Did you hear the big announcement from AWS re:Invent 2021? I’m sure you’re trying to remember what the “big” one was, but for me it was the preview of Amazon Private 5G service. Why is this such a big deal? And why is it making my IT-focused brain race in overdrive? Especially when it comes to security?
Firstly, Amazon isn’t going to be a phone company. There’s no money in it for them. They don’t want to sell you service. Instead, they want you to buy devices from them that have SIM card slots to run a private 5G network. What kinds of devices have SIM card slots but aren’t phones? That’s right, industrial IoT! Amazon is betting that IoT is going to bypass traditional Wi-Fi based solutions entirely in favor of 5G connectivity going forward. It’s a very interesting play that opens up a huge market to companies that are wanting to take advantage of this flood of new systems that are going to be connected to the Internet without the need to deploy the Wi-Fi that we’ve come to know and love and trust.

The security side of my brain is also lighting up like Christmas lights because I know that bypassing the existing security controls that we rely on through Wi-Fi is going to create all kinds of hassles. You’re telling me that putting a smart device or an industrial machine on the Internet with a SIM card is going be safer than using something like WPA3? If this were an LTE setup I would absolutely say that this is a security disaster waiting to happen.
The Pillars of Security in 5G
The advent of 5G makes the security aspects of this problem a lot easier to deal with. I was able to attend a presentation from Betacom during Security Field Day and I learned a lot about how the security in 5G has been increased to help combat these issues. Here’s a great video from the session that you will want to check out:
Ravinder Jarral certainly knows what he’s talking about when it comes to 5G. The big takeaway for me is that 3GPP, the consortium that serves as the umbrella where new mobile technologies are developed, has done a spectacular job of recognizing the needs that modern mobile devices need to be secure.
5G is all about granular security controls for the devices and the network. The days of a solid, unbreakable perimeter are gone. We used to believe that if we could just keep the attackers at bay they would eventually go away. Instead, the data inside our networks and contained on our devices became so valuable to those looking to intrude that it was well worth it to break through the defenses on the outside. Once they managed to get inside the protection it was a free-for-all, due to the fact that older technology for mobility forced providers to create one policy for all devices connected to a network.
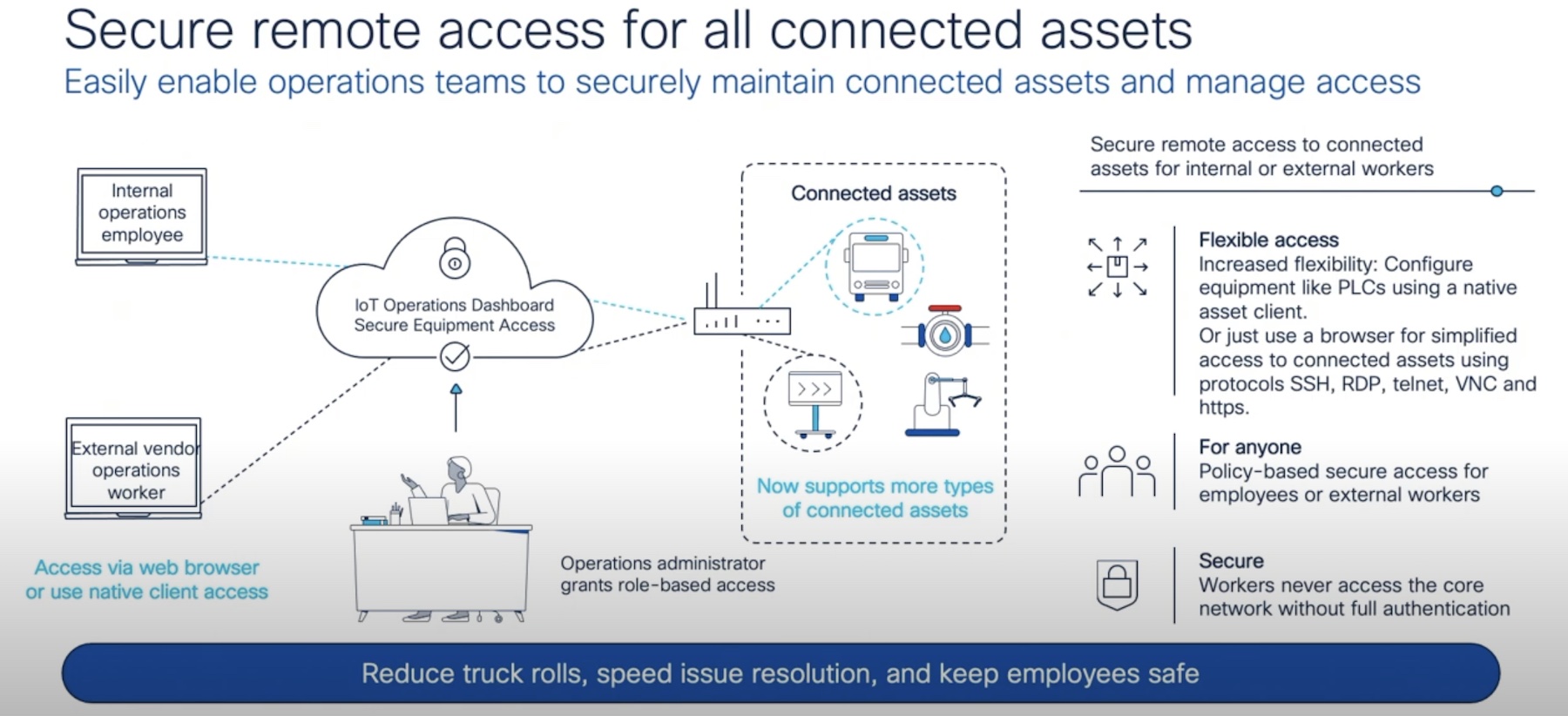
Today, 5G gives operators the ability to create policies per device or per device class. That means you can secure some super critical devices with a very restrictive policy while allowing other devices without data storage or ability to be compromised easily to a different class of access. Moreover, you can also assign