Enterprises are competing with each other over tightening supply of cybersecurity skills. The shortage has intensified over the past few years and is now tantamount to 3.5 million unfulfilled positions. Needless to say, hiring is a challenge in this climate. But fortunately, there’s automation to bring closure to the widening talent gap.
In November’s Security Field Day event, security automation was one of the top topics, and Swimlane dominated the conversation with a series of presentations focused on automation. In one of the sessions, they presented their five-level SecOps Automation Maturity Model that is designed to eliminate dependency on skilled workers, and harness the full power of automation.
The Struggle to Woo Qualified Talent
The threat landscape has assumed a dire form in a very short time pressing it upon organizations to reinforce their infrastructures. Wary of the spike in malicious cyber activities, companies turn to the labor market in hopes of finding qualified professionals to expand the workforce, only to find that skills are in short supply.
The only way to overcome the talent gap is to load up on security tools. But contrary to expectations, overloading the arsenal produces very opposite results. Brimming with swanky tools and solutions, companies now have a new problem. Too many tools create an alert storm obfuscating key indicators and obstructing timely responses. So, on top of being short-staffed, they now have SecOps teams that are beleaguered and burnt-out. This has translated to higher employee turnover rates bringing enterprises back to where they began.
Averting the Crisis
Having witnessed the crisis unfold from inside the industry, Swimlane is motivated to forge a solution that’d put an end to the longstanding struggle. Knowing that in cybersecurity, devil is in the data, Swimlane sets out to build a system of record that, for one, gives organizations assimilated intelligence in a central location, and for another, helps identify what’s happening in their environment and what they need to do through various stages of automation.
