The best security practices are often not the ones that focus on protecting the crown jewels, but holistically everything inside the network. Zero Trust security is a big part of that, but the multi-cloud computing model introduces some baffling complexities in the game making it harder to connect all three of network, users, and applications in a fully secure fashion.
Last week at KubeCon 2022 in Detroit, we met with Ashher Syed, Product Marketing Lead at HashiCorp and talked about how HashiCorp is protecting authentication credentials and making the hybrid multi-cloud environment safe for its clients.
A Twofold Problem
Organizations’ security ambitions have become magnitudes more difficult since they’ve started down the hybrid multi-cloud road where workloads are in distributed environments and users and applications are linked via interconnects – a situation most ideal for data leaks. Even in a thought experiment, one can come up with a disturbing number of ways to exploit this setting. It’s not like companies are skimping on security solutions, but the problem of threats and risks still prevails.
Not helping with the problem are numberless nodes and clusters in the environments which make it hard to tell which is which. Although that is more of a problem of visibility than security, the two are intertwined in a fashion that if one is to be solved, the other needs figuring out too.
An Infrastructure for the Infrastructures
HashiCorp sees a way through with service mesh. The service mesh is an infrastructure layer that is designed to monitor and control the way data is communicated between applications. HashiCorp wields it to tackle both the problems of visibility and security in one shot.
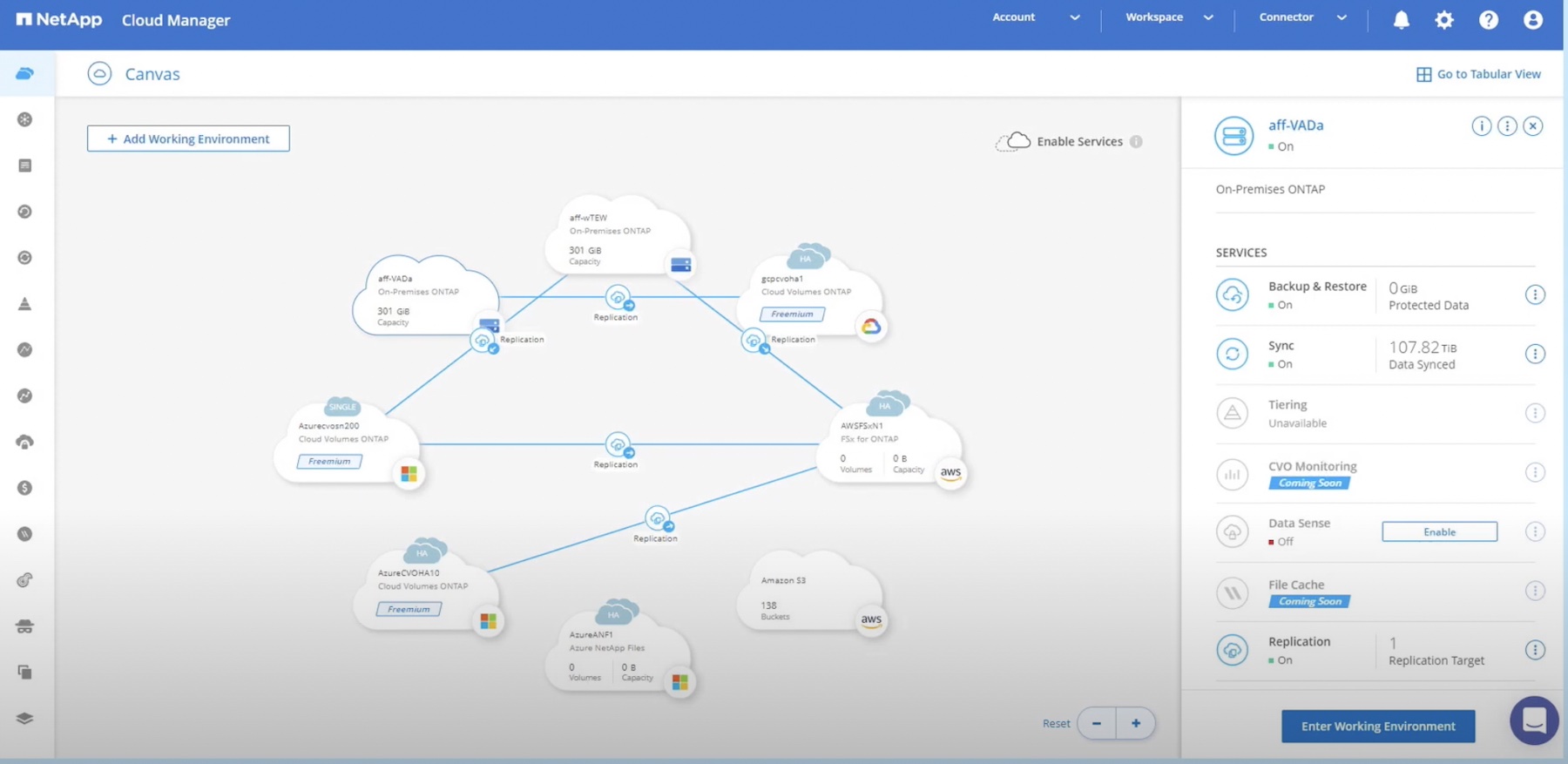
HashiCorp pieced together a multi-platform service mesh called Consul. The Consul provides a secure workflow between environments, that holds all workloads together in datacenters in multiple regions.
