The world is seeing an explosion in IoT devices. When the term IoT comes up in discussions, the most likely device that pops into mind is a thermostat or a light bulb. However, the largest number of IoT devices in the world today are in the medical field. Healthcare is a technology playground, and the amount of information gathered by IoT devices is impressive.
Healthcare is a vertical that has a significant amount of regulatory security. Health records are a highly protected resource thanks to HIPAA, so it makes sense that the data collected to build those records should be just as protected. Being able to intercept that data could be a goldmine for nefarious actors looking to build ransomware. With IoT, you need to get to that data before it’s sent.
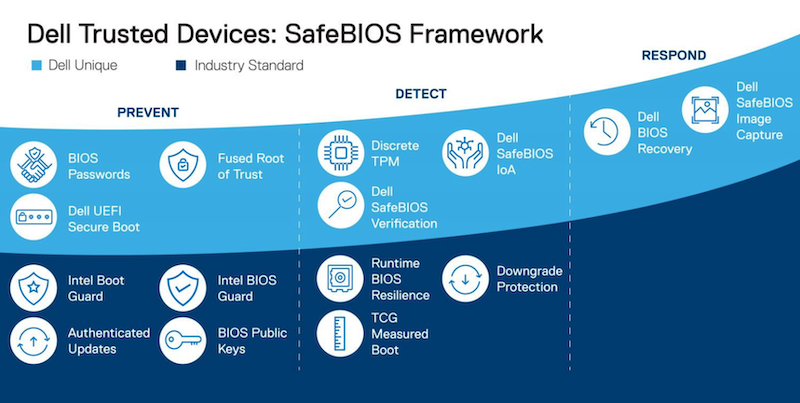
Compromising IoT devices is the new attack du jour. Suppose you can create firmware that will give you the ability to persist on devices with little to no management capability. In that case, you have a foothold that will provide you with a window into all kinds of possibilities. After all, who would think to check a glucose monitor or a blood pressure cuff for malware? Ensuring that your IoT devices are safe and secure is something that every healthcare IT admin should be worried about.
VMware Edge Network Intelligence Solves Assurance Worries
Enter VMware and Nyansa (now VMware Edge Network Intelligence). Nyansa is a company that has focused on providing great analytics, and VMware picked it up to bring that expertise into the fold of its Edge Network Intelligence (ENI) platform. The idea behind leveraging ENI to secure IoT devices is essential because the platform can use the advantages provided by VMware Edge Network Intelligence to fulfill the five key points of the IoT Operational Lifecycle:
- Inventory – What devices are in operation on the network?
- Performance – Are those devices connected and working correctly?
- Baseline – What does normal look like on this network?
- Mitigation – If something deviates from the baseline, what happens?
- Prevention – How do we keep things from violating policies?
Each of these points is a place for a well-constructed ENI solution to help with IoT. It is imperative to make sure the baseline is appropriately set in a healthcare environment to ensure that deviations are caught and analyzed. Because of the nature of the devices providing care, you need to ensure that you’re handling exceptions correctly. They must be documented and dealt with according to policy. You don’t want to shut off an insulin pump that starts making weird requests. The device itself needs to still function. However, you do want to know what’s going on and deal with it during downtime. Or deal with it by taking the device out of production.