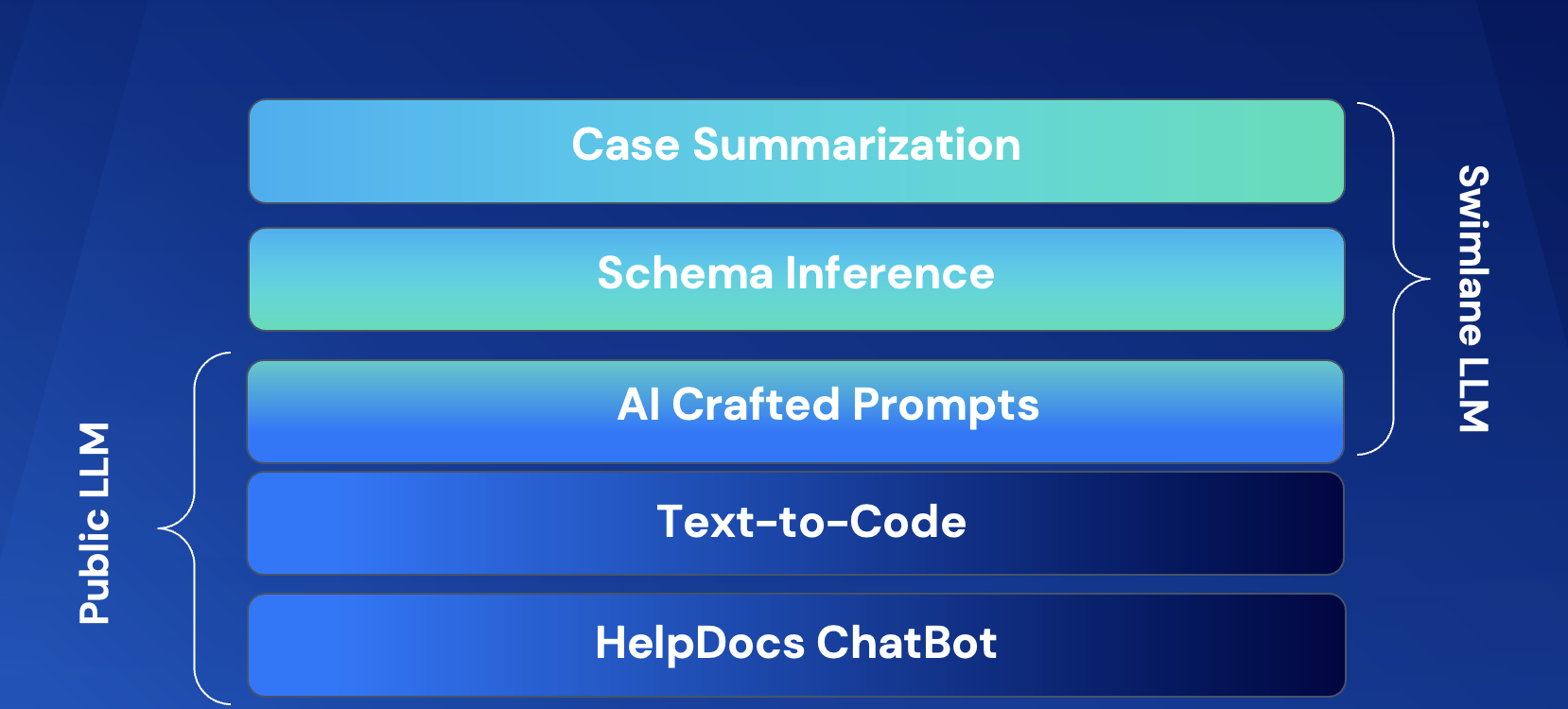
Swimlane’s is a “low-code” automation platform that provides a full system of record. Fully extensible, it comes with an easy-to-use workflow builder for automating responses. Cody Cornell, Co-Founder & Chief Strategy Officer points out the three building blocks of the platform – automation, integration and visualization.
Cornell says, “A lot of the folks talk about low code but it’s usually a playbook builder or a dag (Directed Acyclic Graphs) that people are going to build from a workflow perspective on how they actually are going to automate. But our low code component actually moves into the user experience as well.”
The platform has a scalable integration fabric that features hundreds of pre-built integrations which takes the pressure off the developers. “It’s tied into hundreds and hundreds of security and non-security integrations that are in our marketplace,” informs Cornell.
Swimlane features landing page for different personas working in organizations to help knock down the silos between departments.
Swimlane’s Security Automation Maturity Model
At the recent Security Field Day event, presenters Cody Cornell, and Bryon Page, Director of Solutions Architecture at Swimlane, gave a closer look at the Swimlane SecOps Automation Maturity Model and wrapped it up with a demo of Swimlane.
The SecOps Automation Maturity Model is a newly introduced framework that is built to help organizations “understand what they need to do to mature an operations program”. Up close, the model reveals five stages or levels, namely – Foundational Visibility, Enriched Visibility, Automated Response, Automated Prevention and Expanded SecOps Automation.
Focused on security automation, the model is aligned to popular security frameworks like NIST, D3FEND, ATT&CK and C2M2, and industry best practices. Swimlane breaks down the metrics into four broad categories – Case Management, Enrichment and Mapping, Response and Improvement to help organizations evaluate their security posture and locate where they are in the spectrum.
