It is often the narrative in IT that in order to get premium solutions, one needs to pay top dollars. This is especially true in case of cybersecurity. Any change in security spending begets a corresponding change in the security outcomes, and consequently, on the overall posture. But there is a silver lining behind this rather unpopular reality which often gets lost in the noise. A strong security posture isn’t so much about the solution as it is about the strategy. Even in application security, which captures over $6 billion in spending, there is a way to establish consistent security at a very reasonable cost.
At the recent Cloud Field Day event in California, Fortinet presented three solutions that build on this argument. Cloud Security Architect, Srija Reddy Allam, and Global SAP Security Engineer, Julian Petersohn, staged multiple real-world scenarios to demonstrate to the audience how Fortinet’s solutions build an impenetrable front, providing pervasive protection to applications throughout the lifecycle.
Expectations and Obligations
When it comes to app security, there are some baseline expectations to meet. First, the solution should be easily consumable, and it should not encroach upon the time or bandwidth of the teams.
Second, and this is a top priority with a majority of the organizations, is that a security solution should be able to manage risks at a minimum cost. And last but not the least, affordable operations that would steer an organization away from costly pitfalls.
Securing the Application Development Process
Fortinet pledges to satisfy all of the above, and more. Fortinet’s policy is consistent end-to-end application security which they believe is the secret to drive up cyber resiliency and pare down spending.
Fortinet’s solutions get to the root, and arrest the threat vectors, limiting the possibilities of an attack. Fortinet’s catalogue features a wealth of solutions that brings enhanced visibility and early mitigation of vulnerabilities. Shrinking down the attack surface, not just in production, but right from pre-production, they say, ensures maximum security.
“Application security in general, falls under two primary focus areas- shift left, pre-production and shift right, the production area. The opportunity in pre-production is in how far we can reduce risk and shrink the attack surface. We can reduce risk and improve our security baseline at the least cost there,” explained Petersohn.
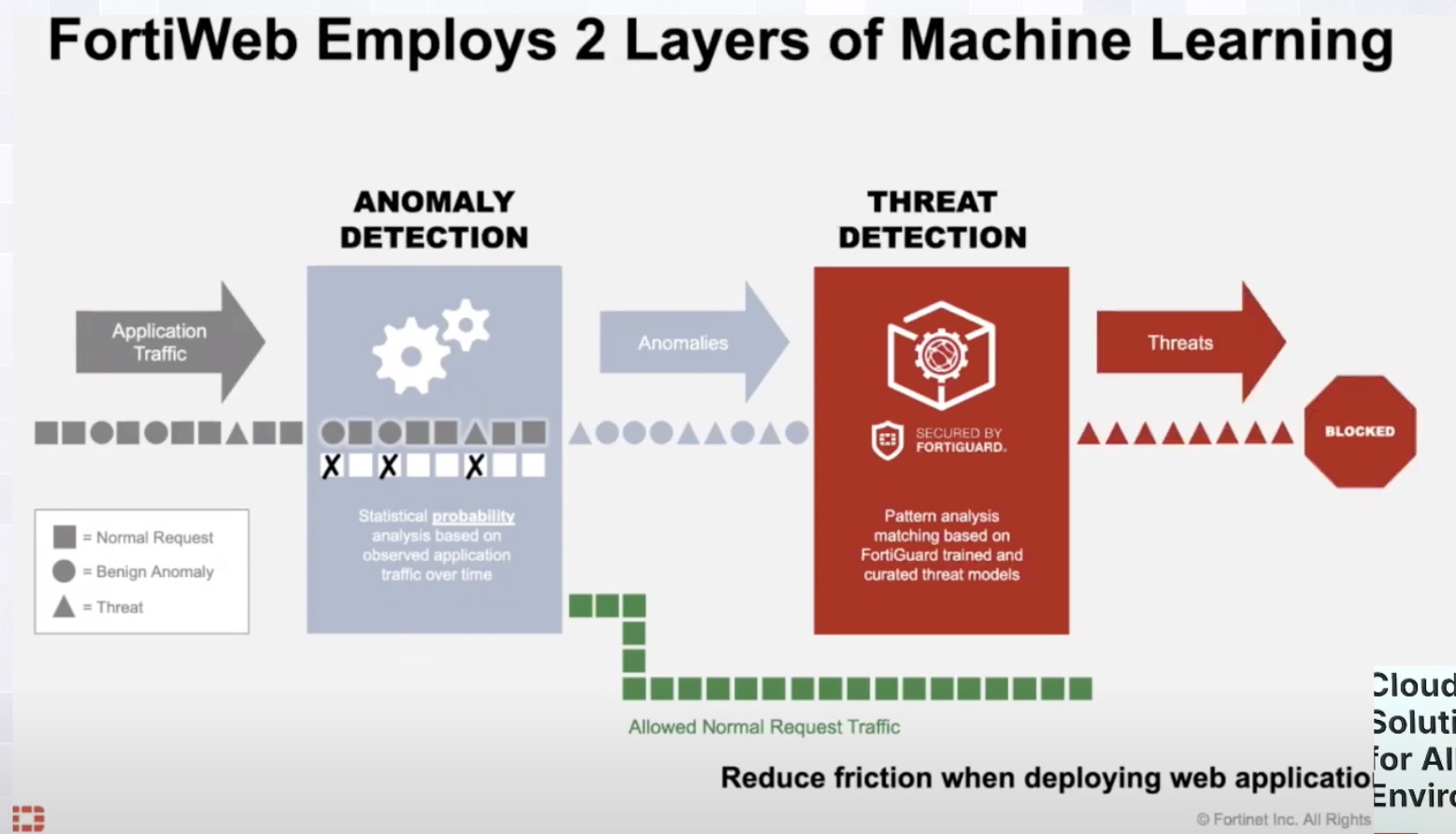
“After the application gets into production, this is the point at which it faces the highest risk. Here, the security must adapt to the user inputs behavior, identify malicious versus benign anomalies, and that, without affecting anything of the usual benign behavior, or making it even more complex to go out there,” he noted.
