I’ve spent a lot of time learning about replacements for spanning tree protocol (STP) over the years. The two biggest contenders to the crown were Transparent Interconnection of Lots of Links (TRILL) and Shortest Path Bridging (SPB). Once upon a time, I thought that TRILL was going to be the clear winner. The tech behind SPB was sound but no one wanted to pick it up and run with it. Avaya was the biggest SPB champion out there, even using it during the 2010 Winter Olympics in Vancouver. But TRILL had all the support in the world and looked to be the way forward. Until it wasn’t. The cloud changed the way we looked at connectivity and the need to interconnect large campuses and data centers. With the rise of VXLAN and NVGRE, TRILL and SPB filtered to the back of the line and were promptly marginalized.
A funny thing happened along the way, though. Avaya was bought up by Extreme Networks. And SPB got a fresh look. Not through the lens of the data center but instead as a new take on security. As it turns out, being able to build pathways at layer 2 between hosts or devices is a great way to also be able to isolate those devices as well. You can direct traffic any which way you want it to go. And if you’re a security person following along, you may be saying the same word that I’m thinking right now:
microsegmentation
As we start looking at the need to run a zero-trust campus or even data center, the idea of isolating workloads and communications pathways is even more important than before. It’s not enough to hope that data isn’t going somewhere it’s not supposed to be. Now, we have to ensure that data is being delivered to the right locations and also to be able to tell that data isn’t going somewhere it shouldn’t. The certainty is a little more pedantic, but much nicer than having to deal with a security audit. Or worse, having to hear your company is the latest security breach newsmaker in the headlines.
SPB is a protocol built to address those issues. Today, you have to get creative to ensure that pathways are built or denied. Maybe it’s a VLAN with a VACL. Or perhaps you’re using VRF-lite with MPLS. If you’re crafty you could be using VXLAN tunnels everywhere you can terminate them with a VTEP. Or, if you have a security background, you’re probably putting firewalls between everything that has a network card. It’s a temporary solution that doesn’t scale at all. And if you find out that someone has a way to bypass one of these protections you’re going to be scrambling to implement something new.
As for SPB, take a look at this video from Networking Field Day 21 last October. Ed Koehler does a great job of talking about SPB:
