It has long been suggested that multi-cloud enhances efficiency and agility for organizations. Since services of multiple cloud vendors are used, the theory goes that it brings together best-in-class services at the lowest price-point. But as companies take steps towards a multi-cloud-based future, they get tripped up by extraordinary networking challenges.
At the recent Cloud Field Day event, Prosimo, a multi-cloud networking company, demonstrates how these challenges can be leveled with a well-rounded cloud-native network blueprint.
The Vagaries of Multi-Cloud Environments
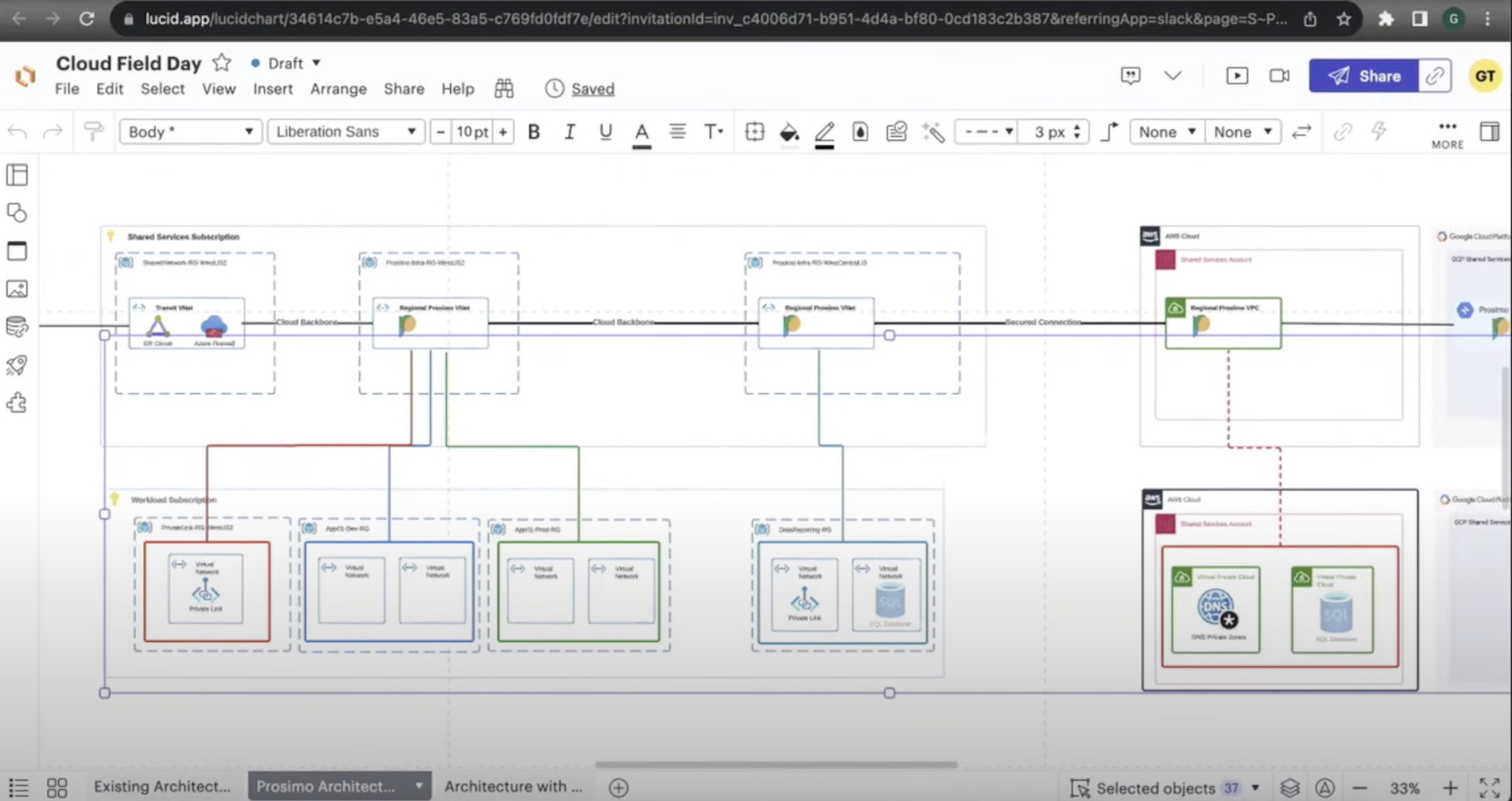
Drawing from a customer case study, Principal Solutions Architect, Gaurav Thakur, walked the audience through the list of challenges wrapping clarity around the aspects of security, observability and connectivity in multi-cloud.
