How do you approach security? Do you think about the world as a nefarious place filled to the brim with bad guys just looking to disrupt your business and ruin your life? Or do you see security as a necessity that you can manage through clever use of tools and policies that helps you keep the worst offenders out and makes life easier for your employees? The answer might depend entirely on what kind of company you work for and how they look at the statistics they’re collecting about intrusions and such.
Visibility In The Dark
You have to know what’s going on before you can start to build a proper security strategy. According to Matt Cauthorn, VP of Security at ExtraHop, enterprises are seeing over 5,000 daily security alerts each day. Those alerts tend to pile up and take over three months to be looked at and resolved. That lack of ability to discern events, coupled with the amount of time they are unaddressed, means that exactly 0% of respondents in a recent survey were satisfied with their security monitoring solution. I would have though even 1% would have made sense, but Matt told me that they couldn’t find anyone that had confidence in what they were using.
Part of the issue stems from the perspective of security monitoring companies. They believe they have built the perfect framework to detect and deal with incidents. The only thing they’re missing is the data that will populate the system and reveal the truth about what’s going on. They build the system before they know what they’re looking for because they know how intruders operate and how to stop them. It’s much like a scientist believing beyond the shadow of a doubt that a hypothesis is correct even before the first experiment produces data.
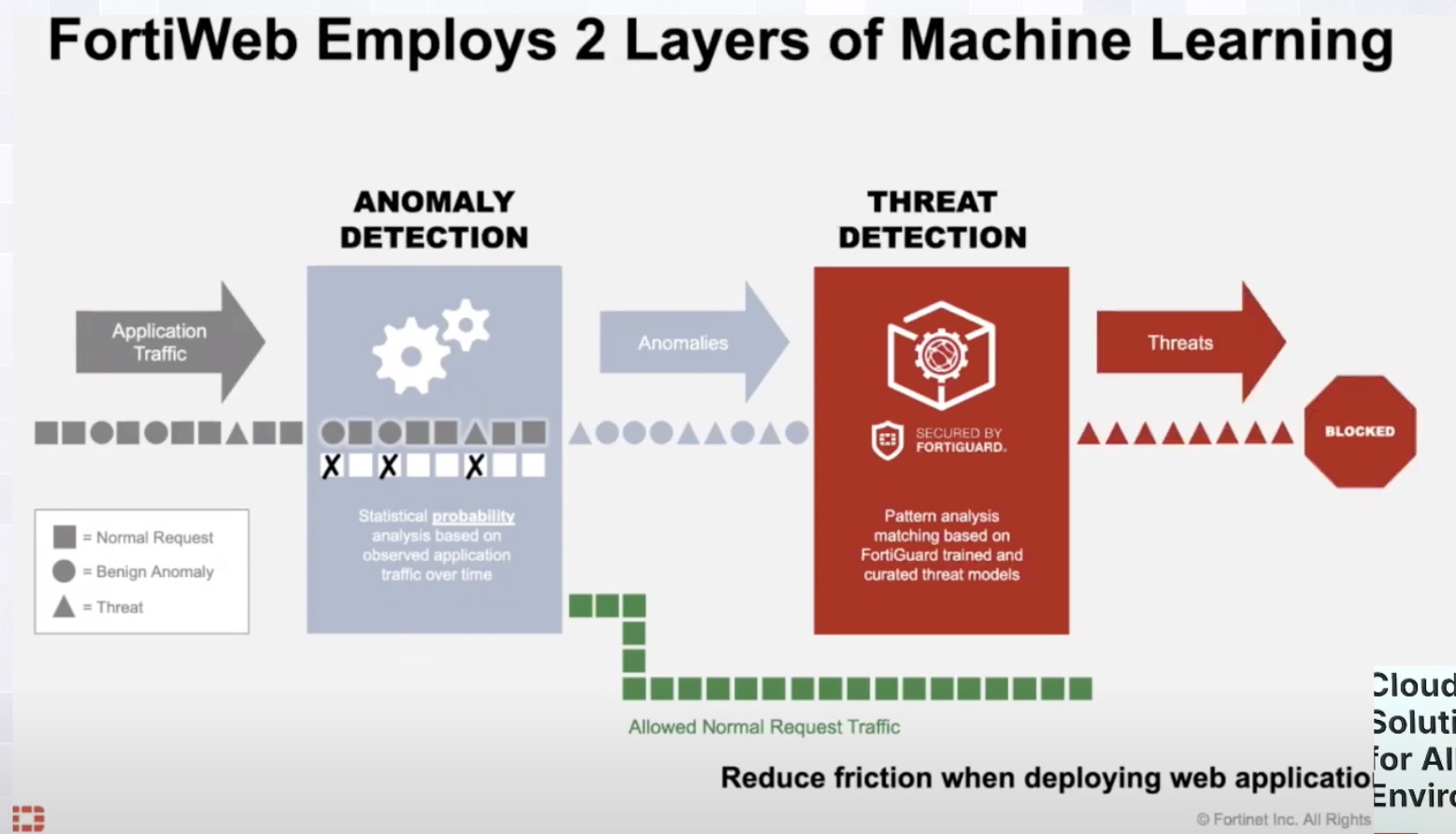
Network monitoring companies, like ExtraHop, take a slightly different approach. They collect the data first. They build a framework to collect data across the network and put it in a central place. Once there, the data can be analyzed for patterns. Collecting the data in this manner helps to reduce the likelihood of missing some of the views that you might take if you were only focusing on security. It also ensures that data is analyzed completely instead of sampling and hoping that your sample size or location is good enough to get the data you need.