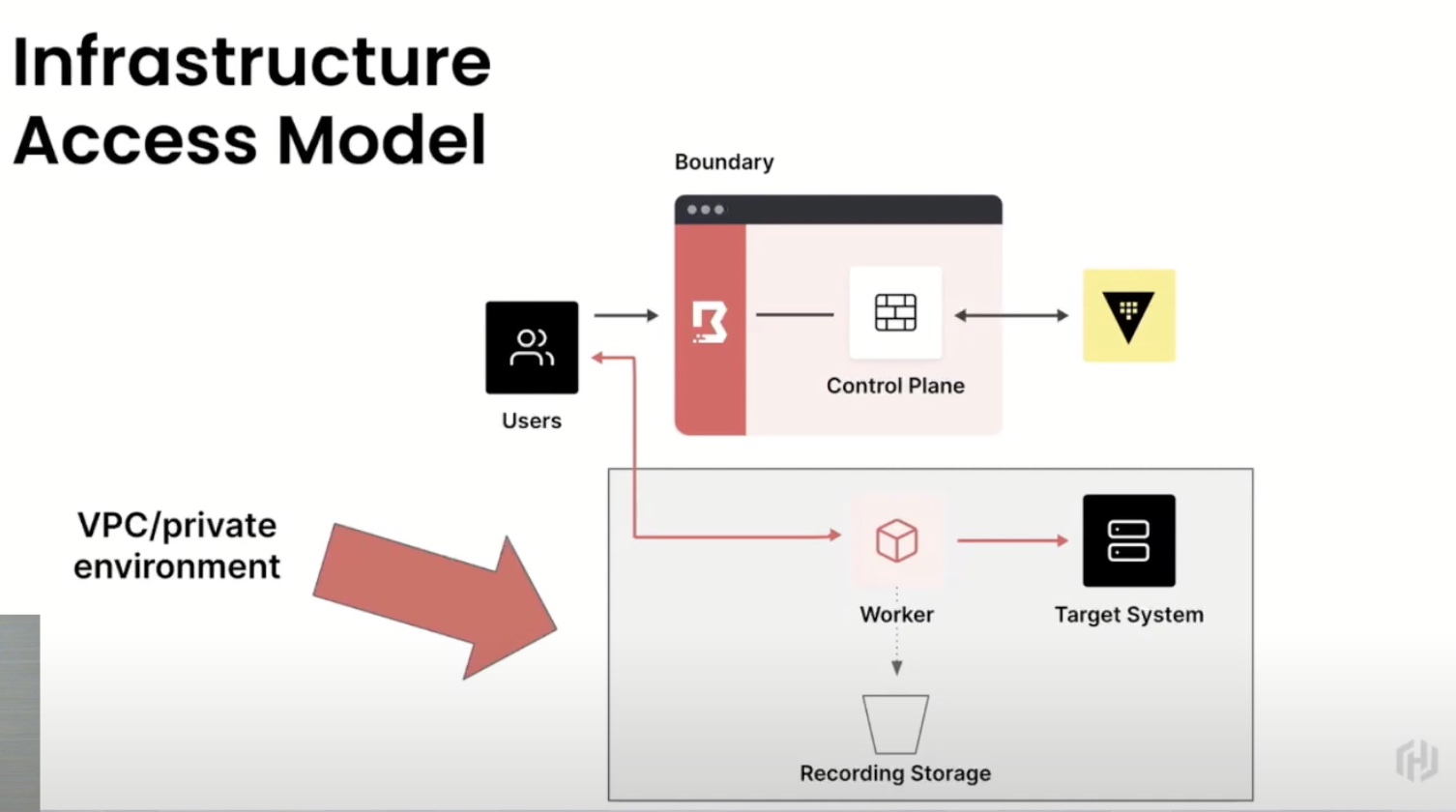
This also has a Zero Trust aspect to it. Under the banner, there are three products- the Consul, the Vault and the most recently released Boundary. Together they cover hybrid multi-cloud connectivity which is top of the list at present, zero trust security, the best way to provide users a safe passage to the applications, and automation for all Day 2 operational tasks. If this sounds ambitious, it’s probably because it is. In a normal situation, what would take armies of operators and support teams weeks to accomplish, the service mesh reduces down to numbered actions performed within minutes.
HashiCorp’s service mesh provides visibility into all Kubernetes workflows, and non-Kubernetes ones too – both inside the K8s environment and any VMs, ECS, EKS and GKE clusters.
Consul has built-in Vault integrations that allows for secure secrets management. Vault encrypts and saves all secrets generated by the secrets engine centrally inside it, instead of storing them in Kubernetes, where unencrypted, they are vulnerable to attacks. For good measure, all encryption keys are put on auto-rotation.
Consul is more than just a secure connection layer. Just on its own, it provides deep and wide observability in a scaled environment. Service discovery enables quick one-minute discovery of any new services on the registry. Users can look inside the clusters and out, and perform monitoring functions like health checks to find how well or not the services are working. By automating a lot of the accompanying networking works, it reduces time to deployment.
But when you factor in the capabilities of the other two solutions – the Vault and Boundary, Consul can accomplish even more on the security side of things. It relies on identity-based authorization which involves authentication, authorization and encryption of all traffic. Service to service encryption creates a hermitically sealed environment for the data packets to travel.