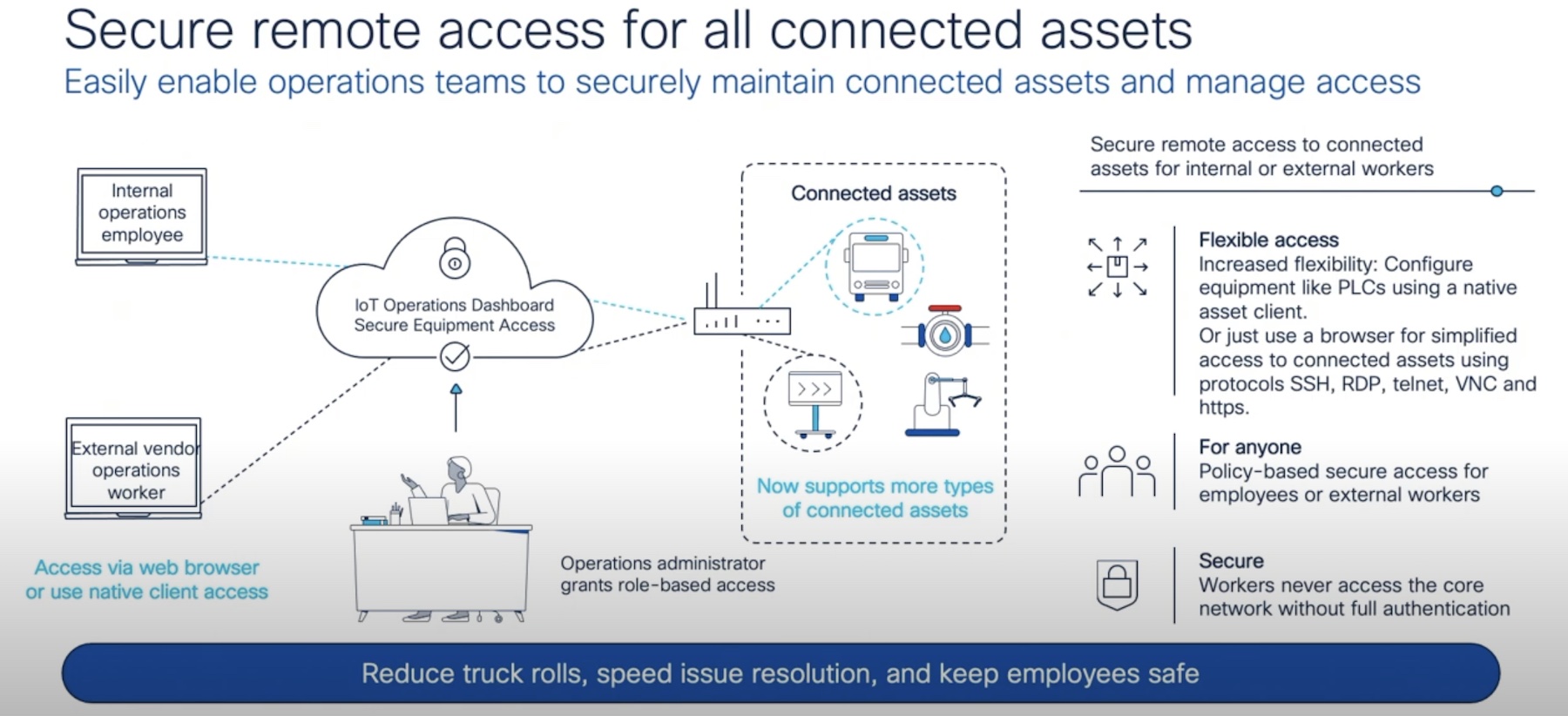
Because IoT devices’ attack surface is growing every day, operations teams need to have eyes on them. They need to understand the challenges of isolating these devices and monitoring their communications to ensure that nothing is happening to create potential exposure.
A blood pressure monitor has a specific list of systems it should talk to. It should never be attempting to send a massive amount of data outside of the network. Compromising internal IoT devices that seem invisible to the rest of the IT staff is a great way to gain a foothold to exfiltrate data for future ransomware campaigns. You need a solution that helps with all the aspects of the lifecycle to spot these attempts to subvert your devices before you’re exposed and liable.
For highly regulated environments, like healthcare, you need to have a solution in place to reduce your potential exposure. If you don’t, you need to stop what you’re doing and look at VMware’s ENI solution.
The hope is that by deploying it now to manage your growing IoT footprint, you won’t ever need the advanced reporting capabilities to determine when you’ve been breached. Better to have it now and ensure you’re on top of the problems before you need to write up reports to the risk auditors later.