Ed’s been working on SPB for most of the past decade. He’s seen the protocol transform from data center to security darling. Honestly, SPB makes all the sense in the world for the kinds of isolation that need to be done today. It uses MAC-in-MAC encapsulation to virtualize the network. It then uses IS-IS in the control plane to advertise different network “services” to hosts. If a host is able to create a circuit to that service, the pathway is built and traffic is forwarded. If there is a policy that denies that or doesn’t explicitly allow it to be built it doesn’t happen. And, because there is no spanning tree to block links, all the links in the fabric are forwarding at all times for the pathways they contain.
Service All The Things
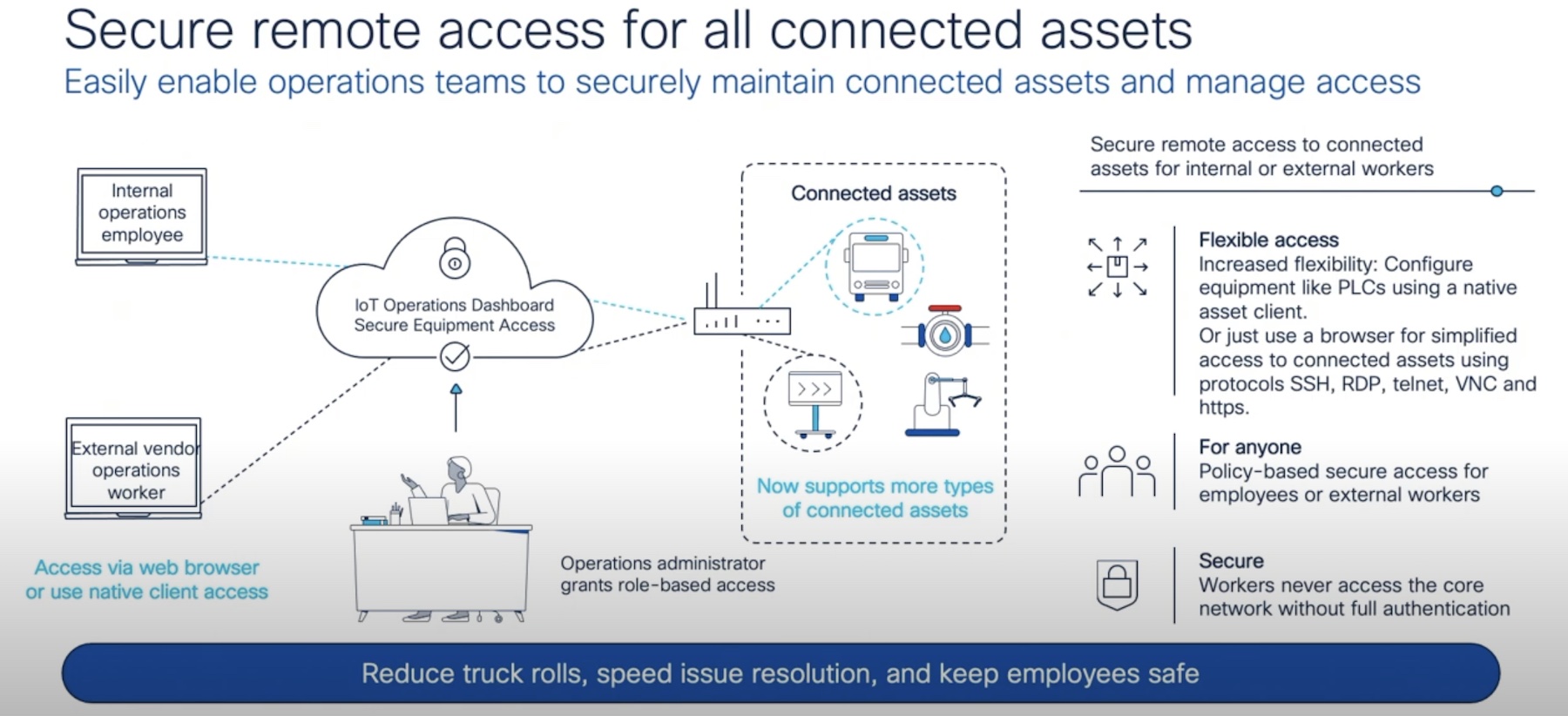
My first big thought for using SPB is for Internet of Things (IoT) networks. These edge devices don’t have a lot of CPU to do tricky things with networking stacks. And the devices they plug into aren’t always capable of terminating VXLAN tunnels or running MPLS. Instead, enable SPB at the edge of the network and let the heavy lifting be done elsewhere. With SPB, you can advertise the networking that is needed to connect these devices and they are none the wiser.
Even better is that, by having centralized control of the way the networking is handled in the underlay, you can ensure that IoT devices don’t become a source of exposure later. We’ve all heard about the fish tank thermometer debacle. Or how Target was hacked via HVAC and had their POS systems breached. These stories are the baselines for ensuring your devices are isolated. I’d argue they have become the clarion call for microsegmentation in the industry. By using something like SPB to isolate devices on the network you don’t have to worry about someone breaching the system with malformed packets or escalation exploits. If the only thing the HVAC or monitoring system can talk to is an external server or a central comms server you don’t have to see traffic being sent back and forth to areas that it should never be touching.
Bringing It All Together
I will say that I picked the wrong horse all those years ago. I was sure that TRILL had the backing and the pedigree to be the dominant data center interconnection protocol. Sadly, the environment changed and left TRILL blowing in the wind. SPB continued to innovate and reposition as a security protocol. And then with the help of the cloud and IoT, SPB found itself exactly where it needed to be: becoming a foundational fabric for building out secure infrastructure going forward. I’m glad Extreme gave us a look at what they’re working on with SPB. And I think it’s time I took another look at it in depth.