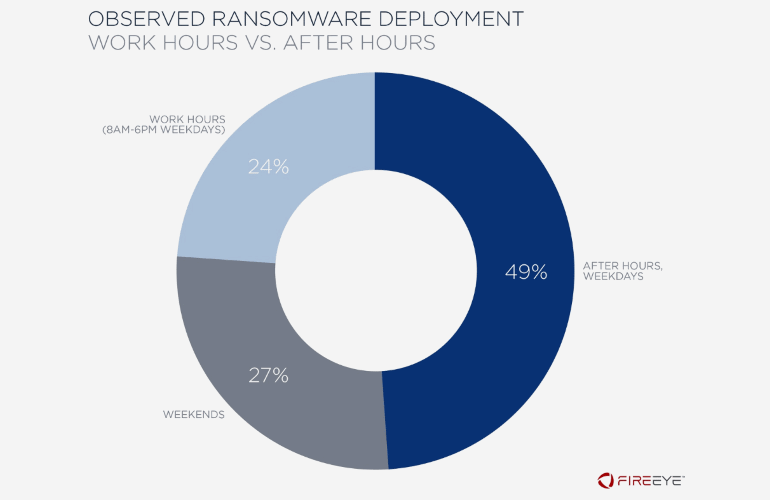
Source: FireEye
One of the takeaways was that most of these human-operated attacks occur at night or the weekend. This is indeed a major problem for IT organizations, it delays mitigation and recovery efforts, as well as potentially allows for the ransomware to spread deeper into an organization. But after looking at this chart, something stood out to me.
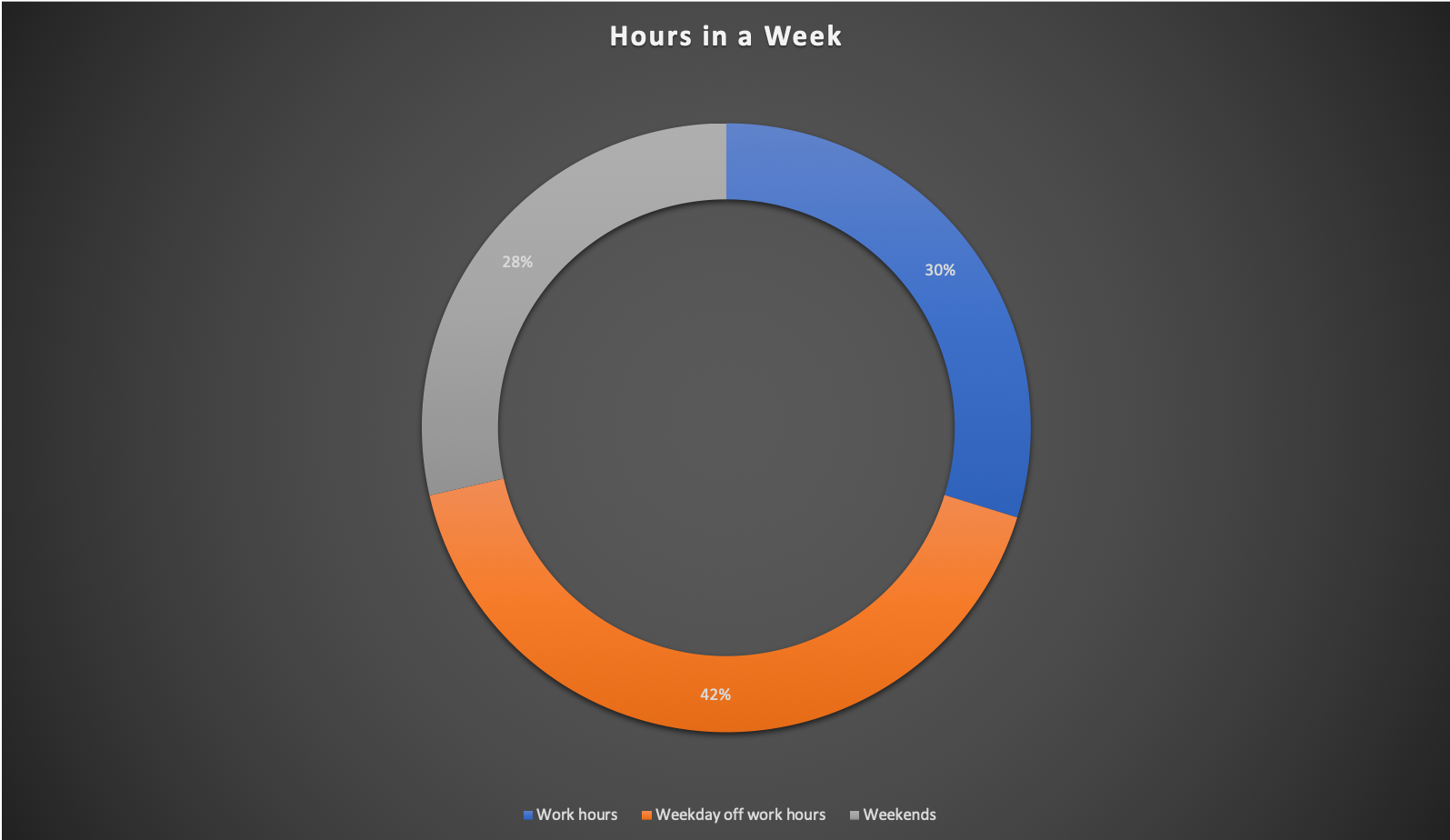
The headline is that 76% of ransomware attacks occur outside of work hours. But if you look at hours in a given week, 70% of hours occur outside of work hours. If ransomware attacks occurred randomly, wouldn’t the total number of occurrences look similar given enough volume? Luckily, there is a better data visualization to prove FireEye’s point.
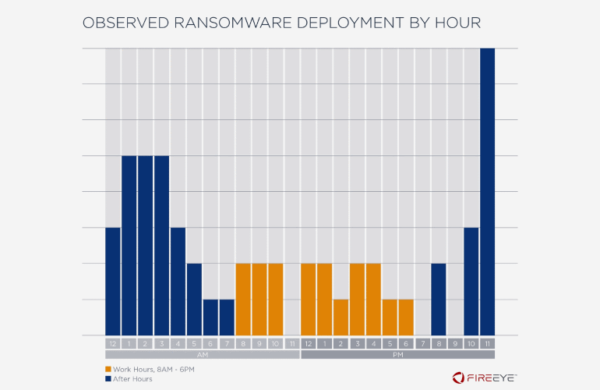
This chart does a much better job getting the point across, with a clear target being painted at off hours (although 11pm seems a bit too early to ensure that a admin wouldn’t get some kind of notification).
Ultimately, this study makes a fantastic case for better monitoring integrated into automation as the best way to protect against ransomware. If attackers are targeting off-hours as the best chance for success, it tells me that too many organizations either don’t have a ransomware mitigation and recovery plan in place or it requires too much human interaction to really be effective.
Read More: Most ransomware attacks take place during the night or over the weekend