Although keeping bad actors out of the network is important for security, in today’s landscape, where attackers can exist within the network for months to years at a time without notice, tracking network traffic proves a more effective way at ensuring security over longer spans. Unfortunately, monitoring network traffic is a real chore when done manually. That’s why VMware has buffed out their software-defined NSX Firewall product to streamline East-West traffic security, which they showcased at their recent Security Field Day appearance.
The Importance of East-West Security in the Network
In IBM’s 2021 Threat Intelligence Index, one of the key findings is the fact that 35% of breaches reported in 2020 were initiated by a scanned exploit, the #1 initial attack vector of the year. For context, that number is up 5% from 2019 (30%), and up even higher from the 8% reported in 2018.
Given the general difficulty of patching every little potential vulnerability in your network, some security professionals have resigned to the fact that it’s inevitable that a bad actor will somehow make their way into the network. With that in mind, it’s time to rethink the way we secure our networks, shifting from focusing solely on keeping attackers out altogether to instead finding ways to reduce the overall amount of time they can exist within your network, also known as East-West security.
Setting Up Defenses Inside the Network with VMware NSX
The network security team at VMware cares a lot about East-West traffic, in some may say a maniacal fashion. Their NSX Firewall software is purpose-built to safeguard East-West traffic at the hypervisor layer. It does so by creating smaller, software-defined firewall fragments across each workload of the hypervisor that act as a single, unified firewall controlled and managed through a single pane of glass.
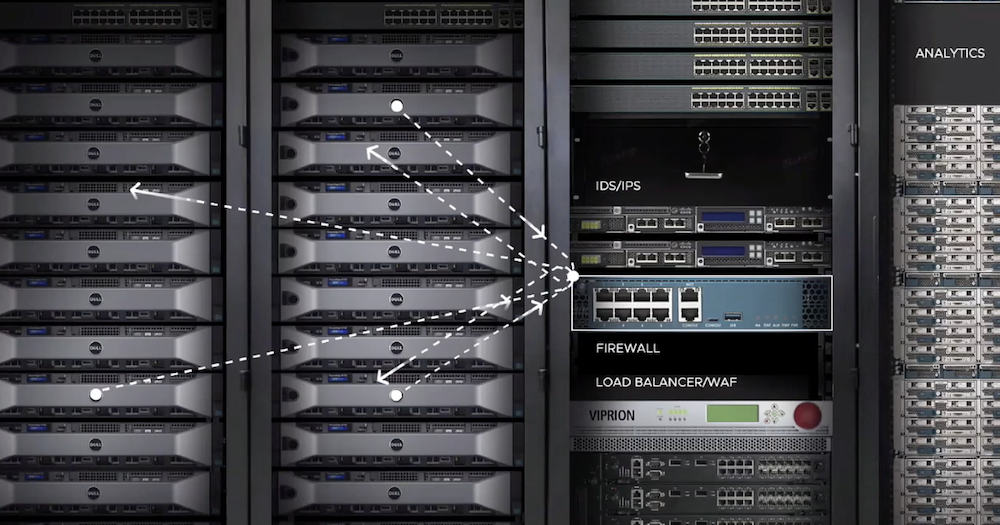
In essence, this means that you can stand up a firewall wherever your workloads are, including IDS/IPS functionality, load balancing, web application firewalling, and even analytics. Following VMware’s acquisition of Lastline, NSX also provides Advanced Threat Protection (ATP), which detects and responds to potential unauthorized attempts on the network.
Diving Deeper into NSX
During their appearance at March’s Security Field Day event, VMware’s Senior Director of Product Marketing for Network Security, Dhruv Jain, detailed the capabilities of their NSX Firewall product. According to Jain, NSX is built on the three core principles of securing East-West traffic: segmentation, distributed IPS/IDS, and NTA/NDR.
In practice, you can segment your network directly through the NSX admin console by creating security groups and assigning access policies to them, much like you would when you manage your system configurations and application access. Then, using the AI capabilities introduced by Lastline ATP, NSX analyzes your network traffic behavior, creating an application topology that sets a baseline of East-West traffic and automatically recommends segmentation policies based on the results.

In his presentation, Jain provided an important distinction of NSX: it provides up to 20 Tbps of firewalling capacity at almost a third of the cost of traditional firewalls, combining superior efficacy and control at an easy-to-swallow cost. What’s more, NSX Firewall is now a completely standalone product, so anyone can take advantage of complete control of their East-West network traffic without having to already be an NSX customer.
Zach’s Reaction
The level of control and visibility VMware’s NSX Firewall brings to the data center seems like an ideal way for enterprise organizations to ensure their East-West traffic operates both effectively and securely. And, given how widespread and distributed today’s networks need to be to accommodate for remote work, NSX makes sure that, wherever your network is needed, a firewall is there to keep traffic flow safe.
Learn more about NSX by watching the video above and the rest of VMware’s Security Field Day presentation, or by visiting their website.