The dynamic, multigenerational workforce of IT faces a gigantic obstacle. With vast differences in perspectives, belief systems and methods, these professionals struggle to connect with their peers from other teams. Especially, there is a worrying rift between security and IT, where all of IT is on one side, and the department of cybersecurity, on the other.
A Divide in Outlooks
“A big part of it comes from the fact that IT tends to open up everything to let it flow as it wants to, and not put any controls over it which can lead to chaos,” says Brian Knudtson, a long-time IT professional, author and speaker, at the Ignite Talk recorded at the recent Edge Field Day event in California.
The approach adopted by the security team is in sharp contrast to this. “Security is there to truly control things and make sure that they are moving the way they should be moving which does require saying no sometimes.”
As a result, the rest of IT often views security as the “Department of No”.
But this is more than the general lack of rapport seen between enthusiastic newcomers and long-time veterans working alongside in a team. There is a lot at stake. Present-day organizations face colossal cybersecurity threats, and if they are to thrive, teams will likely need to work closely with each other to combat the risks and support business objectives.
“We can’t look away from security when they’re trying to tell us something,” urges Knudtson. “We need to listen to them, and we need to work together in a partnership across IT, security and the business to make sure that we’re putting the whole thing together in a way that works for the business because we’re there to enable it.”
Weak communication between teams results in a bombardment of unintended consequences, and more and more security risks. Bridging that gap can not only strengthen collaboration, but also help put up a united front against the threats that face organizations.
Surmounting the Communication Barrier
But how do teams with inherently different philosophies and MOs work together harmoniously? Knudtson has a few tips and tricks to share that can encourage mutual respect and compatibility.
As noted, IT is responsible for managing a seamless flow of information, whereas security is tasked with protecting that information. If the two work synchronously keeping communications and actions aligned, they can become an undefeatable force against external threats.
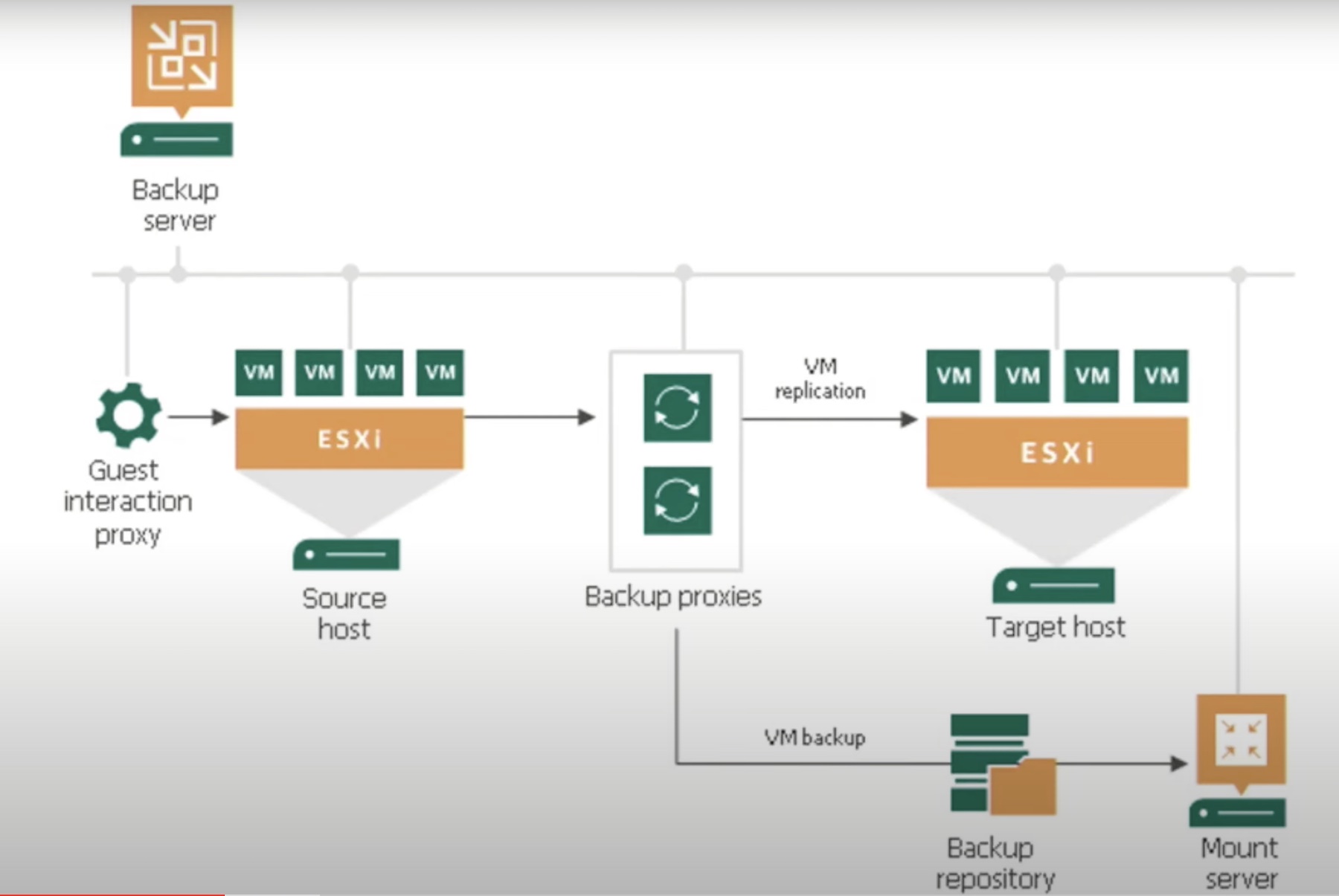
According to Knudtson, backup is where this alliance must begin. “There’s a lot of room for collaboration when we start talking about the backup infrastructure itself. There’s a lot of good data that can support security through its entire lifecycle.”