Fortinet Security Fabric
As an industry leader of many years, Fortinet knows better than most how to combat cyberthreats. For Fortinet, the path to complete protection is through a 360-degree approach. Its solutions, when working together, ensure a defense readiness that organizations need to operate in the perilous digital world of today.
For that they offer a holistic solution that is called the Fortinet Security Fabric. Fortinet Security Fabric is a unified solution designed with heterogenous integrated solutions and services. True to its name, the solution deploys as a fabric, protecting environments against the most vicious kinds of attacks, be it in cloud, on-prem, edge, remote or campus.
When weighed against point security solutions, the Fortinet Security Fabric has several significant advantages. Rather than relying on standalone products, Fortinet packs the best of its security solutions into a platform. Being powered by a multitude of integrated tools, services and capabilities, each one of which is designed to deliver a certain kind of protection, this fabric provides the broadest defense.
In the guts of Fortinet Security Fabric is FortiGuard Threat Intelligence, the crown jewel of Fortinet’s security portfolio. It’s where their deep awareness of the real-world threats comes from. Threat Intelligence picks up telemetry via millions of Fortinet sensors deployed worldwide. A constant stream of intelligence from FortiGuard Threat Intelligence feeds into the solutions keeping them up-to-date about the latest threats and trends. Combined into a single solution, these services reduce management complexity and cost overheads.
Fortinet’s is an open ecosystem. Petersohn informed, “We have over 500 solutions in our fabric, which can exchange information with over 350 vendors.”
In short, the Fortinet Security Fabric is a slam-dunk for any organization looking for security to be integrated in way that it does not get in the way of application delivery.
Application Security with the Trifecta of FortiGate CNF, FortiWeb and FortiDevSec
During the demo, the team brought three products into focus to showcase the strength of protection provided by Fortinet.
FortiGate CNF
First in line was the FortiGate Cloud-Native Firewall Service. FortiGate Cloud-Native Firewall (CNF) is a fully managed, firewall-as-a-service solution that is designed to relieve security operation workloads and simplify cloud network security. FortiGate CNF comes with advanced features like bad IP and DNS filtering, Intrusion Prevention System (IPS), geo IP policies, and application layer visibility.
All security and authentication features can be put to set-and-forget mode which means that the service to do its job without manual intervention. It allows the security teams to offload the works of configuration, provision and maintenance of the firewall software which automatically brings down the TCO, and leaves them to focus on policy management.
FortiWeb Cloud
Next up is FortiWeb, a web application firewall whose chief function is to block attacks aimed at exploiting web applications and APIs. Also a SaaS offering, FortiWeb has a host of great features including easy on-boarding, vulnerability scanning, bot detection, and ML-based detection and blocking. ML-based analytics reduces false positives, and enables it to look beyond the conventional security models.
Srija Allam informed, “FortiWeb Cloud can be subscribed from any of the major clouds like AWS, Azure, GCP and OCI. All you have to do is subscribe to the AWS marketplace. From there, it’s like creating a social media profile. Just create a support account on support.fortinet.com, and you can log into FortiWeb Cloud.”
FortiDevSec
The third and the final product that ties it all together is FortiDevSec, another SaaS-based offering from Fortinet. FortiDevSec comes packed with vulnerability detection and management capabilities, but most importantly it has the DevSecOps DNA that allows developers and DevOps to use it alike, without requiring any specialized security expertise.
FortiDevSec is primarily a testing solution that automates application testing in the continuous integration/continuous deployment (CI/CD) lifecycle. With just a few lines of codes, engineers can integrate it natively into their CI/CD process. This is particularly useful in agile methodologies where everything happens concurrently and in iterations, and there is not much room for continuous testing.
FortiDevSec scans things like source codes, open-source, third-party libraries, secrets, and Infrastructure as Code (IaC) for hidden vulnerabilities. It serves up the findings on a consolidated dashboard that offers visibility into all the security risks existing in a web application.
Wrapping Up
The end-to-end security imperative is especially paramount in application security. But cost should not be the Achille’s heel of comprehensive security. The solutions show that Fortinet knows how to embed security in the DNA of app development, and most importantly, to do it without blowing up the TCO. Besides doing the obvious job of helping organizations combat the latest strains threats, the solutions examine vulnerabilities, and weed them out to make applications safer throughout their lifecycle. With this trifecta, Fortinet proves once again that security is truly in its wheelhouse.
If you are interested in the technical details of the solutions, be sure to check out Fortinet’s presentation above from the recent Cloud Field Day event.