Reports published last year states that nearly 500 million ransomware breaches were recorded worldwide in 2022. Researchers predict that this year’s number will top that out making ransomware one of the most pressing issues at hand.
A Compounding Problem
Both big and small size companies have experienced breaches over the last year. The attacks have had several causes. A leading one among them is surface exposures caused by errors and oversights that unexpectedly led to catastrophic outcomes.
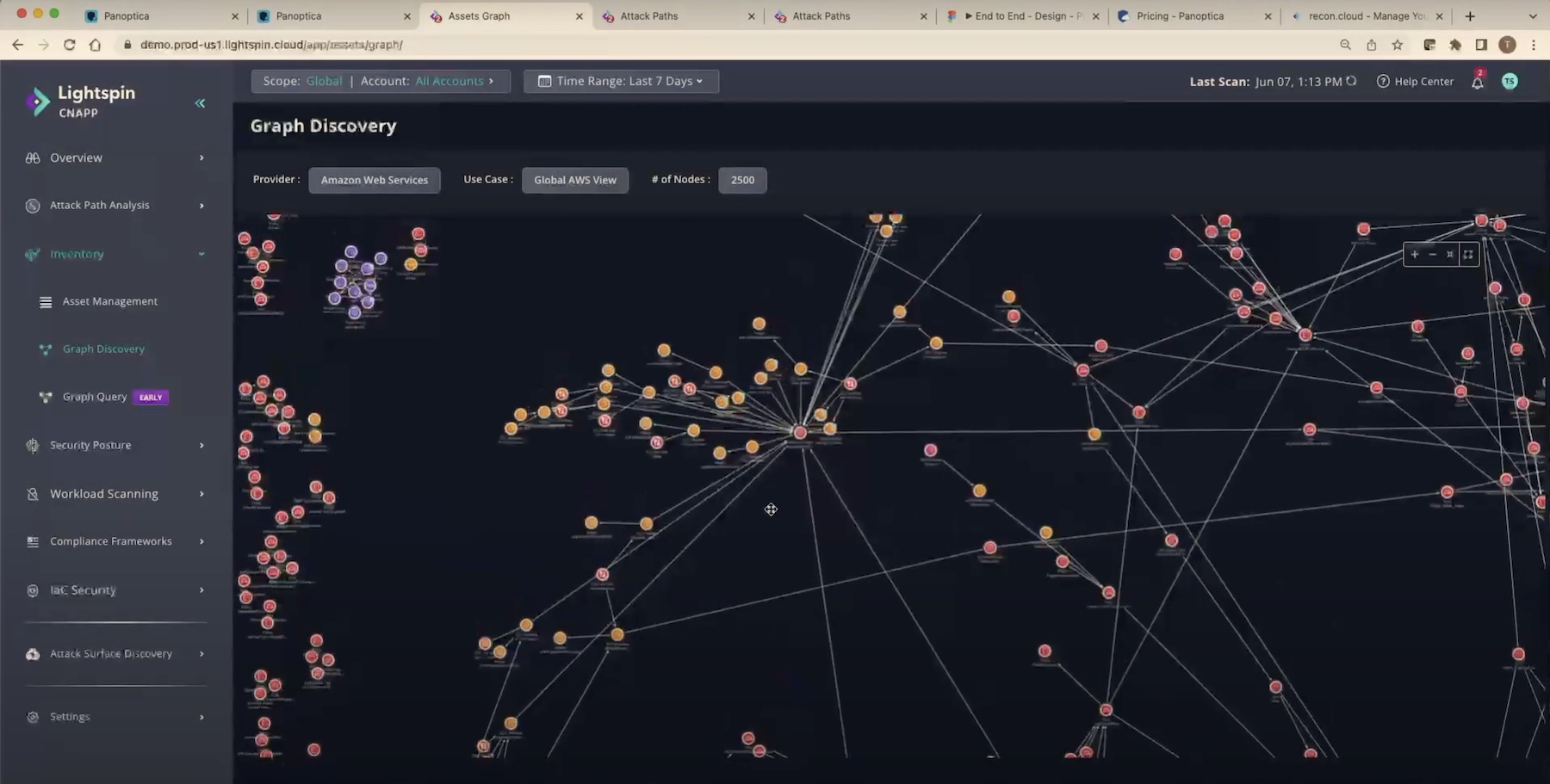
This, in no small part, is due to the exponential growth of networks. The network size and resources have approached infinity in a short few years sending open invitations to unscrupulous entities. Any random person with a little skill and a plan can sneak in and make off with valuable data. And so they have, running up the average cost of a data breach recovery to $4.35 million, according to IBM.
