Amidst the proliferation of high profile security breaches over the past few years a trend has emerged. The attack vectors that have been exploited in these attacks have largely been preventable. Sometimes a common piece of software was not patched in an appropriate amount of time. Other times it may be an IoT device that was not properly locked down and was accessible from the Internet with a default username and password. Regardless of the method of attack, the point remains that most of these breaches are due to a lack of strictly enforced security policy throughout the entire organization.
A Change in Attitude
With this trend in trend in high profile, and ultimately preventable attacks, most enterprises are seeing a shift in strategy when it comes to security. New projects and applications need to be designed with security as a key component, and not as a bolt on or a check box item that is addressed simply to satisfy auditors. Ensuring that policies are defined, and more importantly enforced, will ensure that access to resources is granted to only those who need it, activity is audited, and remediation of risks is addressed in a timely manner.
Adopting this “Security First” attitude is one thing, but actually executing upon it can be challenging. How do you ensure that policy is being enforced in all the platforms and endpoints across the organization? How can you manage enforcement at scale for applications that span on-premises, cloud, and mobile devices? It’s apparent that this is a challenge that is not easily solved and on that the enterprise must turn to a trusted partner to for help.
The Logical Next Step
I was recently briefed by Check Point Software Technologies and learned how their recent acquisition of Dome9 enables them to help customers adopt a security first mindset across their entire organization. Many are already familiar with Check Point and their history in the security space. They have been around for over 25 years, and although they got their start as a firewall company, they have expanded their portfolio to include multiple security products addressing on-premises, mobile, and cloud security challenges.
When I first heard about the acquisition of Dome9, I was curious how it fit into Check Point’s existing portfolio. After all, Check Point already had their Cloud Guard offering which is meant to protect both SaaS and IaaS services. Peter Alexander, Check Point CMO, described to me how the acquisition gave them a product that was complimentary to their existing portfolio.
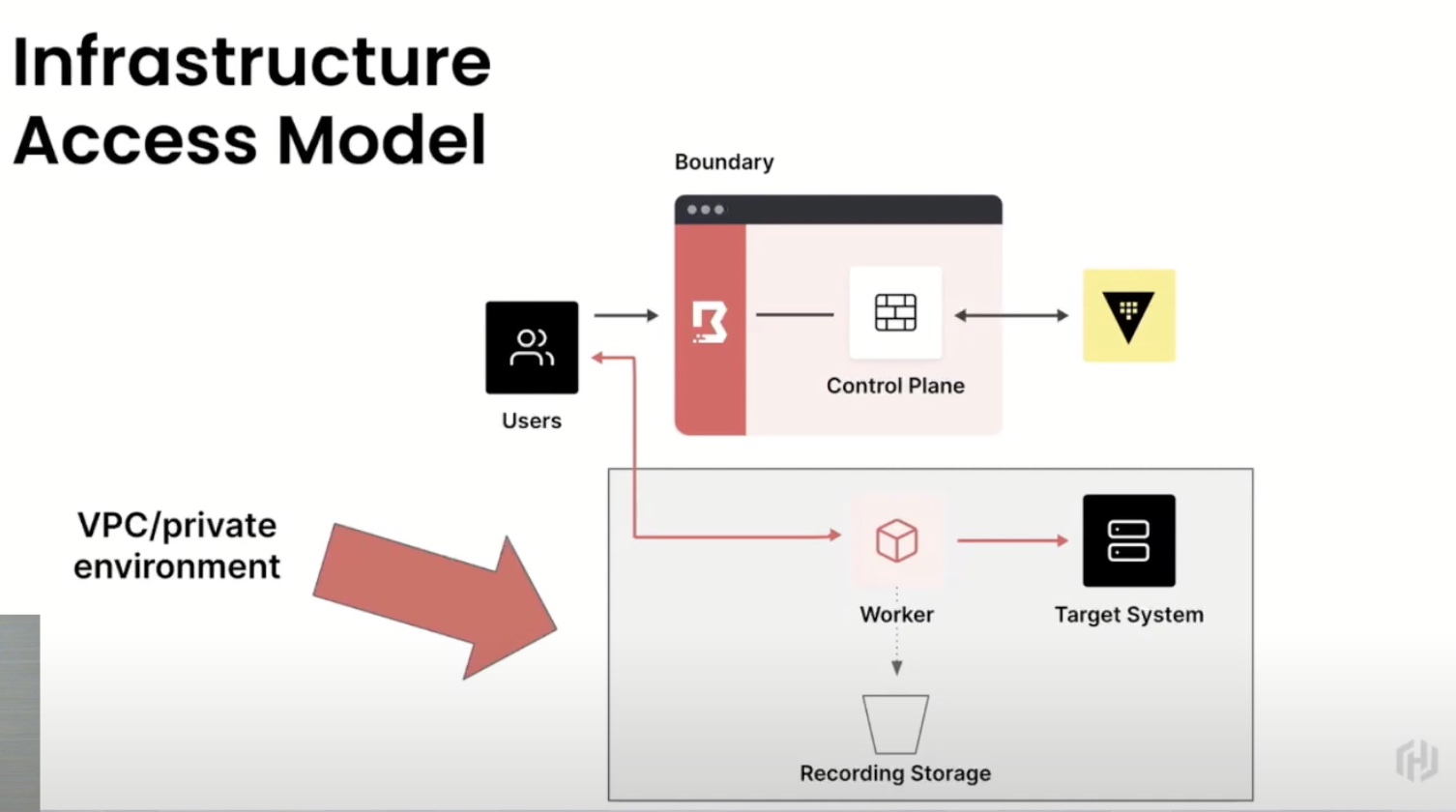
Automating a Security Tool is Important as Implementing It
Unlike many of the existing products in Check Point’s portfolio, Dome9’s main purpose is not to be the enforcer on the endpoint that blocks access on a specific VM port or stops the spread of a virus. Dome9 is an enforcer of policy across your entire cloud infrastructure. You can create policy’s that ensure the temporary access given to a contractor truly is temporary or that your S3 buckets will not be open to the entire Internet. Dome9 will automatically remediate any deviations from policy set and ensure compliance and governance of your applications and data.
This systematic and automated approach to security is what caught Check Point’s eye and eventually led to the acquisition. In order to adopt a security first mindset, the ability to define policy and automate are keys to managing at scale and making security a built in element of any workflow. Combined with Check Point’s existing portfolio, Dome9’s solution for cloud security allows customers to address all different aspects of their security posture from one vendor’s tools. Once Dome9 is integrated into Check Point’s Infinity offering, all security policies will be manageable from a single interface, thus reducing friction.
Ken’s Conclusion
The creator’s of the Internet themselves have admitted that it was not a platform that was designed with security in mind. It may have idealism that the Internet would only be used as a tool for good or simply a lack of understanding of the multitude of use cases for the revolutionary technology. Regardless, the reality is that security is table-stakes for any public facing application or service. Before a single line of code is written, an EC2 instance is spun up, or an S3 bucket is created, an application is designed and the security policy of that application must be part of that design. Furthermore, the enforcement of that policy needs to be automated to provide assurance that deviations will be remediated. All of this adds up to an acquisition that doesn’t just make sense, but was a necessary next step. Ensuring that customers can adopt a mindset to designing applications and infrastructure with security as a required component from the beginning will ensure that Check Point remain at the forefront of the security landscape.