SD-WAN has been a hot topic in the enterprise WAN for several years. But even with all the hype, SD-WAN technology has remained the territory of early adopters. Now, as the features of SD-WAN mature, a new wave of organizations are looking to implement SD-WAN technology. Nearly every company with a WAN can benefit from SD-WAN and those with strict security requirements may benefit the most.
Organizations in heavily regulated industries have struggled to find a manageable solution to secure their WAN environments. Until recently, the technologies available to provide segmentation and security for the WAN were expensive, difficult to manage, or both. Segmentation technologies available for the WAN were complex and burdensome, requiring unique configurations to be implemented by highly skilled engineers. Providing segmentation and security at each branch location often required firewalls which also need to be managed individually by highly skilled team. The lack of native encryption in WAN technologies require bolt-on certificate management systems or less secure preshared-keys to provide encryption of data in motion.
SD-WAN provides a better way to secure the WAN.

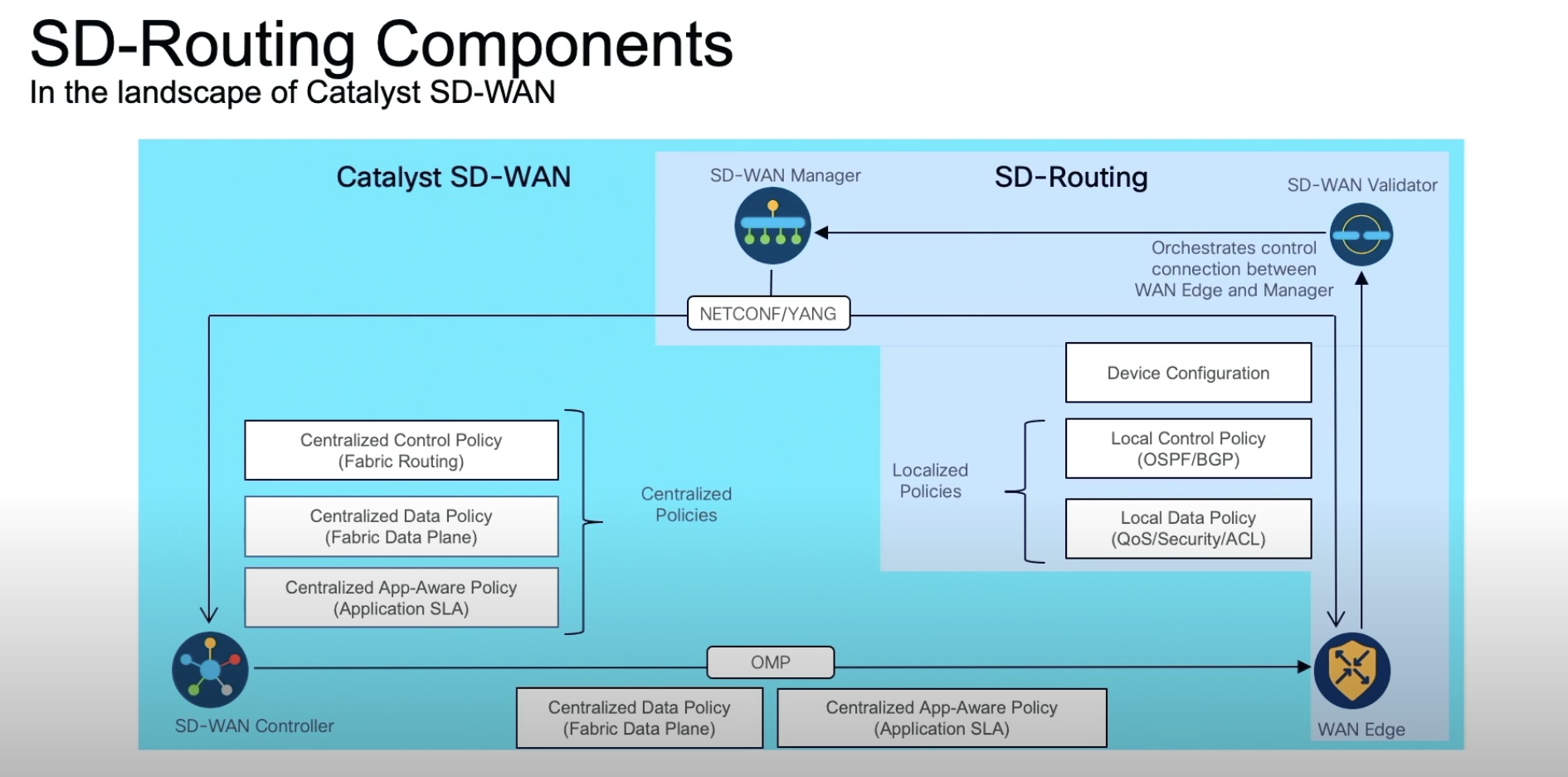
Because SD-WAN was designed from the ground up to be orchestrated from a central controller, engineers no longer need to manually configure individual devices. Templates combined with zero touch provisioning remove the risk and guess-work from device configuration. Engineers no longer need to worry that a forgotten access list or a typo in configuration will introduce a security risk into their organization. Templates provide an auditable, reliable framework to ensure consistent application of security policy for the entire WAN.
