We live in a world where data is transmitted back and forth all the time. We also live in a world where people want to get access to that data wherever they can. Things like bank account numbers, credit card info, or confidential patient data are all highly valuable. We’ve worked hard to secure the data when it is being transmitted with protocols like SSL and TLS. Once those were in place, attackers started looking for data hiding in the storage media. Now we encrypt data wherever it rests. But that’s still not enough.
Modern attackers have learned that data needs to be decoded to be processed. So advanced techniques can allow that information to be intercepted as it is read into memory and processed. Because of the nature of applications today there’s no real way to prevent this. If your system is reading data it is vulnerable to these kinds of memory-resident attacks. There doesn’t seem to be a way to protect the data, does there?

Enclave Building
Just a few years ago, the answer to that question would have been an unqualified “no”. However, thanks to the work of Intel we have an answer to this particular problem. The answer lies in Software Guard Extensions (SGX). Intel SGX allows security developers to build applications that create a secure enclave inside the CPU to execute programs in complete encrypted secrecy.
The approach is easy to understand. Intel SGX allows you to build partitions between your applications in memory. They are assigned access keys to the secured enclave inside the CPU. The hardware accelerates access to those area to prevent slowdown. Because the keys are per-application, you can ensure that only that application can access the data being processed there. The keys are also per-instance, which means that multitenancy doesn’t pose an issue for data leakage.
The data is encrypted at all times. Period. The data is stored in-memory in an encrypted format. The application can only decrypt the data in the secure enclave if it has a key to do so. That means the data is never anywhere in the wild in an unencrypted state. This is a massive change in the way we protect data. Instead of worrying about obfuscating it in transit or in storage, we only need to secure in while it’s being processed in a secure facility. Then we’re good. The data is returned encrypted and the world moves on.
Fortress Fortanix
Intel has built a great set of extensions with SGX. But in order to make it work someone needs to build a product on top of it. Today, the first product to come to market to take advantage of Intel SGX is Fortanix. They have built an entire platform around Intel SGX to ensure data is secured. Fortanix has two components to their solution: The Self-Defending Key Management System (SDKMS) and the Runtime Encryption Platform.
SDKMS helps you manage keys from across your environment. It’s a one stop shop for all kinds of KMS needs, such as public key infrastructure (PKI), SSL/TLS key management, or even encryption of data while at rest. For anything that doesn’t need to be encrypted at execution time SDKMS will take care of you. It’s licensed as an on-prem model for highly secured environments or as a SaaS model.
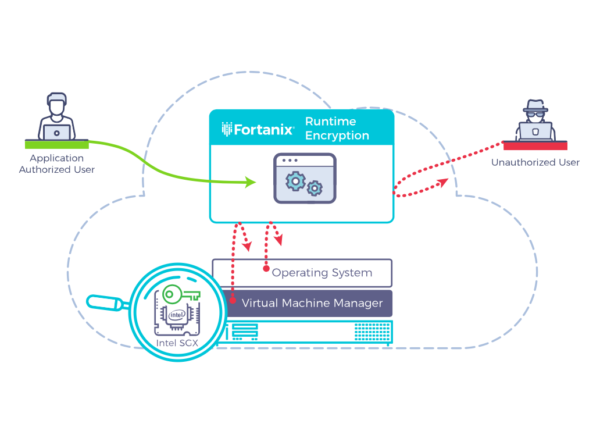
The real magic is with the Runtime Encryption Platform, though. This is the implementation of Intel SGX in the wild. With Runtime Encryption, Fortanix can productize Intel SGX with all the management capabilities you need to make it work for your environment. The Fortanix platform utilizes something called EnclaveOS to provide transparent encryption to existing applications. Because EnclaveOS can transparently handle the decryption process for you, there’s no need to rearchitect your applications to utilize Runtime Encryption.
Runtime Encryption can be deployed to any application. It can be set up to provide access in a variety of ways. A couple of my favorites are setting restrictions on time-of-day access and multiparty restrictions. Time-of-day is easy enough to understand. If you have data stored in a database you can only access and decrypt it in the enclave at certain times. Maybe that’s during the workday. Perhaps it’s during the evening shift. It could even be different times for different people.
Multiparty access is another huge advantage. There are some things that are so secret that they need to be protected at all times. They also need to be protected from an individual trying to access them. Think about the way nuclear missile silos used to work. You had to have two people with two different keys turn them at the same time. Moreover, they were physically separated so they couldn’t be turned by one person. The access method required two people working in concert. Fortanix has that capability built into the Runtime Encryption platform. Now, you cannot only ensure the confidentiality of data, but you can ensure that it takes two or more people to access it. That’s important for super secret things, like soda formulas or the medical records of celebrities.
Bringing It All Together
It was only a matter of time before we realized that the only way to make data secure was to make certain that it was never exposed in any way where it could be read. Intel and Fortanix have made this possible thanks to SGX and the platform built around it. The idea of keeping highly secured data inside a secure enclave is radical enough that it’s going to take time to catch on. But once companies see the value of being able to encrypt things completely without the need to use trickery with TLS, this is going to take off big time. Stay tuned to Fortanix for more greatness to come.