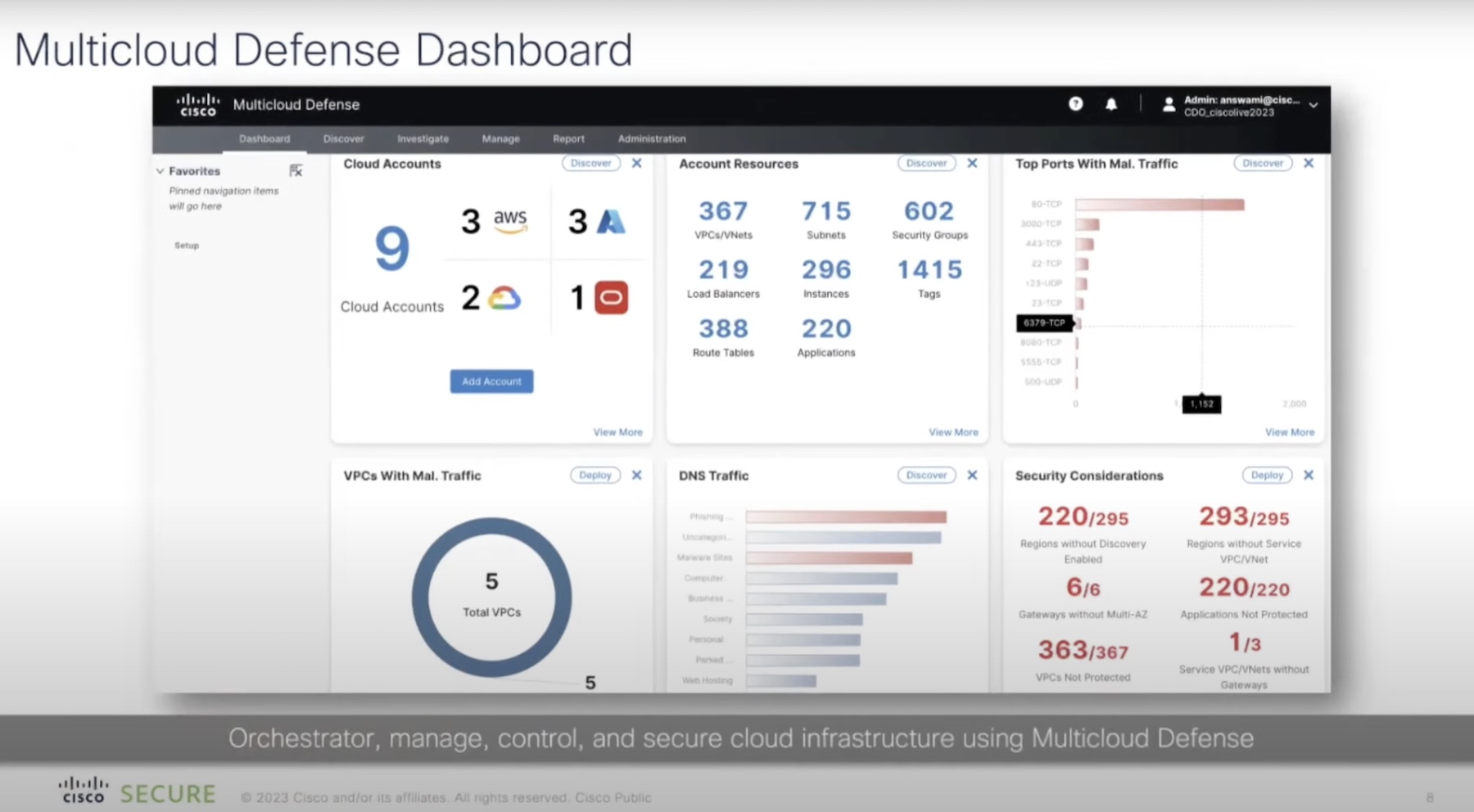
The world of multi-cloud is as divided as it is distributed. It is a hodgepodge of network connections, applications and data that networking teams need to make sense of, observe and manage.
