One of the fundamental tenets of SD-WAN is transport independence. This has the potential to change the underlying security model of your organization’s wide-area network (WAN) because there are new potential attack surfaces to consider. As organizations move away from dedicated private connections to broadband and wireless Internet-based transports, security becomes even more fundamental to ongoing WAN operation.
For many years, most enterprises have used a “traditional” model of private or leased lines along with a transport such as MPLS (whether Layer 2 or Layer 3 VPN). These circuits generally do not connect directly to the Internet and are instead privately tunneled over the carrier’s backbone network. Your organization’s traffic is not seen by any other organization, unless special arrangements are made (such as the case of a private extranet). Due to this inherent privacy, organizations might not even bother encrypting their traffic as it transits the carrier network, because it is expected to be isolated from all other customers.
This model changes when using SD-WAN with the general Internet as your transport. SD-WAN achieves transport independence by working across any kind of connection, such as cable or DSL broadband, direct Internet access (DIA), 4G/LTE, and soon 5G wireless. SD-WAN can even work with traditional private MPLS circuits, depending on the configuration. When using the Internet for transport, the nearly-universal underlying protocol is IPsec.
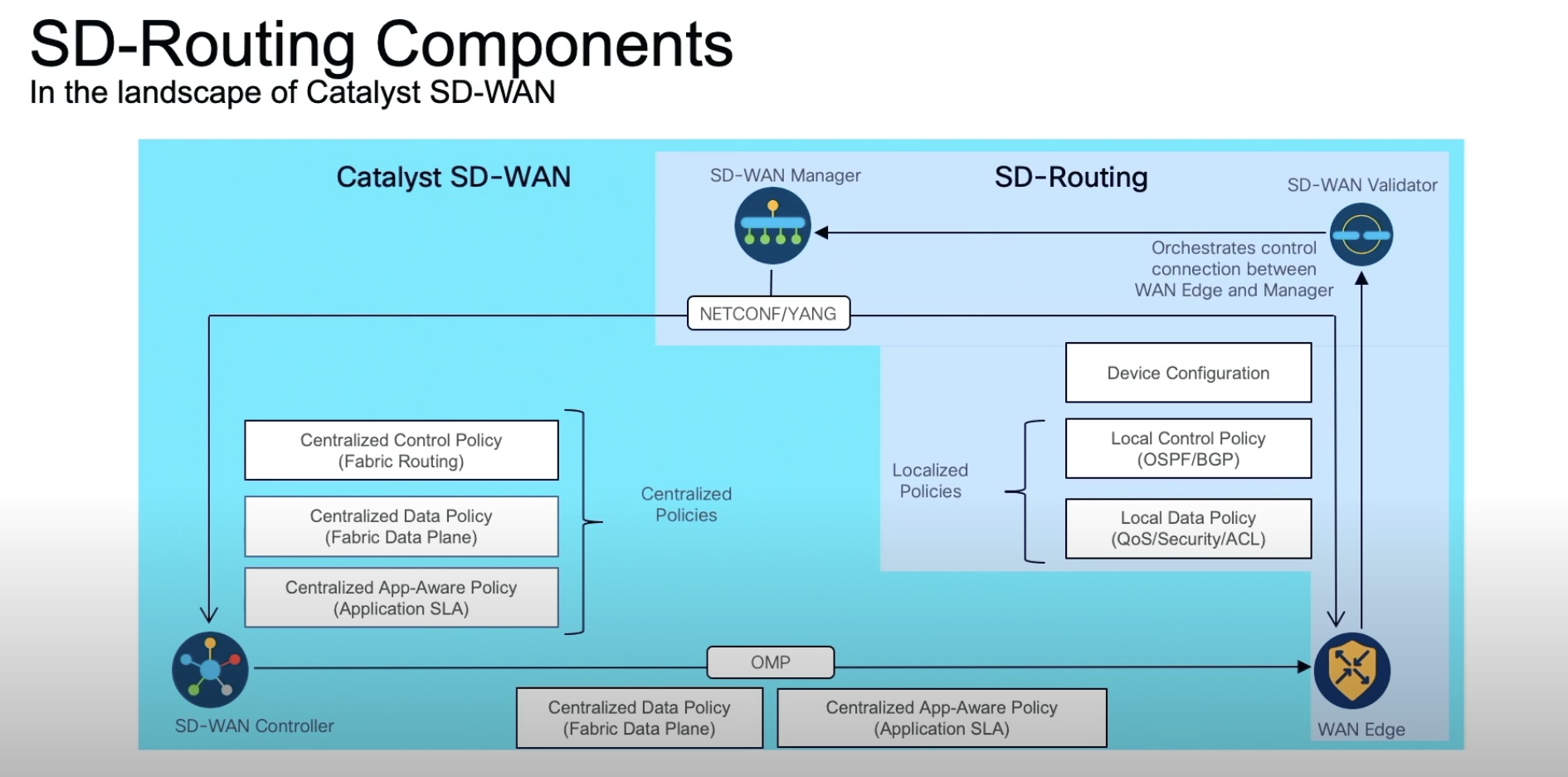
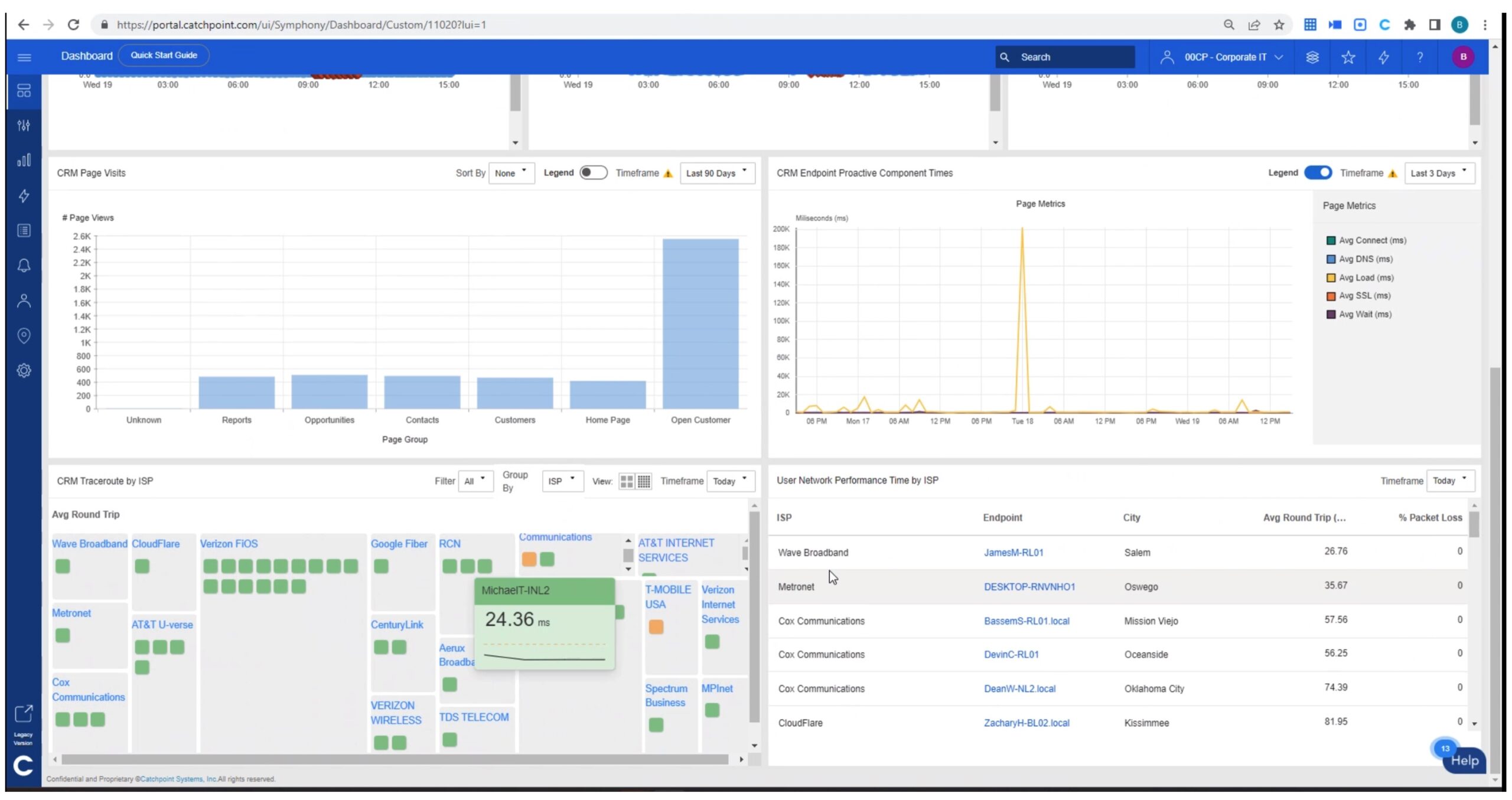
Traditional devices such as firewalls and higher-end routers have had the ability to use IPsec VPNs for many years. SD-WAN adds new capabilities to the operation. Most SD-WAN edge devices communicate with one or more centralized controllers to orchestrate the automated setup and teardown of site-to-site IPsec tunnels. SD-WAN also adds measuring and reporting capabilities on the performance of individual links and can tailor the sending of traffic based on business policy. A common example is to automatically send all VoIP traffic over the connection that is measured with the lowest latency and jitter, and send bulk traffic over faster, but potentially worse-performing links.
SD-WAN increases the potential attack surface when using Internet-based transport. Many organizations have used an “Internet backhaul” model where each location receives Internet access through a centralized point, whether