Microsegementation is one of the hot topics in networking today. The idea that you can essentially build a zero-trust solution with no host firewalls or hairpinning of traffic is important in the IT world we live in today. It wasn’t too long ago that everyone could safely assume that every server that needed to talk to other servers would either be physical or be based on a virtual machine of some kind. Today, those VMs might live in the cloud or they may even be ephemeral like a container. And without granular controls on those systems you can only hope that your data isn’t leaking somewhere it’s not supposed to be.
Border Controls Are Baroque
 I had a chance to sit down with Ratinder Ahuja, CEO of ShieldX, right after RSA this year. Ratinder was formerly the CTO for McAfee so he knows a thing or two about security. He told me that traditional security portfolios have a huge blind spot today. They’re all focused on border security. Stop the bad things before they get into the network. Stop the bad things from finding your files. Stop everything with devices that could potentially be bottlenecked somehow.
I had a chance to sit down with Ratinder Ahuja, CEO of ShieldX, right after RSA this year. Ratinder was formerly the CTO for McAfee so he knows a thing or two about security. He told me that traditional security portfolios have a huge blind spot today. They’re all focused on border security. Stop the bad things before they get into the network. Stop the bad things from finding your files. Stop everything with devices that could potentially be bottlenecked somehow.
Ratinder told me that the east/west traffic flow has increased over the past few years and has really accelerated security concerns, especially as we become more dependent on cloud-based solutions. Security professionals need to know which programs are talking to each other, how they are doing it, and which applications are critical for the operations of the business. You have to identify all three of those things before you can even begin to implement a security policy.
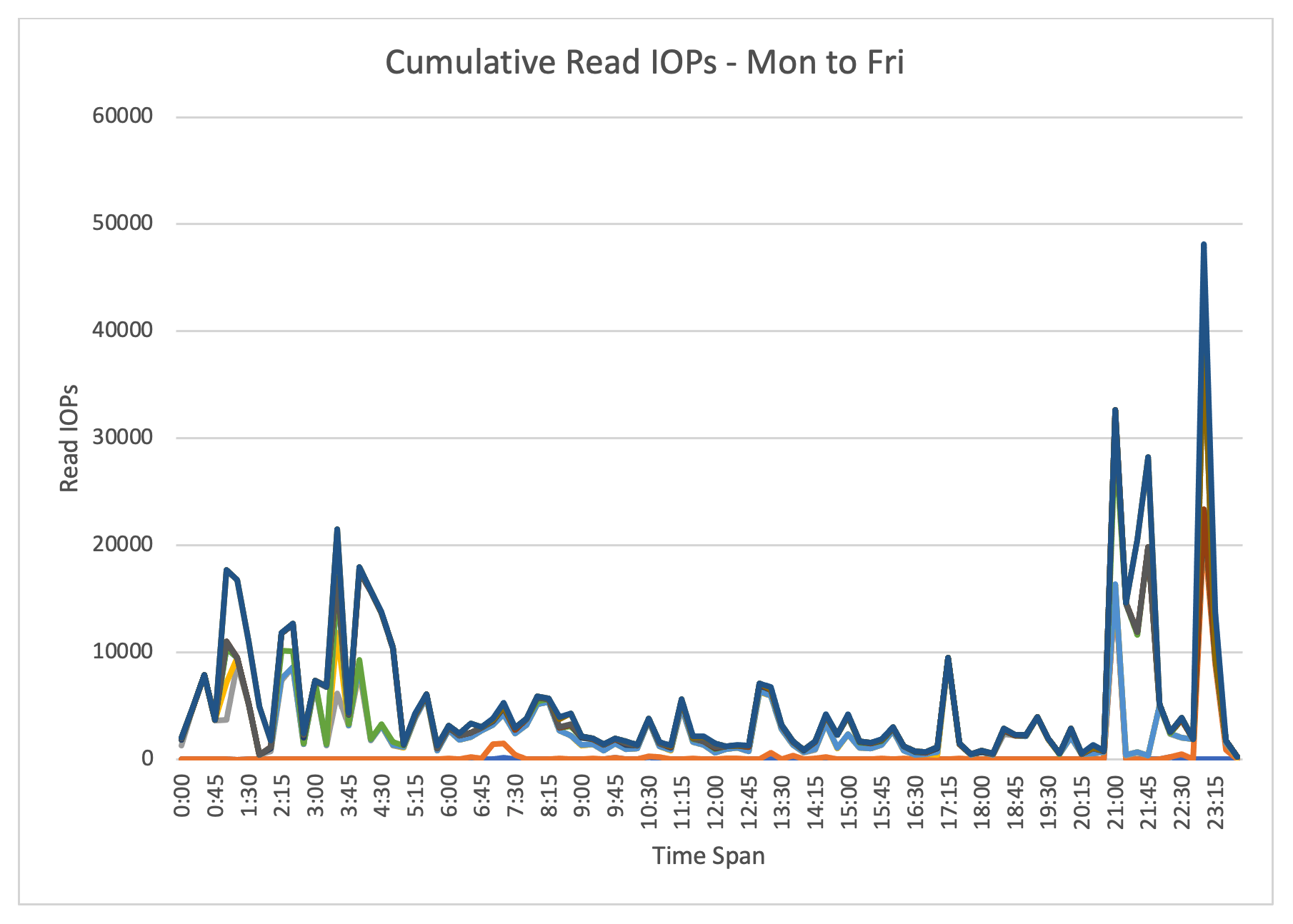
A security policy is critical to the operation of a modern network. No longer can security people think in terms of ACLs or firewall rules. Instead, you must craft a policy in more general terms and have it implemented by a solution that can scale faster than your workloads. For example, if you’re relying on your networking or security teams to add firewall rules to permit the web app tier to talk to the backend database tier as needed, what happens when you need to cloudburst 50 more servers RIGHT NOW because of a spike in demand. Even if you have a firewall rule ready to copy and implement you’re not going to be able to scale fast enough. And heaven help you if you make a typo.
Virtual Shield
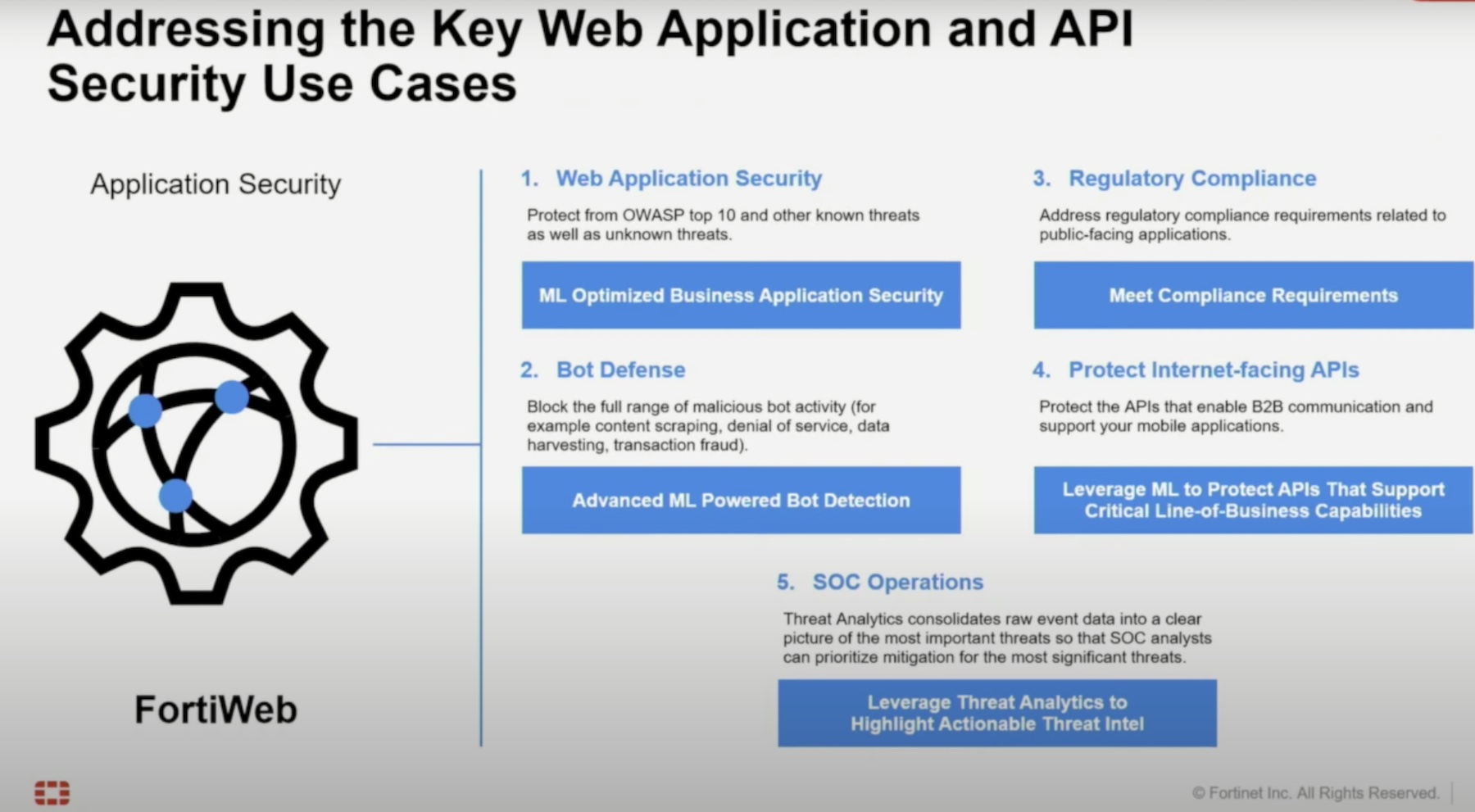
Ratinder then explained how the ShieldX solution works to eliminate these issues. ShieldX is microsegementation, but it’s focused on virtual workloads. Instead of manipulating firewall or iptables rules on the host, ShieldX does something much more novel to ensure that they capture traffic on virtual hosts.