Enterprises’ dirty little secret is that multi-cloud networking is an afterthought. The industry talks endlessly about the value of multi-cloud, but is quick to overlook how much work is needed to actually make it work. There’s nothing simple about stitching together infrastructures that have very different architectures and dissimilar methods of connecting with one another.
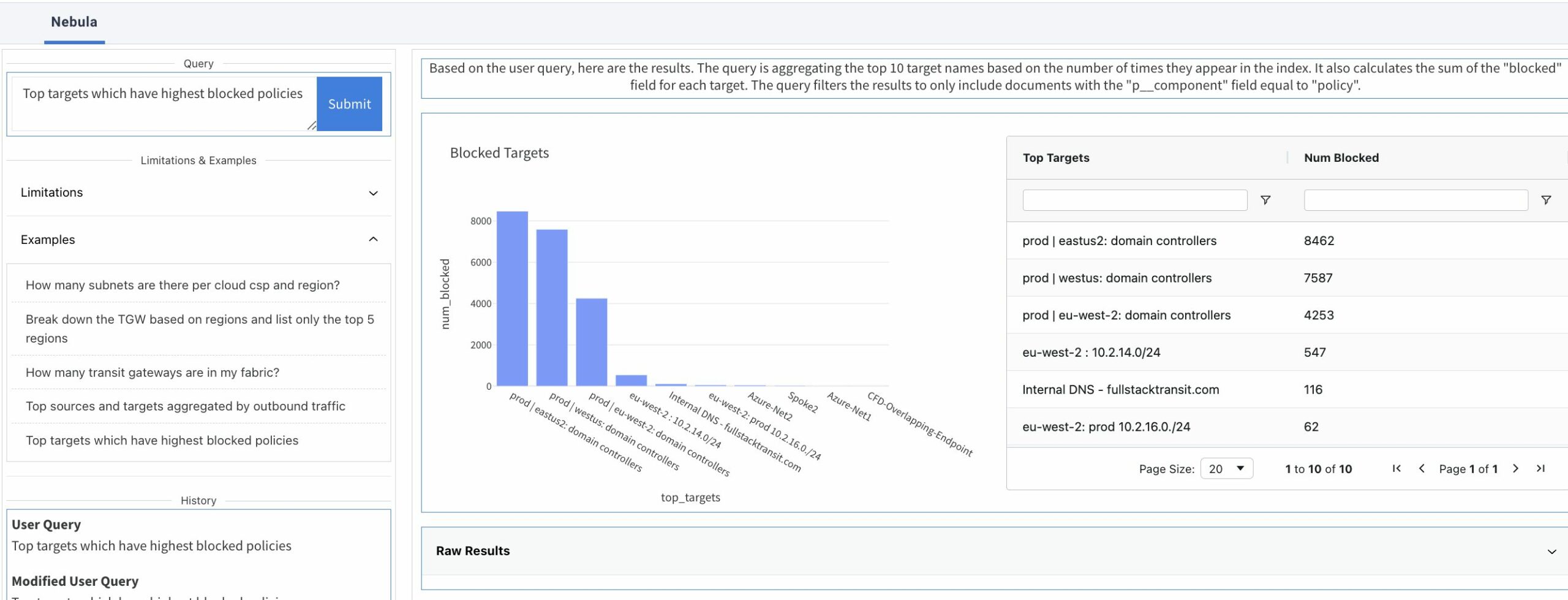
It turns out, that getting a handle on all of this is a pretty hard job. Operators tasked with making the connection have no way of viewing the assets from a vantage point.