“Zero Trust from our lens is all identity driven. It starts from identity, and application identity brings all the guardrails for Zero Trust security in terms of authentication, authorization and encryption of all the traffic. Also, any secrets that you have, have to be time-bound, and you should be able to audit and log everything after the fact that you bring some data out of it and see if there are any bad actors out there,” says Syed.
Now and in the Future
As an active participant in the Kubernetes space, HashiCorp is constantly exploring trends and supporting the big K8s community out there. But it’s focused on network, users and application connectivity, not just for Kubernetes environments but others as well.
In things that are new, HashiCorp has a newly released Zero Trust stack which is all over the news. Syed informed that HashiCorp’s plans going forward is to focus on scaling Kubernetes operations. Another forward-looking project is the GAMMA or Gateway API for Mesh Management and Administration for Kubernetes initiative in which HashiCorp is involved.
Wrapping Up
Today’s businesses don’t operate in just one cloud, but scale across multiple cloud infrastructures. For that, security is a top concern. With a service mesh, there’s a clear opportunity to consolidate disparate tools for which the Consul is a versatile solution. But the trick is having the right set of tools, and HashiCorp has a great Zero Trust stack that makes it possible to enforce a high level of security and build a safe hybrid multi-cloud space for users and applications.
Check out the full interview above. Keep an eye out for more interesting interviews coming up next, straight from the floor of KubeCon 2022.