The need for WAN segmentation, especially in highly regulated industries, has never been higher. In certain organizations like health care, insecure devices provide mission critical functions but cannot be patched. Preventing lateral movement from insecure devices on the legacy WAN requires laborious and error prone manual configuration or expensive firewall hardware at each site. With SD-WAN, the network can be segmented across the entire fabric with straightforward changes to a centralized template. Policy drives the connectivity model and will determine which WAN segments can talk to other segments.
As the security landscape changes, organizations have a renewed need to encrypt traffic in motion, even over private networks. However, the administrative overhead to maintain IPSEC tunnels across the WAN, especially with certificates or unique keys, has been prohibitive for many organizations. SD-WAN eliminates the administrative burden by building encryption into the WAN. Certificates are managed by a central controller, no external PKI required. Encryption is enabled by default making configuration a no-brainer.
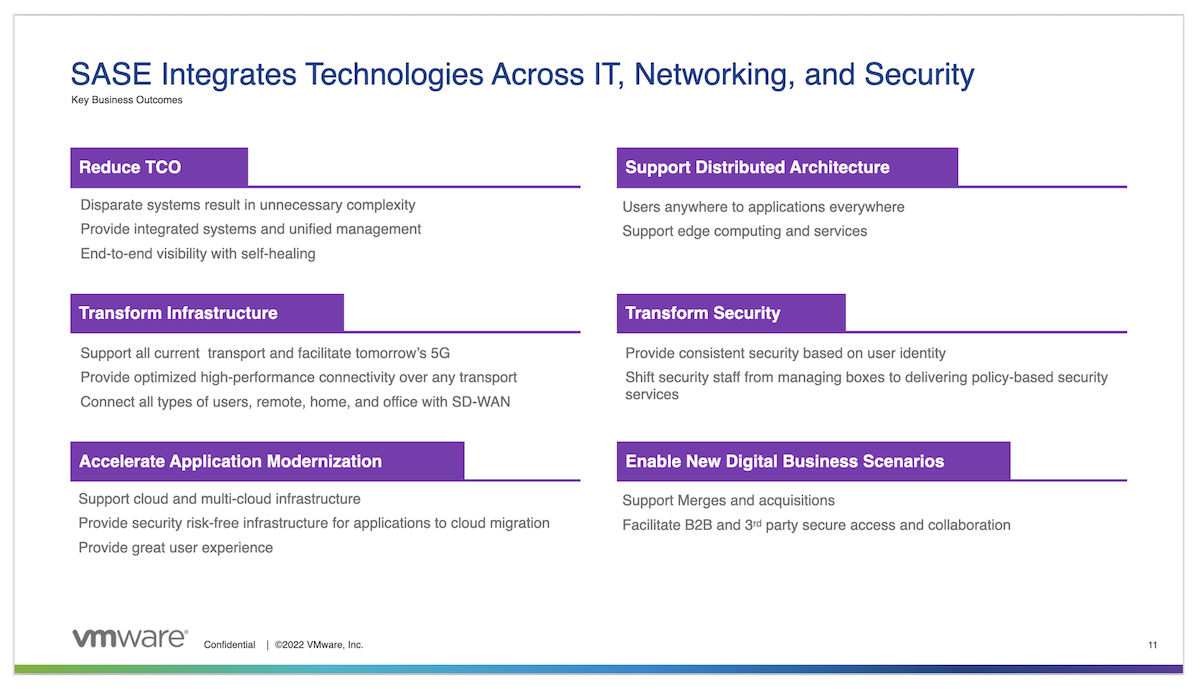
The combined features of SD-WAN, including centralized orchestration, easy fabric-wide segmentation, and built-in encryption make the WAN more secure than ever. Organizations are finding the security capabilities of SD-WAN incorporated with features likes transport independence, intelligent traffic steering, and built-in redundancy are too compelling to ignore for their next WAN refresh.