“If something goes wrong, they don’t even know where to begin troubleshooting because the connections are everywhere,” says Thakur. And with little visibility of how the traffic is flowing from source to destination, it is a puzzle that cannot be solved.
“Cloud providers brought in constructs like private link that have to be integrated so that all of the traffic, at any given point, is private,” said Thakur. Integrating these constructs to the network adds overheads.
Applying a consistent security policy on top of this is a whole other worry, not to mention the surface area for attack gets a lot larger. “Services and applications are no longer sitting inside a virtual network boundary. PaaS services for example, do not sit in a virtual network that’s managed by the cloud provider. If enterprises have to enforce the same security standards, how should the communication be?” said Thakur.
As a result of this, IT personas like developers who are laypeople when it comes to networking technicalities, find it harder to consume services.
Implementing a Cloud-Native Blueprint
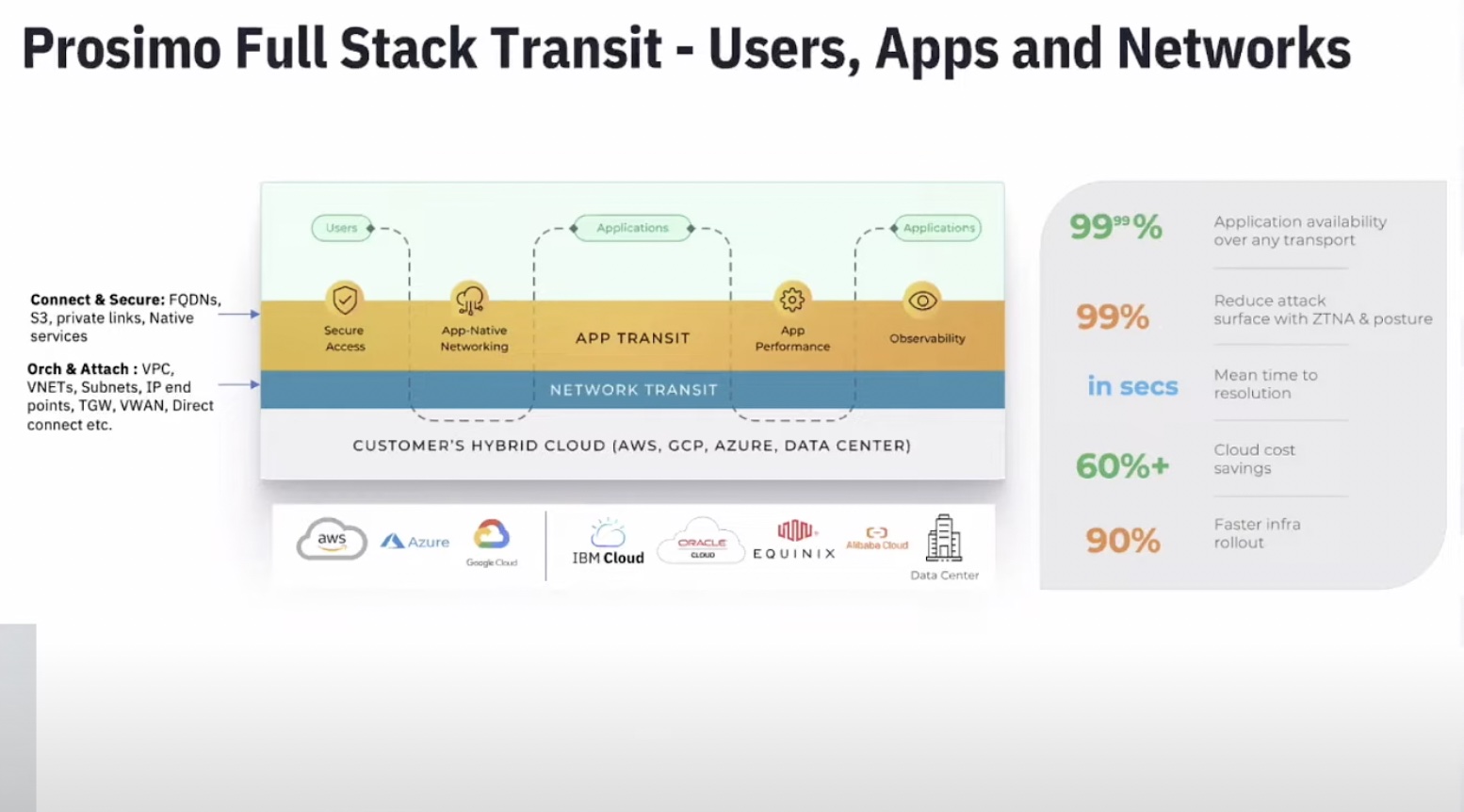
The early adopters of cloud tried to replicate the datacenter networking model in the cloud, but multi-cloud requires a blueprint that is cloud-native by design. Prosimo attempts to solve the bulk of the problem by making cloud networking a self-service option. The result is full stack cloud networking that ties together the disaggregated pieces of multi-cloud networking onto a single, cross-platform networking fabric.