There’s growing anxiety among security professionals that corporate networks have become too large and too dense to fully secure. As companies dramatically punch above their weight adding and building more network assets, cybersecurity has become knottier.
Ask a security professional what’s their job like, and they’ll tell you it’s hard, without missing a beat.
“Sometimes it just seems like a little too much. All the things we have to worry about just when we think we’ve protected everything we could possibly protect. Then there’s a new wave that comes along and someone figures out how to backdoor something, and now we got another vector we have to worry about,” voiced Tom Hollingsworth, Network Engineer, at the recent Security Field Day event.
The situation is escalated by an ongoing skill shortage that is gripping North American companies. It is exceedingly hard to find qualified personnel to hire in security. Left on their own, existing teams are scrambling to cope with the work overload and attention overwhelm brought on by near-unlimited network resources and accesses.
Inspecting with a Closer Eye
Before wrapping up at the Security Field Day event in California, the attending delegates got together to hack into the security situation, and voice their opinions. The participants split into two schools of thought. One school believed that security is a double-edged sword.
Karen Lopez, Architect, kicked off the debate by stating that although indubitably non-negotiable, security is a drag on IT processes. She explains, the endless routine of authentication and verification creates a resistance from within that accumulates to delays and stops, and is viewed as an encumbrance on all of IT.
It gets worse, weighs in Ed Weadon, Network Engineer. Every time a new model or a new solution is adopted, things screech to a halt causing company-wide anxiety and unsettlement.
It’s no secret that as enterprises shift towards new models like the zero-trust network access model, the rest of IT follows kicking and screaming. “It is a massive paradigm shift for a lot of organizations in the way they work today,” he commented.
Department of Nothing
In enterprises, security is often one of the most undervalued teams. Increasingly, the public attitude is becoming harsher. Always the first to fall into disfavor when something goes kaput, their unpopularity is often unexplainable.
The real reason security teams are the target of ire is because not enough people understand that security is imperfect by design. For security specialists, a majority of the time, it’s skating on thin ice. It’s Murphy’s law everyday – anything that can go wrong will go wrong. While there are ways to prevent the preventable, there is no silver bullet, and that is security’s biggest Achille’s heel.
Other times, the disapproval comes from a general dislike for the rigorous security routine which is a burden on the operations team. But ironically, no sooner than a breach happens, the whole company comes down on the security people for not doing their job right. They end up getting flak for doing their job, and grief for not doing it right.
Safe to say that there is nearly not enough awareness within the organization when it comes to security.
Hollingsworth pointed out that security is a work in progress, and not a finished assignment. “No organization – not even the NSA – started off with a fully-developed, multilayer security controls. It’s just boiling a frog, we’re going to add one more thing, and another,” he reminded.
Teams need to come together to make security a concerted push because no one team can make the network safe, not when everybody else is busy playing the blame game. To that end, enterprises must work on elevating awareness about the importance and nuances of security, and forge a more cohesive culture internally.
Security is Unobtanium
While one camp debated the workings of security, the other camp took to dissecting the design. “Security is unobtanium,” says Alex Neihaus, Cloud Infrastructure Architect.
Neihaus cited a couple reasons for this. According to Neihaus, the fact that the internet has been insecure at birth is the mother of all evil. “We built a worldwide network of networks, the Internet, on a fundamentally unauthenticated, unsecured packet switch network,” he reminded.