security policies to the network as well, which gives you an additional layer of defense-in-depth that attackers will need to deal with when they try to get into your critical areas. Instead of just having a static, solid edge you have layers upon layers inside designed to keep attackers busy defeating your safeguards on a per-device basis.
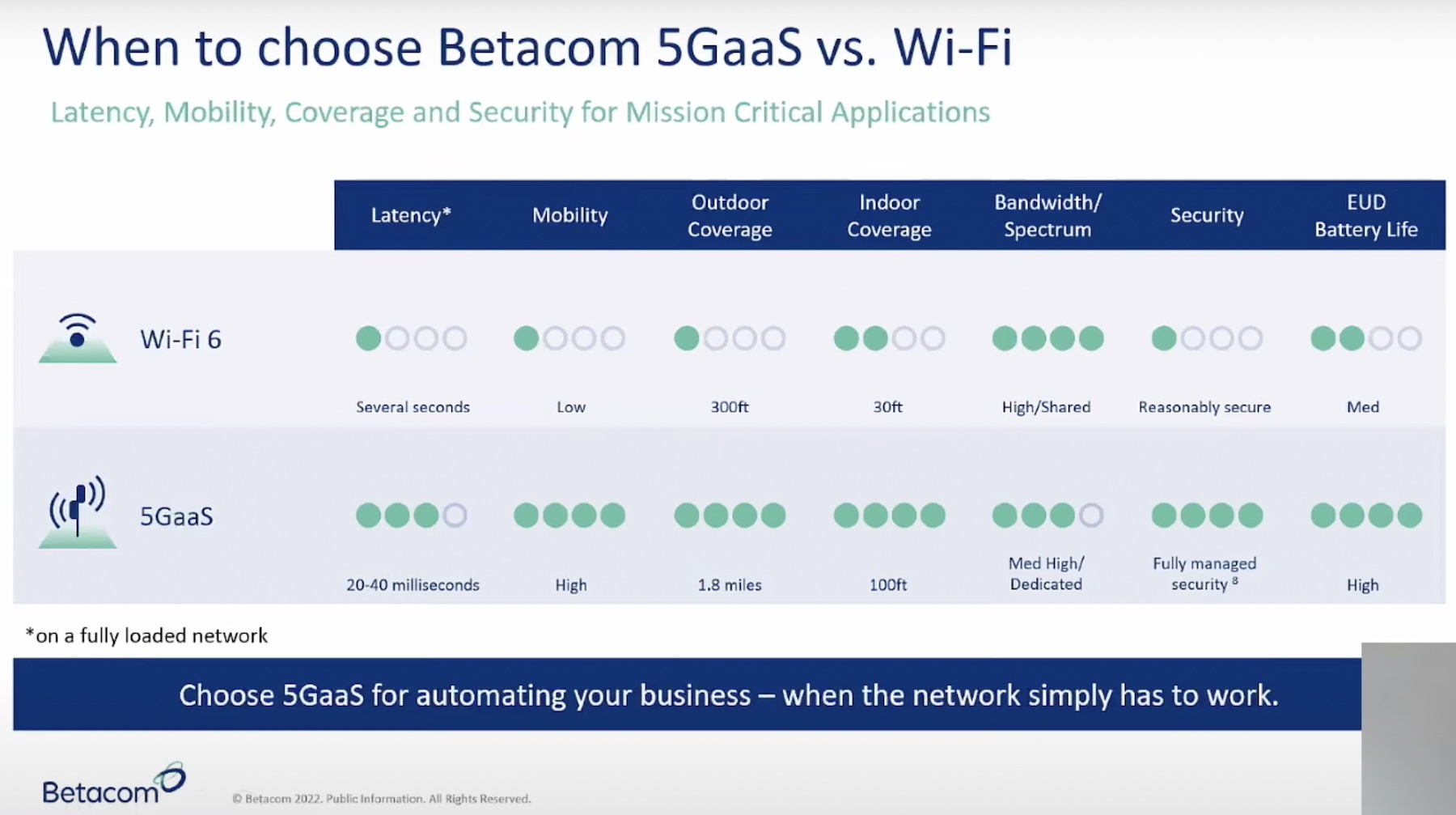
This all means that IoT devices leveraging 5G connectivity can be secured to a degree that we haven’t been able to do in a long time. That also means that IoT devices can gain a huge security advantage over other systems that use traditional Wi-Fi only. However, the number of devices that are being proposed along with the need to create more granular policies means more work for your security team if they don’t have a way to leverage tools to make the job easier.
Betacom Comes To the Rescue
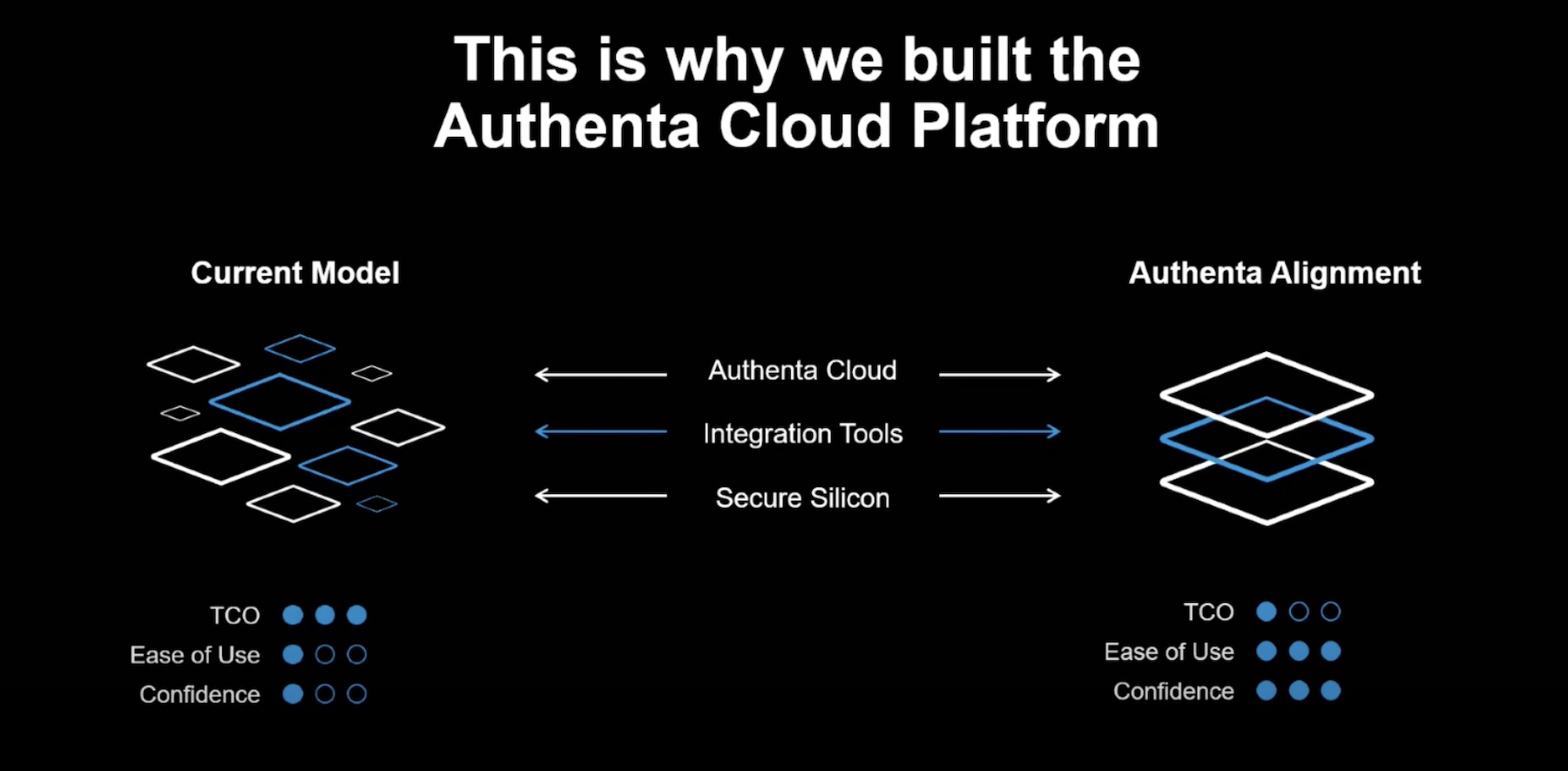
That’s where Betacom shines. Instead of having a monolithic structure like 3G and early 4G networks, 5G has essentially disaggregated the control and data planes from each other. That allows you to secure each separately, but it also allows you to put additional security controls in a separate layer to allow for more configurability of the various needs of the devices on your network.
Betacom has even developed an idea they call the Monitor Plane, which allows you to abstract the telemetry and security incident data from the 5G network to send to a different platform, whether one you operate or one that someone else operates for you. That distinction is a key point of their entire presentation. If you can abstract the control and data planes as well as the security controls you can provide all of that management through a service you can offer to customers that are looking to implement private 5G networks.
Betacom does just that with their 5G-as-a-Service offering that allows them to help you turn up and operate the network securely. While aimed at mobile devices like phones today I fully expect announcements like the one from Amazon to really start the push to have more and more IoT devices enabled with 5G radios to allow for always-on connectivity instead of building in a ton of existing Wi-Fi radios.
Bringing It All Together
You’re at the point right before the coming storm of 5G-enabled IoT devices. You will be dealing with these newly enabled systems in the near future if companies like Amazon can build up the support for them in your user base that they’re hoping. You need to have a plan in place for those inevitable suggestions that you enable an Amazon Private 5G network (or some other provider). And if you don’t have that answer right now you should look at having someone like Betacom help you solve it. Because they have the expertise and the knowledge you don’t right now. If you aren’t ready for 5G IoT that’s okay. But if you don’t reach out to someone that is ready you’re going to find yourself scrambling.
For more information about Betacom and their 5G-as-a-Service offering, make sure you check out their website at http://Betacom.com