“The backup is a huge trove of information,” he says. If information found in backup like what datasets need to be backed up, or what needs restoring immediately as opposed to what can be restored last are catalogued for security teams to use, then they can build security accordingly, and deliver maximum protection.
As the IT folks process the data, they’re the first to notice red flags. “They know what normal is, and when something strange is afoot.”
By effectively sharing that information with security, they can give them a chance to investigate threats early in the attack chain and nip them in the bud.
“We can use the backup repository itself to see and run analysis within that data. That data is huge for the digital forensic side of things. The security team can go back to points in time, and find out when a threat showed up and how long it’s been there,” he emphasizes.
Several new techniques have emerged that can help implement this cooperation. Entropy detection is one such technique. It is the study of the measure of randomness vs order and is helpful to establish a baseline and spot indicators of compromise. When the IT team spots these IoCs, they can flag them so that the security team can swoop in and resolve them before they fester.
This is especially helpful when dealing with malicious bots and software. “The longer a malware sits in the environment, the further it is going to spread, the deeper it is going to go, and the harder it is going be to take out.”
By working in cahoots, the teams can cut down the dwell time in the environment and contain the blast radius early.
“We’re all Sneetches on the beach. We all have to realize that because one person in the organization has a star upon their’s, and we might not, we still need to work together because we’re still on the same team, and have the same goal which is to protect the environment and make it useful,” he concludes.
Wrapping Up
There is no denying that IT and security teams are innately different from one another. One stands for randomness, and other for restrain. But a work model that provides outlets to communicate and facilitate collaboration can ensure that the gap does not make way for the bad guys to break in. The enemy is asymmetrical, and there is a lot to lose if it wins. Only when teams can transcend their individual jobs and connect over their shared interests, can they fulfill the mission of long-term survival of the organization.
Be sure to watch Knudtson’s full presentation, and more interesting Ignite Talks from the recent Edge Field Day event.