While it’s a bit too late to change that now, the second major problem adding to the insecurity of the internet is that it’s impossible to teach its ginormous user base how to adopt caution while using the public internet. So enterprises resort to embracing new technologies that are no more than putting band aids on wounds because they cannot be healed from within.
“It’s a Gordian knot. It is really hard to do the right thing consistently right because you have humans and you have bad tech bottom line,” he added.
Niehaus’ frustration is shared by Lopez who extended the argument to describe modern technologies. “Almost every technology that we, as a society, deploy, is based on an assumption that there are no bad actors that would ever want to compromise it, or worse, make money from it,” she said.
Email is a classic example of that. “The reason spam works is because the barrier to entry is invisible, and it costs almost nothing to send emails. Then we spent two decades trying to make anti-spam measures work, and now we know we can’t really stop people from sending things. We can only block it at some giant firewall, and we continue to do it for every new social media thing or every new product that comes out,” she noted.
Engineer out the Stupid
Tying it to the point made earlier, one of the things keeping security professionals up at night is insider threats. Increasingly, security teams are finding small and silly errors at the source of major leaks and exploits. Employees are unwittingly manufacturing threat vectors inside the network making attacks more probably.
Training the workforce to rigorously follow security measures, such avoiding putting workloads in open buckets and saving company secrets in vulnerable locations, have been an uphill battle for SecOps.
Lately, security departments have taken to running practice exercises and surprise drills to measure and test employees’ security skills and prime them for real-life threats. This has been helpful so far in keeping the staff within the prescribed bounds, and deal with threats more proactively and aggressively.
Additionally, it is helpful when vendors package and market their products responsibly. Instead of bluntly attempting to upsell by obfuscating real use cases – which they are wont to do – when providers start to describe their wares accurately, buyers can have greater clarity and make better buying decisions.
A Legal Wrangling
More friction is caused when C-Suite executives show unwillingness to bankroll the toolchain that security teams say they require, unless they see a financial incentive for acquiring it. The panel highlighted that a lot of the times, organizations create cultures of ROI-focused decision-making that undermine ground-level problems and overemphasize on revenue outcomes.
This bought the discussion full circle to compliance and what it means for enterprises.
Lopez pointed out that there’s rarely any mention of punitive or compensatory damages in the cyberattack news. She reminded that big corporations have a suspiciously high rate of success with evading legal penalties for data protection violations, something that softens their liability to the public.
Thousands of data breach incidents go unreported annually as companies go out of the way to avoid regulatory penalties and harm to reputation. In the past, findings of unauthorized data collection for marketing purposes have also created significant uproar in the media. News companies and activists have decried it actively but it hasn’t put a stopper on the problem. It has only made organizations more wary and peddling of customer information continues to this day. Egregiously, firms have gotten away with making compensatory offers of small sums of money and free merchandise for the violations.
Although there have been class-action lawsuits against organizations playing fast and loose with public information, and there is always a reputational cost associated with incidents of data breach, one can’t help but wonder if that is reason enough for companies to crank up their policies and meet compliance to a tee.
Part of how some companies afford to skip past compliance is because they know that the damages are temporary, and no bigger punitive cost is owed. They are resolved to seeing security as a cost center, and the only way to change their perspective is to convince them that it is a necessary investment to drive up efficiency and productivity.
Neihaus reminded the panel that the government of United States has cracked down on several such cases with a flurry of actions – the Wells Fargo case being a notable example. But despite the levied fines and criticism, the question lingers – “how does one solve an insoluble problem to the satisfaction of the government?”.
Wrapping up
As Neihaus said, “We are yet to atone for our sin of putting worlds’ business on a publicly shared network”. But what organizations can do is make better choices of tools, do internal drills and trainings to make the average employee adjust better to security protocols, and share information that makes security specialists look less like enemies and more like the guardians that they are. Doing these systemically and synchronically can remove a lot of the obstacles and frictions in that path of security specialists and see to it that cyber resilience is assured at the end of the day. After all, helping them do what they do best is in the best interest of every individual in the organization.
Be sure to watch the full discussion and several interesting presentations from the Security Field Day event on the Tech Field Day website.