Qlik's rebranding is more than a new look, it's a statement. Data analytics has penetrated...
Exclusives
Gestalt IT Exclusives are original long-form posts written by the Gestalt IT team and published here first. Exclusives are highlighted in our weekly Gestalt News email. Sign up today, or follow us on Twitter!
Kubernetes, Beyond the Hype with Jon Hildebrand
Kubernetes is said to be the go-to tool for all of IT. In this Gestalt IT Tech Talk, host Stephen...
Busting the Silo Mentality with DevOps with Matthew Allford
DevOps, if adopted right, can end years of productivity issues in IT. In this Gestalt IT Tech Talk...
Understanding Data Sovereignty with Nathan Bennett
Data sovereignty is one of the burning issues of our time. In this Gestalt IT Tech Talk recorded at...
Shifting Left to Cast a Wide Safety Net with Leon Adato
There is a growing consensus that security needs to shift left in the software development...
Meet Jon Hildebrand, Senior Product Architect at 11:11 Systems
Stephen Foskett sits with Jon Hildebrand to discuss the prevalent misconceptions surrounding...
Meet Mike Bolitho, Wireless Engineer
Meet Mike Bolitho, a wireless engineer for a major medical company. He sat down with Tom...
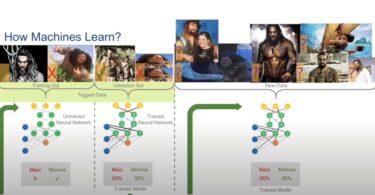
The Custom Silicon Race, with The Futurum Group CEO Daniel Newman
Tech companies are one-upping each other in the custom silicon game. In this Gestalt IT Tech Talk...
Aligning IT and Security to Drive Long-Term Organizational...
In this Ignite Talk from Edge Field Day, Sulagna Saha discusses Brian Knudtson's presentation on...
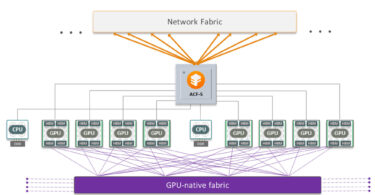
A Different AI Networking Focus with Enfabrica
Building networks for AI is expensive. What you need is a way to better utilize your GPU resources...
Overcoming Cognitive Biases Standing in the Way of Professional...
In this Ignite Talk article from the Edge Field Day event, Sulagna Saha reviews Jim Czuprynski’s...
Generative AI – Risks and Rewards with Gina Rosenthal
In this Ignite Talk article from Edge Field Day, Sulagna Saha discusses Gina Rosenthal's...
The Truth behind SaaS Data Recovery with W Curtis Preston
With most SaaS services used in businesses, backup and recovery is a rare addition. In this Gestalt...
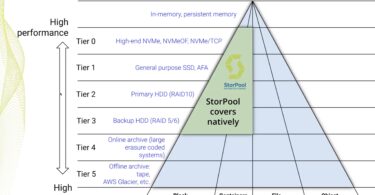
StorPool Tightens Data Protection in StorPool v21
In this exclusive article, Sulagna Saha discusses StorPool's plan to tighten data protection with...
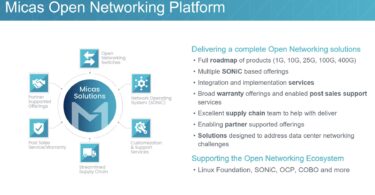
Transitioning to Open Networking, One Step at a Time, with Micas...
In this exclusive article, Sulagna Saha discusses how Micas Networks is helping businesses...