This fabric is cloud-native, and has all the abstraction layers built in. It supports accelerated cloud migration following the security and compliance protocols.
“Full stack from underlay connectivity to layer 3 overlay, all the way up to layer 4 and layer 7 is what we really want to provide,” said Mani Ganesan, VP of Product.
On this plane, orchestration of networking resources happens through Prosimo Edge. “The fabric spans across regions, and clouds. It’s a full mesh of these Edges. You can go ahead and deploy these edges from the control plane and once the Edges come out, they are capable of discovering each other,” explained Thakur.
Network applications, no matter how diverse, can be onboarded on the platform. “Any application type, whether it’s SaaS or homegrown, or the connectivity model, doesn’t matter. If they already have a transit gateway, it’s our responsibility to use that as a Brownfield setup and make it work leveraging the cloud-native principles,” said Ganesan.
Prosimo Edge is deployed using Kubernetes, and native Kubernetes services provided by cloud providers. As a result, high availability and redundancies are baked in. Operators can attach innumerable networks and applications to it, and send across hundreds of GBs of traffic as long as the underlay can support it, says Thakur. Prosimo will auto-scale elastically adjusting to the volume.
“Think about it as a cluster that is running in a customer’s environment.” Connection is established by building secure tunnels between two Edges over the Internet. Prosimo also supports building the connection over a private circuit, said Thakur.
The process of deploying these Edges is minimal. “To deploy, you go through the control plane, choose what region you want to deploy it in, and we take care of everything that is required for this Edge to be functional,” explained Thakur. “You don’t have to make any change to your existing network, VPCs or applications. It’s set in your own cloud account.”
Once the Edge is deployed, operators can dynamically attach any network – datacenter, cloud, and so in – to it with a simple point-and-click implementation. It will discover all networks that are associated to that cloud account.
The networks and applications communicate via cloud-native networking constructs like VPC peering and private service connects. Alternatively, companies can also use the public internet to connect.
This kind of tight coupling of resources results in maximum cost control. “We did this analysis with our customers. Just looking at the cloud bills, 17% of their cloud spend, on average, is just for networking charges. They don’t realize this until they go deeper to figure out who’s consuming all the bandwidth and why they are paying this processing charges,” shared Thakur.
To enforce tight security, these networks and applications can be segmented and siloed. “If you have a broad network segment, you can attach your network from datacenter to it, or your network from AWS, Azure or GCP. This network is global in nature, and spans across the fabric.”
But even though everything is on common layer and is routable, they cannot communicate by default unless operators specify the intent. “We follow is trust-nothing philosophy where you have to actually use a policy construct that will define who can talk to whom.”
Prosimo simplifies this part by enabling operators to enforce user-defined rules and boundaries without delving into the nuances of individual clouds.
Prosimo supports any cloud, and any connectivity, be it private links, peering or tunnels. In many ways, it is a network as-a-service, but one that is controlled by the customers, unlike the traditional middle-mile network as-a-service.
Be sure to check out Prosimo’s in-depth presentations from the recent Cloud Field Day event for more on this.