Revealing The Light

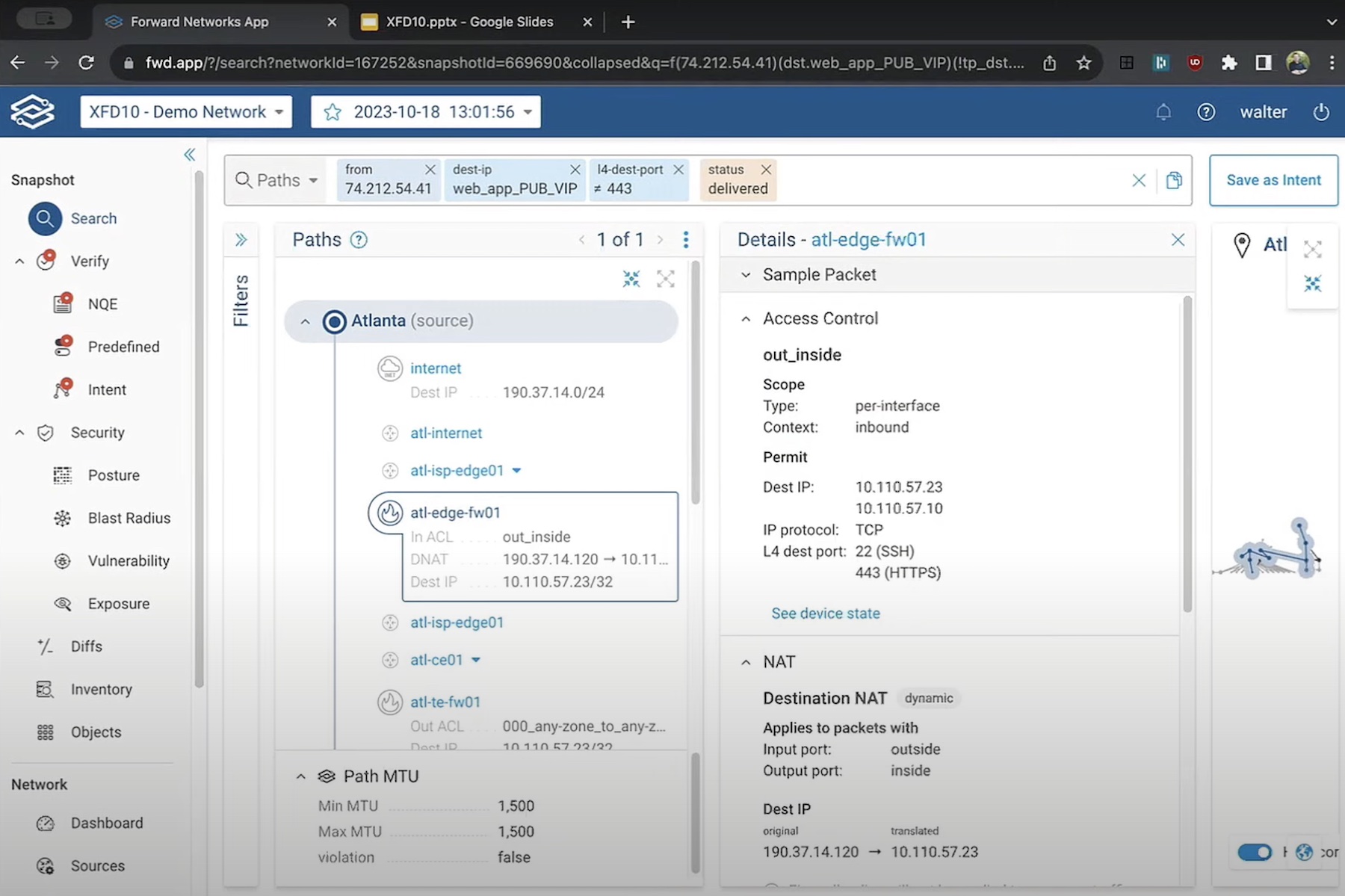
ExtraHop announced a new product called Reveal(x) at the end of January that offers to do a lot of the things that security monitoring tools need to do. Reveal(x) collects the data and processes with which machine learning algorithms. This means that it can find patterns long before human eyes would ever get a chance to notice what was going on. It can also fine tune the data collection to notice aberrant behavior that occurs after certain actions, like accessing systems outside normal parameters and doing directory enumeration.
Armed with that knowledge, Reveal(x) can give you the option of stopping the behavior or monitoring it more closely. That allows you to collect the kinds of information that would necessary to take legal action against intruders and secure your system from similar attacks in the future.

Reveal(x) can also offer advanced technologies like payload decryption, SIEM integration, and robust reporting options. Those features are offered in a three-tier licensing structure that gives you the features you need at the start and positions the more advanced technologies where larger, more complicated enterprises can take advantage of them with different models.
Bringing It All Together
Reveal(x) solves the problem with security monitoring solutions that are perfect except for that pesky data. Instead of building a platform that operates in a vacuum ExtraHop built a great solution that utilizes their existing networking monitoring expertise to start collecting data about security incidents as well. Given that background, they were then able to apply advanced analytics to help weed out false positives and give administrators the peace of mind needed to focus on what’s important in the monitoring system and make it easier to take care of the problems before they happen.