When two hosts exchanging east/west traffic need to be protected on a virtual host, ShieldX takes a look at the virtual switch they are a part of and creates a new port group with two members – the host to be isolated and ShieldX. ShieldX is the default route for all traffic for the host. Anything leaving the protected VM has to be sent through ShieldX.
Thanks to this novel solution, ShieldX can see everything that is being sent via the machine. At first it can just be set to listen to all the traffic and identify flows. Perhaps it’s just logging all the systems that are contacting the database on the server. Once you have a list of the application usage on the host you can start crafting a security policy to allow or deny traffic based on that policy. And because those policies are created in such a way as to be able to be implemented across ShieldX systems, they can scale elastically no matter what!
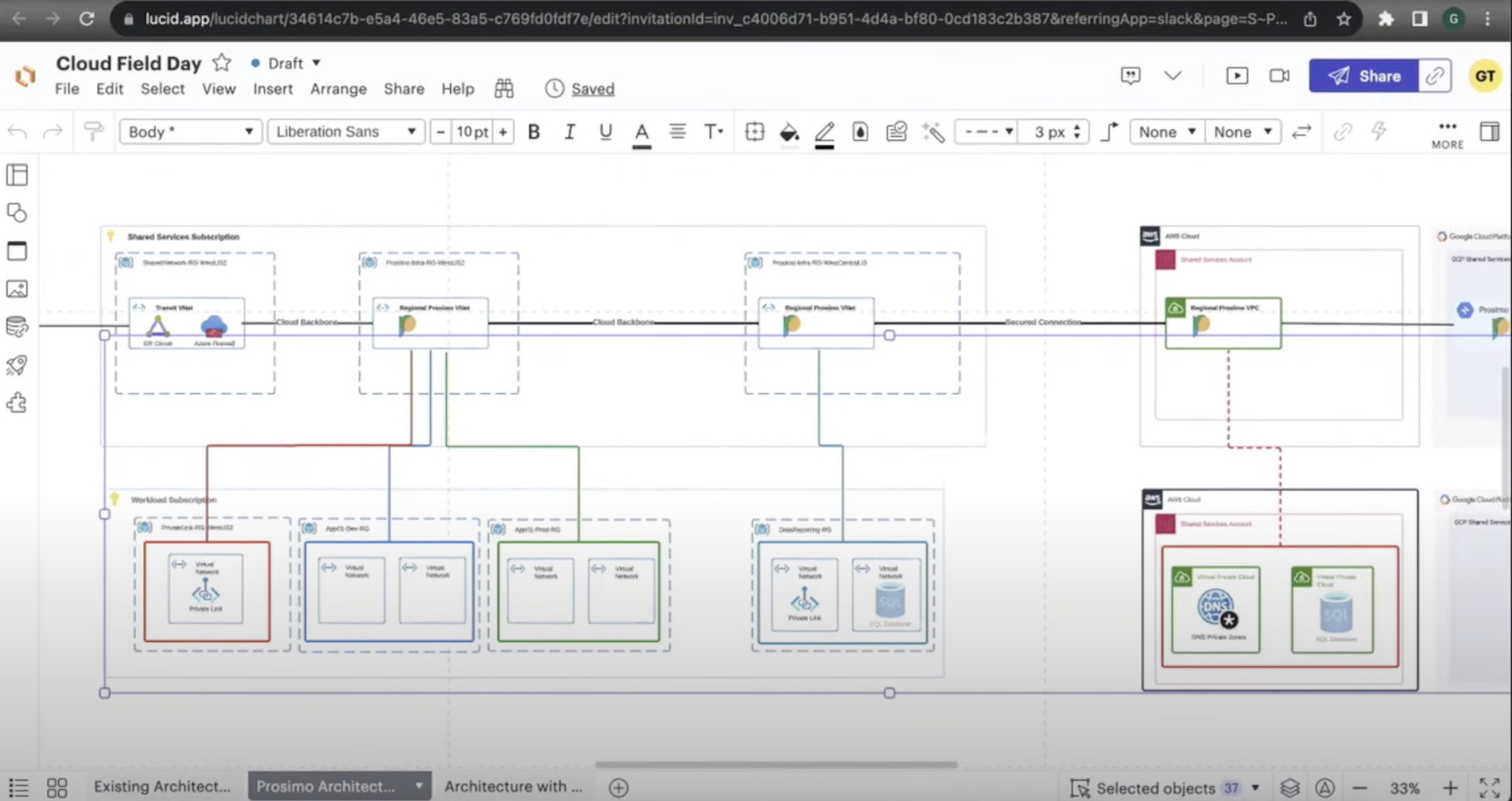
This solution also scales into the cloud. Thanks to Azure User-Defined Routes (UDR) and the ability to utilize VXLAN overlays in AWS ShieldX can protect your cloud workloads as well. The process is transparent after the initial implementation, so once you get everything up and running in your cloud of choice you can manage the entire solution from one console and implement security policy.
The best part? You don’t have to manage another cloud to make this happen. ShieldX runs as a series of containers that can spin up or down depending on the load, so it really does scale elastically with your workloads. And it uses your existing infrastructure, so you don’t have to worry about managing an AWS deployment for your security solution if you’re all-in on Azure.
Ratinder told me that ShieldX is designed for ease-of-use and operation. You could get it up and running in your environment in about 30 minutes and start analyzing traffic to create your security policy shortly thereafter. That’s a very nice way to get some feedback on your current security posture without the need to uproot your existing IT structure and spend thousands (or perhaps even millions) of dollars on a pilot program to maybe get some answers a year from now.
Bringing It All Together
ShieldX does a great job of solving the VM problem for me. With their solution focused on virtual machine traffic and cloud it makes it easy to protect your growing non-physical workloads quickly. ShieldX also has solutions for physical workloads in your data center but they really shine in the cloud with their solutions for AWS and Azure. If you’re taking a hard look at microsegmentation and you have a plan for moving everything to the cloud in the next couple of years, you should really take a look at ShieldX today.
If you’d like to learn more about ShieldX, make sure you check out their website at http://ShieldX.com. You can also check out a review of the ShieldX implementation at Alaska Airlines here.