Do you ever log into systems? That’s a silly question. We all do. But do you usually log into 14 systems at once? Within 30 seconds of each other? Probably not. How about web surfing? We all enjoy using the World Wide Web to look up recipes and sports scores. But do we typically connect to a webpage and then start enumerating directories or looking for cross-site scripting exploits? Not usually, unless we’re the bad guys.
Almost every user does the same behavior when they connect to a system. They log in, connect to resources, and use those resources. It’s a pretty standard affair. But what happens for those cases when people do something that’s outside of the norm? This is the case for the above examples where you had users logging into multiple systems within seconds of each other or directory enumeration. These are all classic examples of “bad” behavior that we would expect to find during some kind of attack on our systems.
We have SIEMs and multiple other software solutions today that are designed to tell us when something doesn’t look right. We can get alerts for all manner of things going on in our environment. We can tell when something is behaving in a way it shouldn’t. Usually, we can tell this because we have analyzed tons of different behaviors over the life of a system and we know what normal is supposed to look like. That’s how SIEMs and other traditional security tools are triggered when bad behavior happens. But what about newer behaviors that we haven’t observed yet? What about emerging threats that we can’t identify because we’ve never seen them before?

AI to the Rescue!
One of the biggest emerging technology fields in security revolves around using artificial intelligence (AI) and machine learning (ML) to analyze data and find a common thread among it all to identify threats. Remember, we’re looking for bad behavior. So we want to baseline what good behavior looks like. Historically, this has taken a lot of time and effort and we have had to engage multiple systems over time to figure out when people are doing something that they’re supposed to.
Machine learning algorithms, on the other hand, are really good at looking for patterns and aberrations in those patterns. They can quickly tell you if something looks like it did the past few times it was observed or if it’s a new category of behavior. Remember that one of the things that attackers want to do is avoid detection. They will take the slow route to avoid tripping sensors. They will log in under different user names to try defenses and avoid setting off alarms.
AI and ML, on the other hand, are always watching. They can see when user “jdavis” logs in and will observe those patterns. If jdavis only ever logs into the payroll system and never touches other servers during the workday, that pattern is logged. Then, if that same user logs in at 3 am and starts connecting to infrastructure servers and listing directory contents, the ML system can quickly tell you that something isn’t right here because it doesn’t fit the previous pattern.