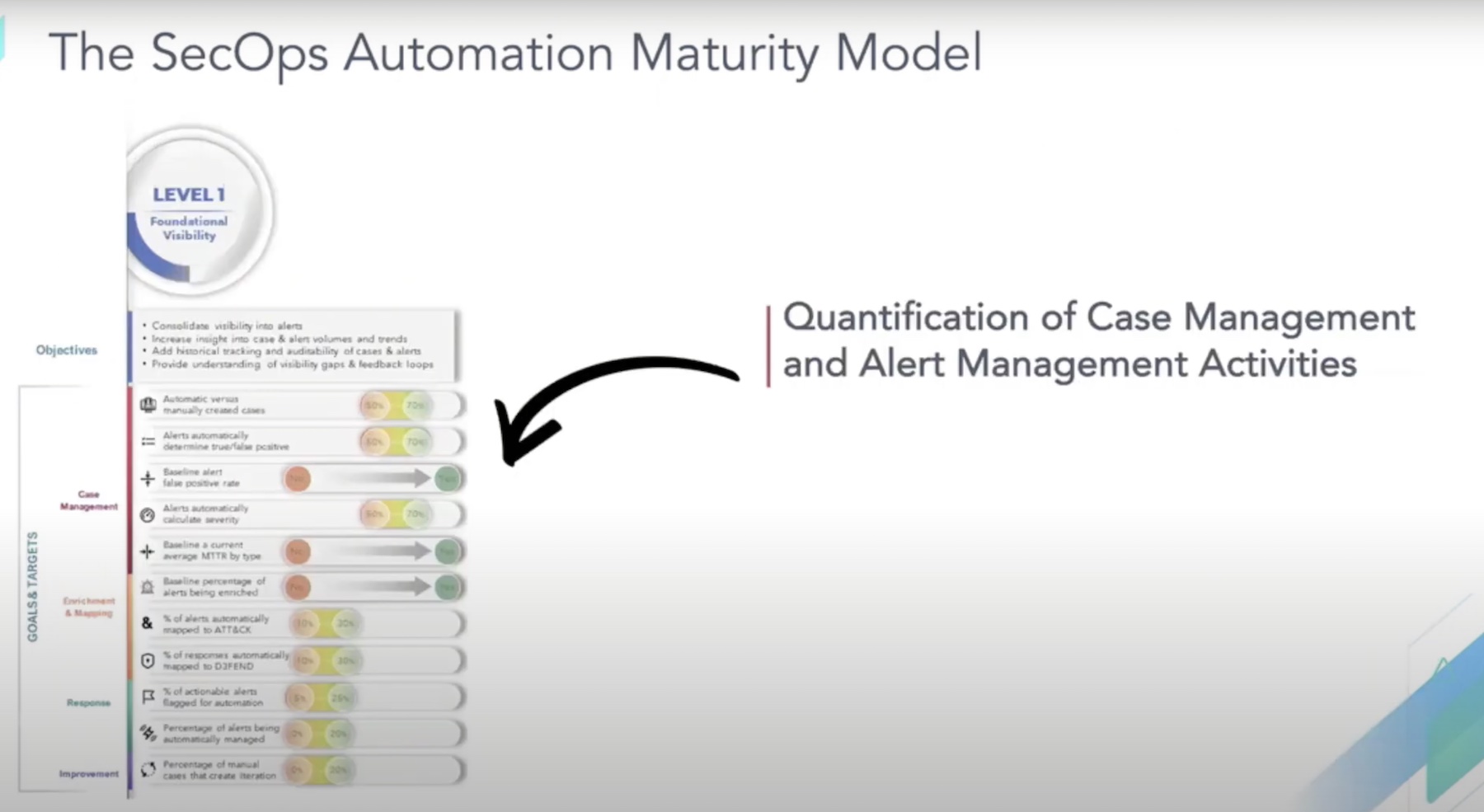
To make the model quantifiable, Swimlane has a set of objectives and goals for each program. For example, for Level 1 which is Foundational Visibility, the overall goal is to assimilate all of the intelligence into alerts and churn out maximum insights out of the data.
As part of alert management, this stage helps determine what measurements and metrics should an organization be looking at and understand how to enrich the data that decisions could be based upon, or used to automate a response in the later stages. A feedback loop provides information to reduce false negatives and enrich the investigation cycle. Since the first two stages are prelude to the automation stage, in preparation, the metrics at this level help sort out the alerts that can be potentially automated.
Cornell elaborated that the five programs and their parameters are all purposed to figure out “what the maturity is typically along these metrics and then map it to all the other frameworks that are out there that enterprises are leveraging.”
Wrapping Up
Reducing cybersecurity headcount without sacrificing the quality of protection is a balancing act companies are yet to master. Security automation surely presents a solution, but it is still in its early days. With a nuanced security maturity framework like Swimlane’s, the mission to stay compliant and protected from bad behavior through automated security is much closer to enterprises. It shows what security automation can look like if done right, and the way to do it.
For more information on Swimlane’s SecOps Automation Maturity Model, be sure to check out other presentations by Swimlane at the recent Security Field Day event.