they are connected by private MPLS circuits or using a firewall with an IPsec VPN. This model has the advantage of utilizing simpler policies with fewer points of interaction at the expense of larger, more expensive centralized firewalls and frequently sub-optimal traffic.
For example, if a branch located on the West coast of the U.S. needs to access an Internet resource also located on the West coast, but the company backhauls all traffic through a datacenter on the East coast, traffic must traverse the entire country twice. No matter how fast your connection is, you still have propagation delay as your packets make a 6,000-mile journey across the country and back.
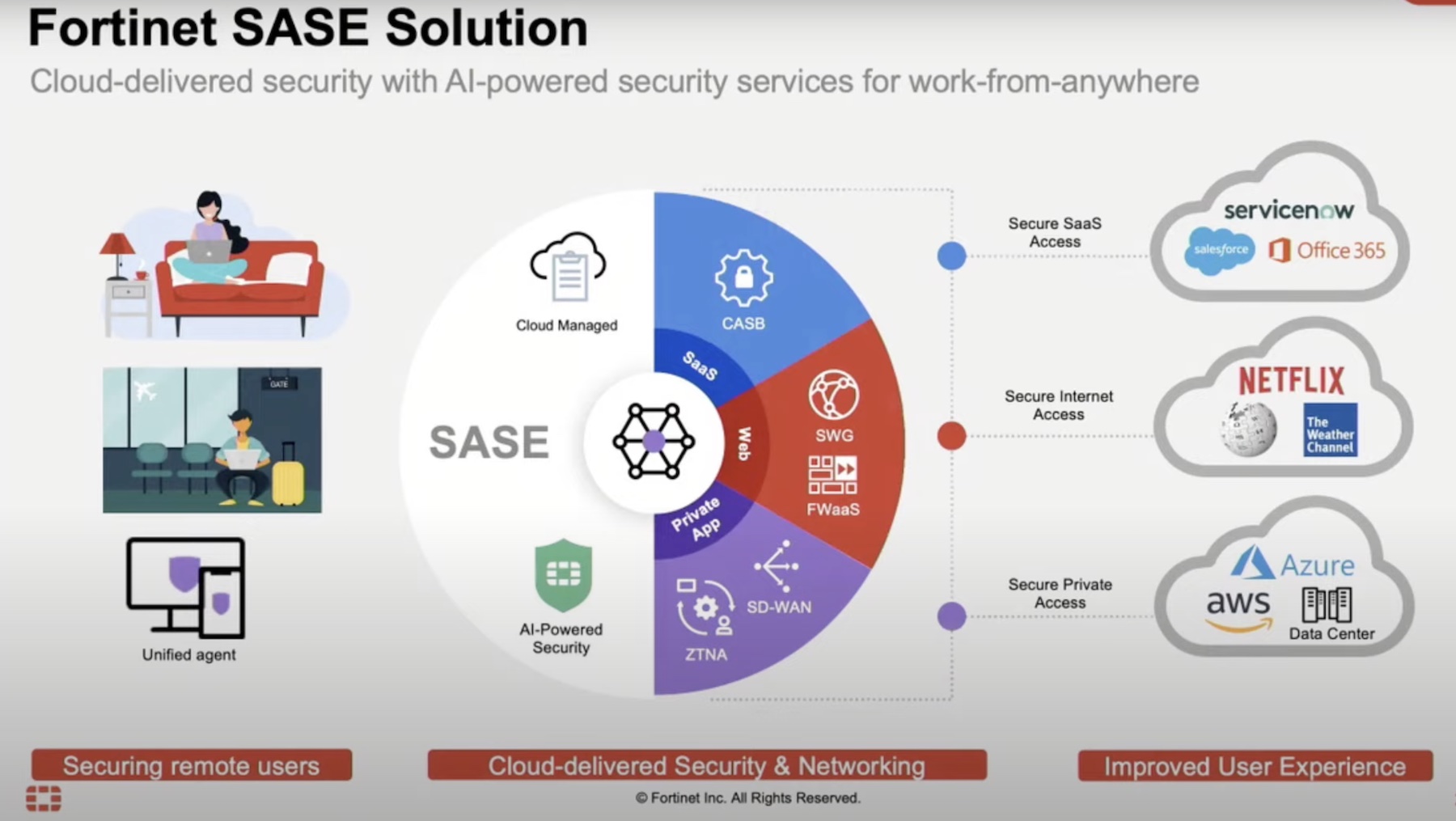
Many SD-WAN platforms have the concept of local Internet breakout, most of which operate on a “whitelist” model. With this operational model, you can define Internet resources for which the SD-WAN edge device will attempt to connect directly over the local Internet connections, instead of forcing the traffic over the IPsec backhaul to the organization’s centralized firewalls. For example, if your company uses trusted Internet-based SaaS platforms, you can define policies so that users connecting to those services from within the branch office connect directly through the Internet.
This type of connectivity was previously possible in the traditional model where branch locations were serviced by local Internet connections fronted by local firewalls. However, SD-WAN adds the orchestration element that is key to reducing administrative overhead in this scenario. Using the SD-WAN platform’s orchestration engine, you can create simple, customized policies that automatically propagate to all edge devices defined in the policy. Previously, if you wanted to add or remove a SaaS platform or website from being accessible locally, you would have had to individually modify each firewall. With SD-WAN orchestration built-in, this becomes a non-issue.
While SD-WAN has become a more mature technology over the past few years, many enterprise organizations would rather take a more cautious approach with regard to security and stick with the model they know and trust. That model is frequently centralized Internet access, despite SD-WAN offering easy local Internet breakout. With time, companies will learn to trust SD-WAN and adapt to the new security paradigm, which will lessen suboptimal Internet-bound traffic and increase overall performance.