Sounds simple, right? And you’re probably laughing now because AI and ML are some of the hardest development jobs in technology right now. It’s not easy to write software programs that can learn on the fly and draw conclusions against those that a human might come up with. It’s hard to get it right the hundredth time you try, let alone getting it right on the first or second.
Juniper Jumps In
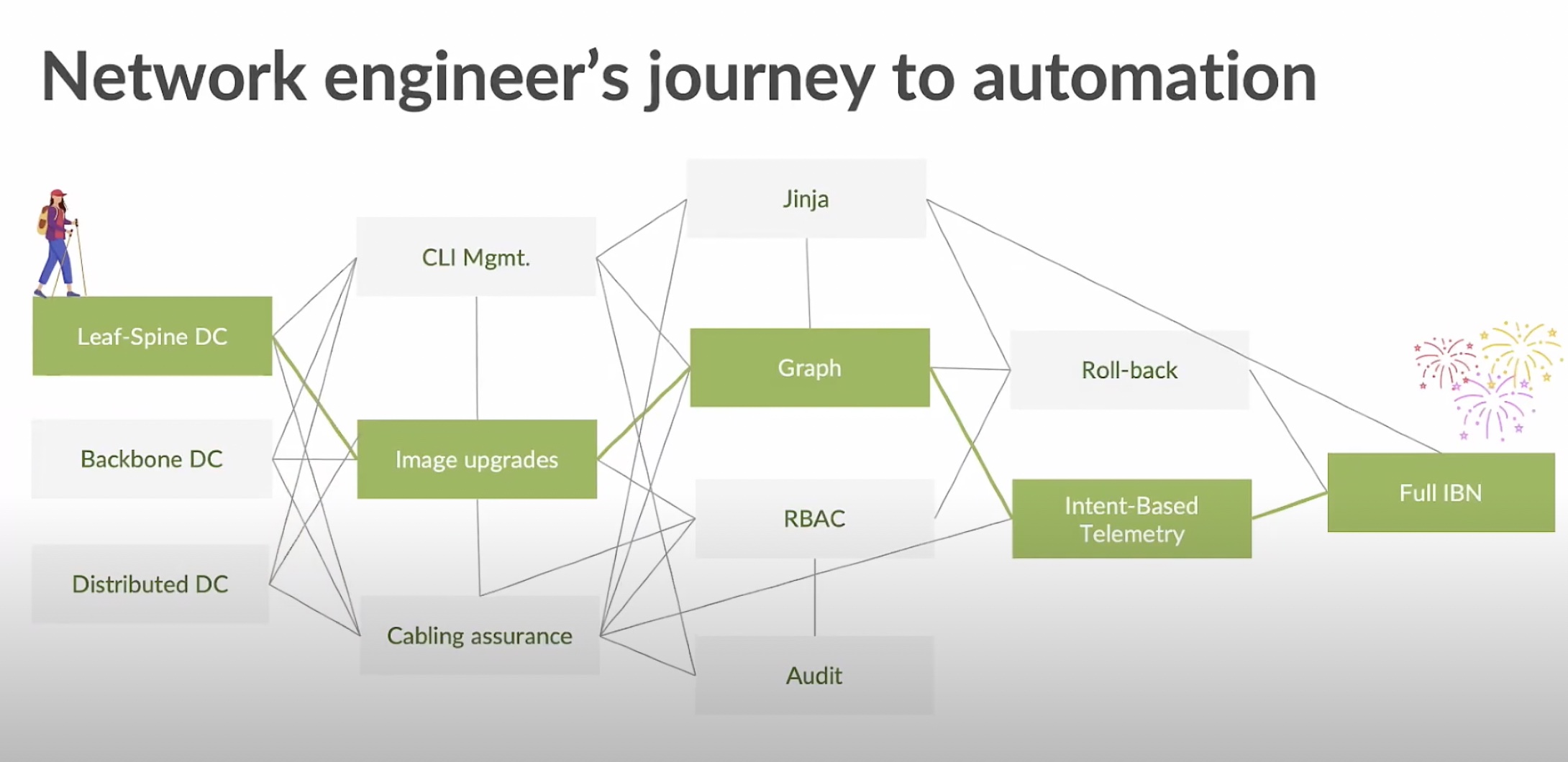
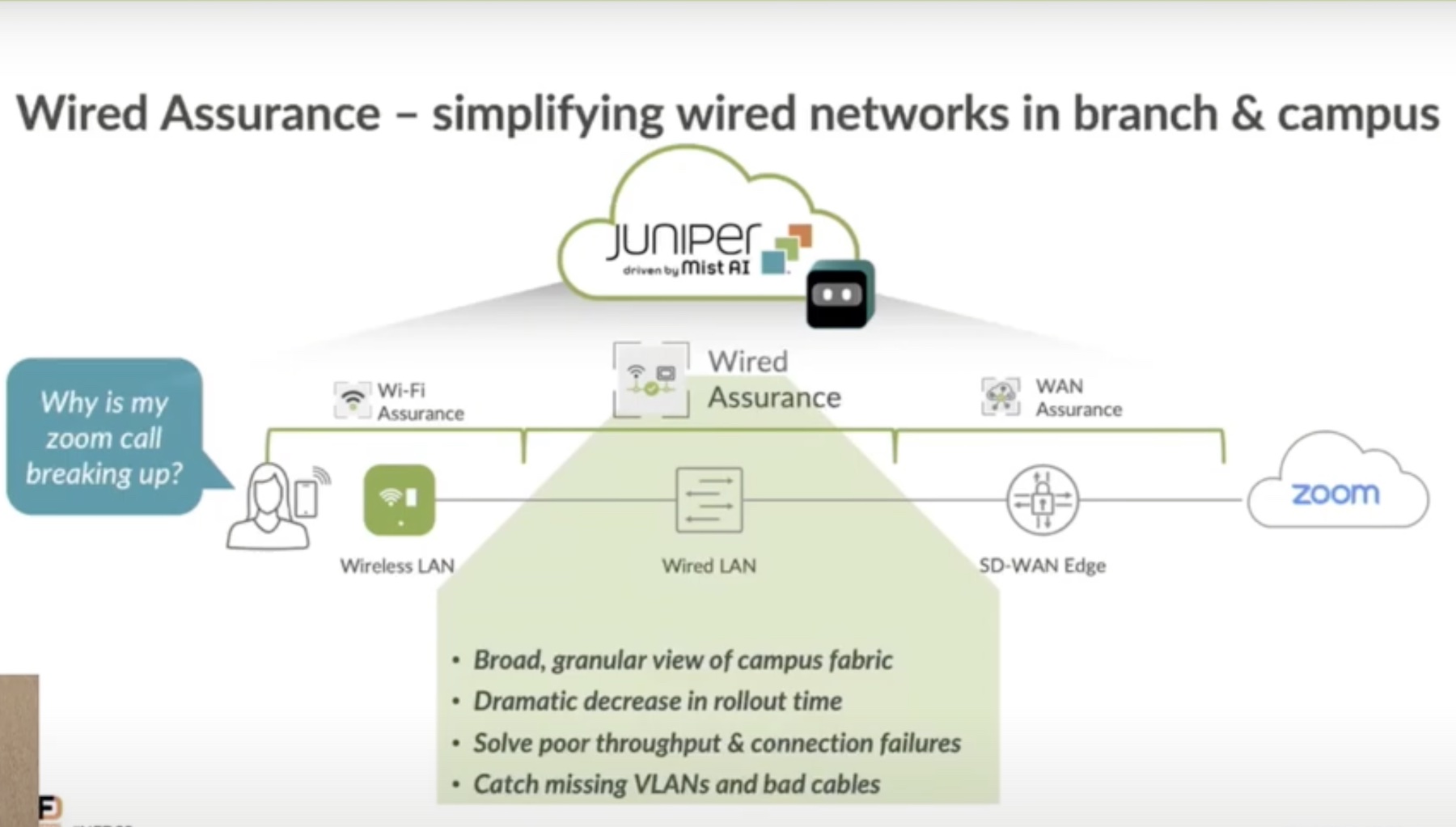
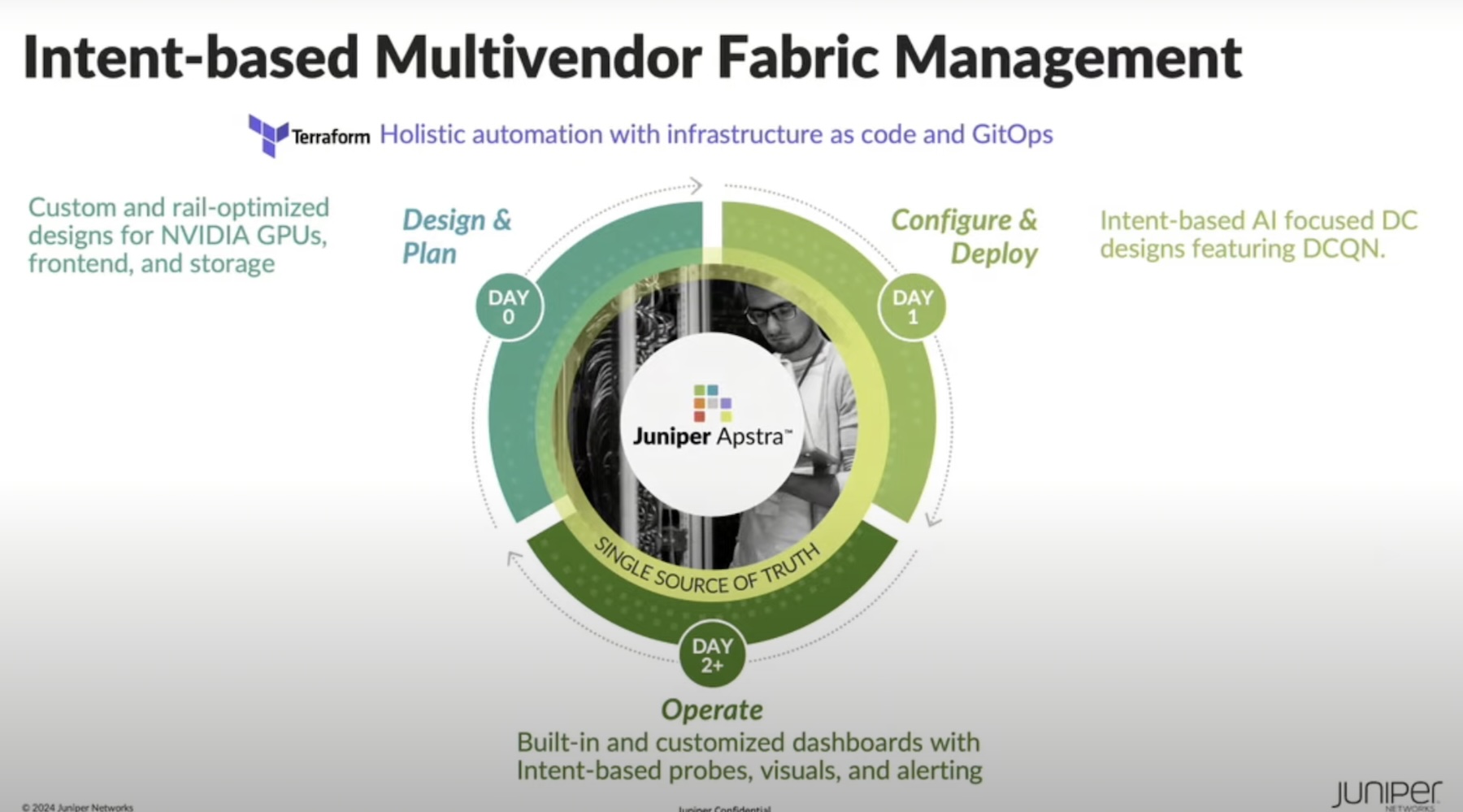
This is where the folks at Juniper Networks come into the picture. You probably have heard the name from their service provider and enterprise networking solutions. Or maybe you picked them up when they acquired Mist Systems last year. Whatever the case, what you should be seeing from them now is a lot of work that’s been done on the security front with AI. During Security Field Day 3 back in May, we got a great look at two different types of security platforms that should be of great interest. The first was Juniper’s overall strategy for using AI in the enterprise network:
The second was the video on encrypted traffic analysis:
Both of these videos highlight the efforts that Juniper has been putting into using AI and ML to augment security. Normally this would be a case of a networking company developing a feature that is quickly becoming standard in the industry for analytics. But the real key here comes from their acquisition of Mist Systems last year.
Remember when I said that it was just as hard to build AI and ML models the hundredth time as it was for the first time? If Juniper had just been starting their AI development process, I wouldn’t have gotten excited. However, they’ve been in development long enough to figure out where they need to focus. The addition of the team at Mist Systems was a huge boon for them. This expertise in the field of AI research is the kick in the pants that starts great things. Instead of making the learning mistakes that all companies make when building these models, Juniper could instead rely on the knowledge that came with the Mist team and build from the shoulders of those AI giants.
The result becomes a system that can evolve and adapt quickly to the changing needs of behavior analysis in the network. As new attacks are developed and released into the wild, the system can protect against the behavior of the attack instead of needing to wait until a signature is developed to find the attack. Because ML can figure it out from the data it sees instead of waiting for more definition in the data, you can quickly figure out what’s going on and make your decisions about blocking or quarantining the traffic for later analysis.
Bringing It All Together
A wolf in sheep’s clothing is still a wolf. You can tell because it does wolf things. Like eating sheep. Likewise, bad behavior stands out among all manner of creative ways to hide it. The key to identifying that behavior is not to build a wolf detector that alerts you when a sheep gets eaten. Instead, you build a system that looks at every sheep and notices when there are sharp teeth and claws and makes the immediate determination that something needs to be done instead of waiting for certainty.
For more information about Juniper Networks and their AI and ML Security solutions, make sure you check out http://Juniper.net.